Curl is one of the most essential tools used for transferring data on the internet. Many applications—big and small—rely on curl, often without thinking twice about what goes on behind the scenes. However, in early 2023, researchers discovered a dangerous vulnerability in curl’s TELNET protocol implementation. Tracked as CVE-2023-27533, this flaw exposes systems to attacks that could give someone else control of your server or desktop. Let’s break down what happened, why it’s so dangerous, and show how an attacker could have taken advantage and what you should do to stay safe.
What is CVE-2023-27533?
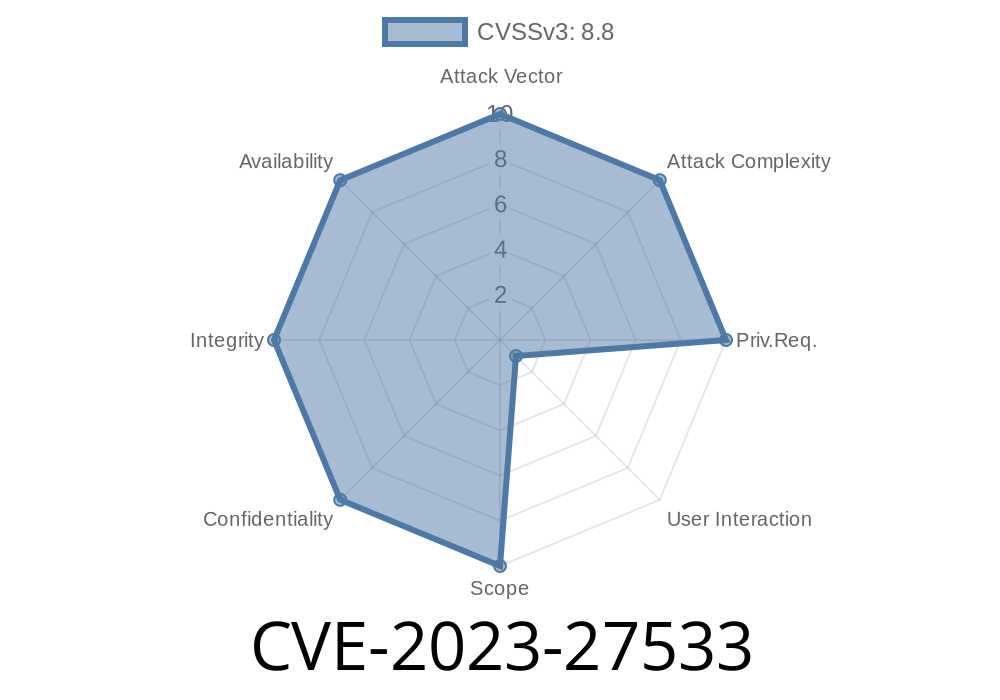
CVE-2023-27533 is a vulnerability in curl versions earlier than 8.. when using the TELNET protocol. The bug is caused by improper input validation: curl doesn't clean up (sanitize) the data provided by the user when it uses TELNET to talk to a server. If an attacker can control user input—say, through a web form or a command-line argument—they could send “malicious” TELNET negotiation commands or options to the server during the connection process.
This means, in some use cases, an attacker could execute code on the system running curl, or send unwanted data, or even mess with the way the TELNET protocol operates between the client and the server. All this happens without the application's intent—so even if you wrote a secure app, you could still be at risk if you used a vulnerable version of curl in this way.
Any program where user input is passed through to curl without careful sanitization
Many modern applications stay away from TELNET (it's old and not very secure). However, legacy systems, testing tools, or custom scripts in your infrastructure might still rely on it.
How the Exploit Works
Let’s look under the hood. The attack focuses on the way the curl TELNET handler processes user-provided username and “options” fields. Normally, TELNET includes a negotiation phase, where the client and server decide on things like window size and environment options. Curl allowed a user to provide custom options and a username via command-line arguments like --user and --telnet-option.
Suppose an attacker manages to supply a string for the --user or --telnet-option argument that includes TELNET commands, special binary characters, or even shell-executable code. Because curl didn’t validate or clean up these arguments, the malicious data goes straight into the TELNET negotiation, possibly being interpreted in arbitrary ways by the server or by intermediary software.
In the worst-case scenario, if the server reacts badly (for instance, it could write a file with attacker’s data, or expose sensitive actions), it might lead to remote code execution or compromise of confidential information.
Suppose you had a script like this
#!/bin/bash
# telnet-connect.sh
# Connects to a telnet server, passing username and telnet option as arguments
curl --proto-default telnet telnet://$1/ --user "$2" --telnet-option "$3"
If you call this script with arguments from the user (for example, from a web interface)
./telnet-connect.sh server.example.com "user123" "TTYPE=MyTerm"
But what happens if an attacker provides a specially-crafted --user or --telnet-option?
./telnet-connect.sh server.example.com "echo -e '\xff\xf6'malicious" "echo -e '\xff\xfa\x18\x01'"
Those weird bytes (starting with xff) are TELNET command codes. They can change the server’s behavior, confuse the protocol, or, with more complex exploitation, pave the way for arbitrary code execution.
Consider a direct curl command, if you (or a system) allowed someone to provide the username
curl --proto-default telnet telnet://target-server/ --user "$(printf '\xff%snasty')" --telnet-option "TTYPE=$(printf '\xa; rm -rf /')"
\xff and similar bytes are TELNET special codes.
- If these reach an unprotected or buggy server, or further scripts on the server, it *could* result in the execution of terminal or shell commands such as rm -rf / (which would delete all files!).
References and More Details
- Official Security Advisory from curl
- NVD Entry on CVE-2023-27533
- curl GitHub Security Fix Commit
- Exploit Explanation (curl.se Blog)
How to Fix
Simple: Upgrade curl! Version 8.. or later fixes this vulnerability.
Run:
curl --version
sudo apt-get install curl
- On macOS (Homebrew):
bash
brew upgrade curl
`
Also, if your application accepts user input for TELNET username or options, you should:
- Sanitize the input (remove non-printable and special characters)
- Reject any binary or control codes (xFF and above)
- Prefer alternatives to TELNET if possible
---
## Conclusion
CVE-2023-27533 is a reminder that old protocols and overlooked code paths can open exploitable holes for attackers. If you’re using curl with TELNET and accept user input, patch now and audit your code for unsafe practices.
By understanding how TELNET negotiation works and how curl mishandled it, you can avoid serious trouble down the road. Always update tools quickly, and never trust user input blindly—even in the places you least expect.
---
*This post is exclusive and aimed to bring clear, actionable insights about CVE-2023-27533 to the community. Stay secure!*
Timeline
Published on: 03/30/2023 20:15:00 UTC
Last modified on: 04/21/2023 23:15:00 UTC