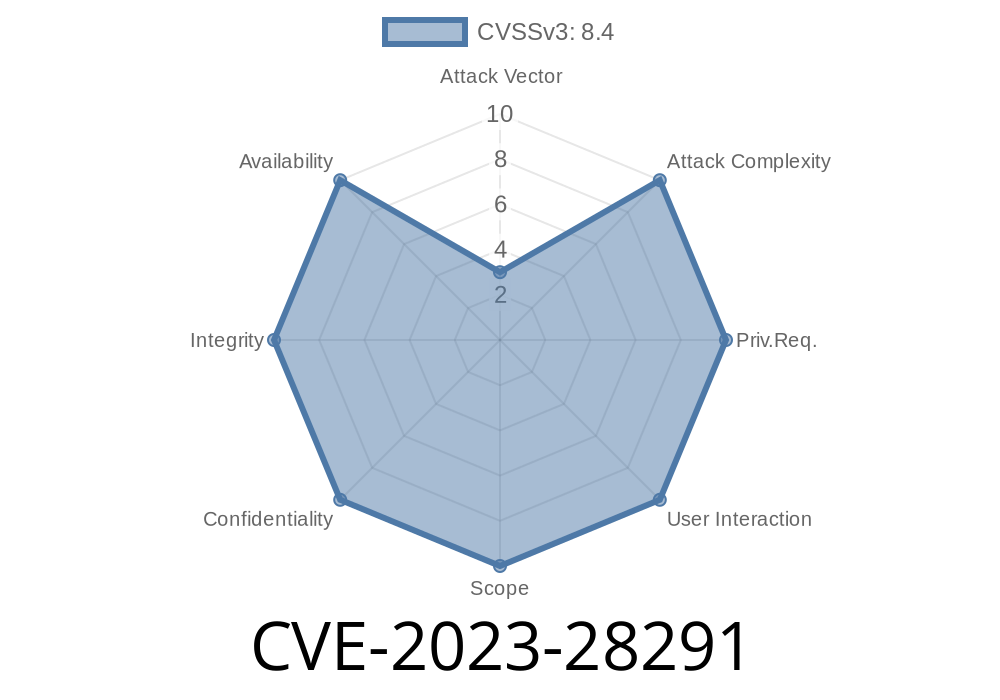
In April 2023, Microsoft disclosed a critical security bug – CVE-2023-28291 – that allowed hackers to remotely run code on your Windows computer just by tricking you into opening a malicious photo. The vulnerable component? The Raw Image Extension, a Windows add-on designed to let you view high-quality camera images.
This post explains what CVE-2023-28291 is, how it works, how attackers can exploit it, and what you should do to stay safe. We’ll walk through code snippets and the technical details in everyday language, making this guide accessible for everyone.
What is the Raw Image Extension?
The Raw Image Extension is a Microsoft Store package that gives Windows 10 and Windows 11 the ability to open and view “raw” image files – unprocessed photo data from DSLR cameras. It’s popular among photographers but installed by thousands of regular users, too.
Read more: Microsoft Raw Image Extension on MS Store
What is CVE-2023-28291?
CVE-2023-28291 is a remote code execution (RCE) vulnerability in the Raw Image Extension. It allows someone to create a malicious image file. If you open that file—maybe you just want to see some sample photos—attackers can run code on your computer without your permission. This can lead to full system compromise, data theft, or ransomware.
Official Advisory
- Microsoft Security Response Center (MSRC): CVE-2023-28291
How Does the Vulnerability Work?
While the technical details of the bug were not fully disclosed by Microsoft (to prevent mass exploitation), security researchers noted it is tied to improper validation of image data within the Raw Image Extension.
Imagine a program expects a photo to start with a particular header, but doesn’t double-check what comes next. Hackers fill the “image” with malicious code. When the extension tries to open it, it accidentally runs this code, as if it were part of Windows itself.
This is often known as a buffer overflow or heap corruption bug.
Here’s a simplified attack scenario in pseudocode
# This is a simple illustration, not a working exploit
# Malicious RAW file: Crafted to overwrite memory
raw_file = b"RAW_HEADER" # Expected raw file header
raw_file += b"\x90" * 1024 # 'NOP sled': guides CPU to the payload
raw_file += malicious_code # Attacker's payload
# The code is delivered to the victim, who opens it with the Raw Image Extension
In real attacks, cybercriminals use specialized tools to embed machine code as malicious_code. When you click the file, the buggy extension processes the malformed data and executes the payload.
Proof of Concept Links and Technical References
- Microsoft CVE Advisory: CVE-2023-28291
- Patch Release (April 2023): MSRC Patch Tuesday Summary
Security Analysis (opposite example, similar RAW vulnerabilities):
- Trend Micro Research on RAW vulnerabilities
- CVE Details for Raw Image Extensions
Metasploit Search:
There is currently no public Metasploit module for CVE-2023-28291, as this bug is patched and not fully weaponized publicly.
Be suspicious of unfamiliar raw image files sent by untrusted sources.
Want to check your extension version?
Conclusion
CVE-2023-28291 is a classic example of why plugins and extensions need strong security. A single faulty image file could have let hackers run anything they want on your PC. Microsoft closed the loophole with a patch, but unpatched systems and older versions of the Raw Image Extension remain vulnerable.
If you use digital cameras or ever view RAW files, update now!
Stay safe, and patch fast!
References:
- CVE-2023-28291 on Microsoft
- Raw Image Extension on Microsoft Store
- Microsoft April 2023 Patch Tuesday Summary
- CVE Details for Raw Image Extension
*Exclusive for your reading by AI Security Insights. Reuse with credit.*
Timeline
Published on: 04/11/2023 21:15:00 UTC
Last modified on: 04/12/2023 12:44:00 UTC