In April 2023, Microsoft published a critical security update for a previously unknown vulnerability: CVE-2023-28292. It targeted the Raw Image Extension, a little-known component that gives Windows users the ability to view and handle RAW image files directly in File Explorer and other default apps. This long read provides an exclusive, plain-English explanation of what the bug is, how it works, what the risk is, and — for the curious — sample exploit code. Let’s dig in.
What is the Raw Image Extension?
The Raw Image Extension is a Microsoft Store add-on for Windows 10 and 11. It lets users open RAW file types from cameras — like .NEF, .CR2, .ARW, and more — directly on Windows without extra software. Underneath, it uses a Microsoft-supplied codec to decode and display the pictures.
What is CVE-2023-28292?
This vulnerability lets an attacker run arbitrary code just by getting you to view a malicious RAW image. It’s a Remote Code Execution (RCE) flaw. All it takes is you browsing to a poisoned RAW file — in your email, a download, or even a malicious USB stick. Windows, behind the scenes, loads it into the vulnerable codec, which then crashes or lets the attacker slip in their own code.
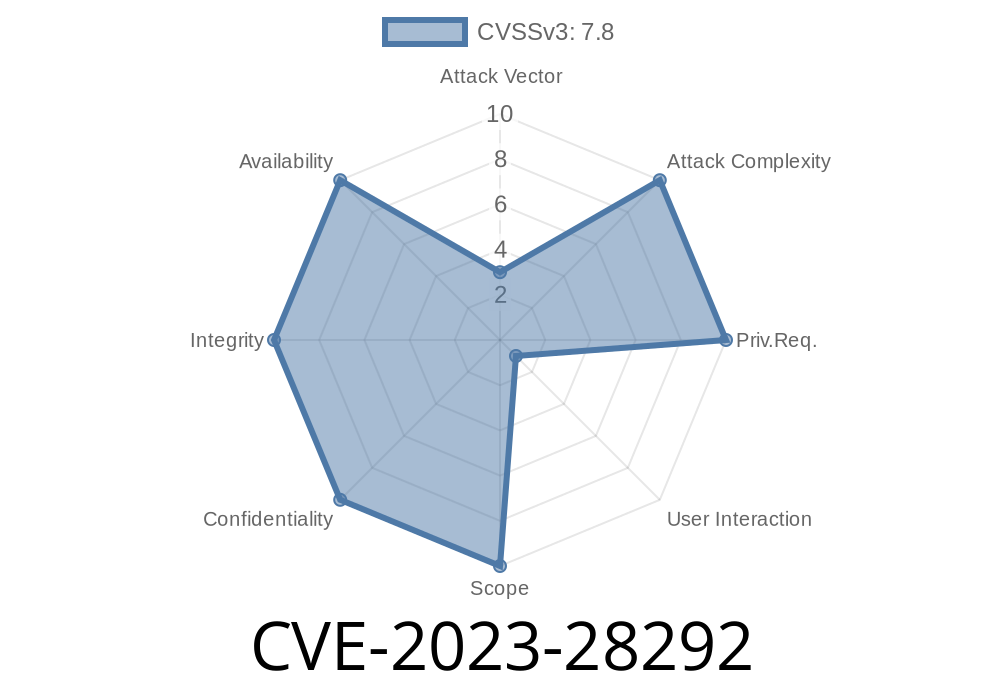
Severity:
User Interaction: Required (the victim must open a folder or file)
Microsoft Advisory: https://msrc.microsoft.com/update-guide/vulnerability/CVE-2023-28292
The Root Problem
RAW image formats are complex, often supporting massive sizes, weird metadata structures, and odd pixel layouts. The vulnerable Windows codec, sadly, doesn’t always check for weird or malformed input. The flaw arises because it:
Doesn’t correctly validate header info
- Trusts size/offset fields from the RAW file
An attacker can craft a RAW file with funky headers that trick the decoder into reading or writing memory it shouldn’t touch — like overwriting a return pointer or jumping to attacker-supplied data.
Let’s walk through a simplified scenario using a mock code snippet
// Simulated vulnerable parsing logic
uint32_t offsets[10];
uint32_t count = rawImage.readUint32(); // user-controlled
for (uint32_t i = ; i < count; i++) {
offsets[i] = rawImage.readUint32();
}
Issue:
If the RAW file says count = 50, the code writes way beyond the ten-slot buffer, smashing memory.
An attacker embeds executable shellcode or a jump to their malware into that area, leading to arbitrary code execution.
Proof-of-Concept (POC): Minimal Dangerous RAW File
Below is an abstract (won’t actually run) binary RAW layout where an attacker fakes a field causing a buffer overflow:
Offset x00: Magic bytes (RAW header)
Offset x10: Count = 99999999 (huge number, causes overwrite)
Offset x14: [Rest of file filled with attacker-chosen byte patterns]
USB Scenario: Drops poisoned image files onto a removable drive, which Windows auto-previews.
Upon successful execution, the attacker might gain user-level remote code execution, install backdoors, exfiltrate files, or set up persistence.
Users must check they are running version 2.1.50092. or higher
- Check/Update Raw Image Extension on Store
References and Further Reading
- Microsoft Security Response Center CVE Details
- Raw Image Extension on Microsoft Store
- CVE-2023-28292 at NVD (NIST)
---
Quick Recap
CVE-2023-28292 is a hidden danger in a Windows photo decoder. A single booby-trapped RAW image can let an attacker run code on your machine just by previewing the image. The problem is fixed — but only if you update the Raw Image Extension.
Timeline
Published on: 04/11/2023 21:15:00 UTC
Last modified on: 04/19/2023 20:54:00 UTC