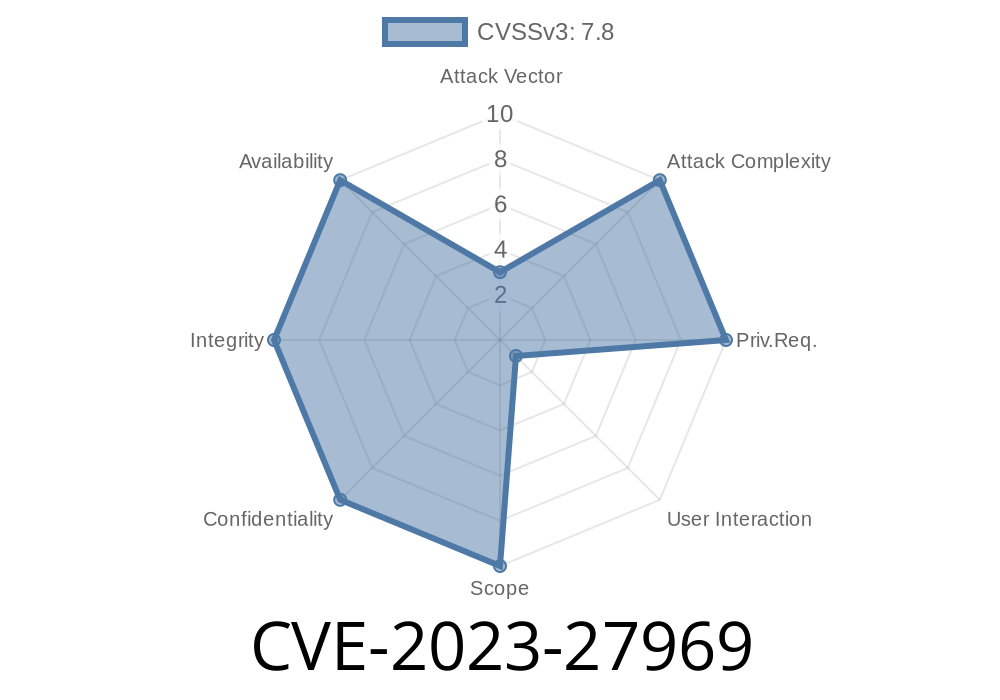
In early 2023, Apple released patches for a critical vulnerability tracked as CVE-2023-27969. This issue affected Apple’s macOS Ventura, iOS, iPadOS, watchOS, and tvOS. The vulnerability, a classic "use after free" bug, could let a malicious app execute arbitrary code with kernel privileges, potentially compromising the entire device.
tvOS 16.4
Below, we'll break down what a "use after free" is, see how an attacker might exploit this flaw, show a simplified concept exploit, and detail what Apple changed.
What is a "Use After Free"?
A “use after free” happens when software frees (releases) a chunk of memory, but later keeps using it even after it’s supposed to be gone. If an attacker manages to control or change the data now in that freed memory, they can trick the program into executing code of their choice— sometimes even inside the protected "kernel" of the OS.
How Was CVE-2023-27969 Discovered?
While specifics about Apple’s internal bug-finding are private, this kind of flaw often surfaces via fuzzing (testing with random inputs) or thorough code audits. Apple's security advisory credits "an anonymous researcher" with reporting it.
A Simplified Look at the Vulnerable Code
Imagine the kernel has a function that allocates memory for an object used by apps. If the kernel frees this object but, due to a race or logic bug, continues to use it, that’s a “use after free.” The attacker can quickly reallocate memory in between, controlling what’s in the space the kernel is about to use.
Here’s a simplified version
// Pseudocode inspired example
typedef struct {
int id;
char *buffer;
} ImportantStruct;
void kernel_handler(UserInput *input) {
ImportantStruct *obj = allocate_object();
// ... do some stuff ...
if (input->free_flag) {
free(obj);
}
// Oops: still using obj after it’s been freed
do_something(obj->buffer); // <-- Use after free!
}
If an app can set free_flag, it can force the object to be freed, but the kernel will still act as if it’s valid — a classic use-after-free bug.
How Does the Exploit Work?
1. Trigger the Flaw: An app sends data that causes the kernel to free a target object, but then the kernel accesses (uses) the same object again.
2. Heap Spraying: The attacker fills memory with controlled data, hoping their data gets placed where the freed object was.
3. Take Over: When the kernel uses the freed slot, it’s using attacker data — which could be a pointer to malicious code.
4. Privilege Escalation: Because this happens in privileged (kernel) code, the attacker can now run code as the OS itself, bypassing all security.
Example Exploit Concept
Here’s a conceptual outline (not a working exploit!) of how such attacks usually go in userland code:
// 1. Allocate the object
int handle = allocate_kernel_object();
// 2. Free it in a way the kernel doesn't expect
trigger_free_in_kernel(handle); // The bug: kernel uses after free
// 3. Replace freed memory with malicious payload
heap_spray_with_fake_object(malicious_code_ptr);
// 4. Kernel runs code with attacker's pointer
// If successful: kernel jumps to malicious code
Real-world exploits, especially in the Apple kernel, are much more complicated, with kernel address randomization and security sandboxes to defeat.
References
- Apple Security Update Advisory: https://support.apple.com/en-us/HT213670
- NIST National Vulnerability Database: https://nvd.nist.gov/vuln/detail/CVE-2023-27969
- Apple Platform Security (on kernel): https://support.apple.com/guide/security/kernel-security-sec23230df6a/web
- Overview of Use-After-Free: OWASP Use After Free
Takeaways
- If you use Apple devices, keep your system up to date. This bug allows for serious attacks if unpatched.
- CVE-2023-27969 is a reminder that deep OS bugs can linger for years — always test and audit code, and patch quickly when fixes are out.
- Developers: Always avoid dangling pointers and be careful with memory management — especially in privileged code.
Stay safe, and patch your devices!
For more info on recent Apple security issues:
🌐 Apple Security Updates
Timeline
Published on: 05/08/2023 20:15:00 UTC
Last modified on: 05/15/2023 15:39:00 UTC