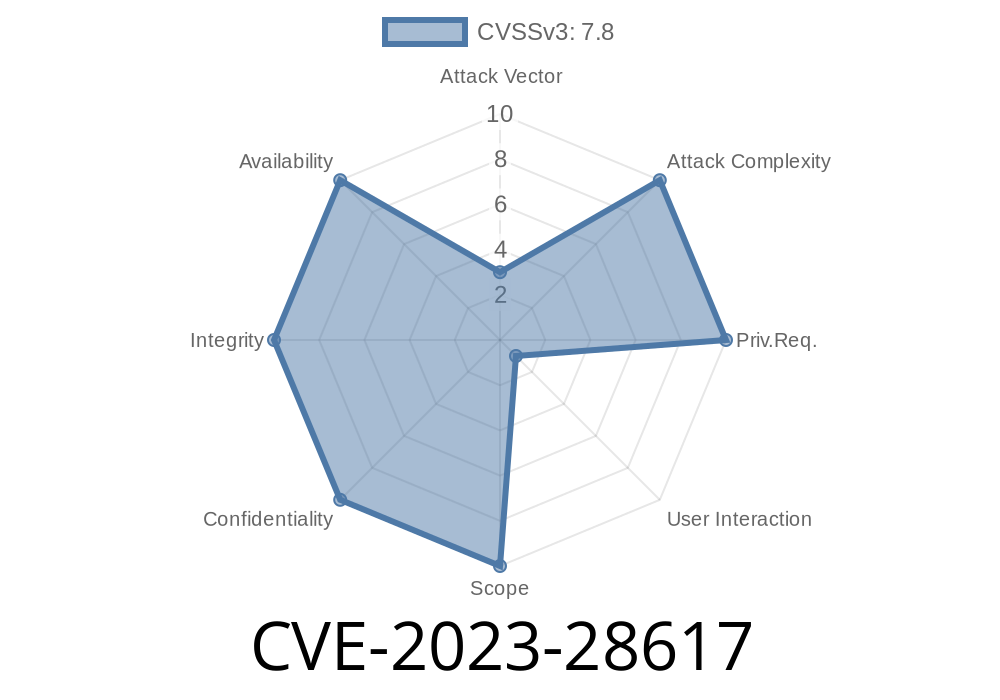
In June 2023, security researchers found a critical vulnerability in the popular Org Mode package for GNU Emacs: CVE-2023-28617. This bug concerns the function org-babel-execute:latex, used for running LaTeX code blocks within Org documents. Attackers could exploit weak filename handling to run arbitrary shell commands, putting users and their systems at risk.
Let’s break down what happened, how the exploit works, and how you can protect yourself.
What is Org Mode and Babel?
Org Mode is a flexible note-taking and organizing system designed for Emacs. One of its coolest features is supporting embedded code blocks—called "babel"—which can be written and executed in dozens of languages. ob-latex.el is the Emacs Lisp module that adds LaTeX support.
In Org files, users can add LaTeX code like this
#+begin_src latex
\LaTeX\ is fun!
#+end_src
And then execute it with Babel to generate outputs (like PDFs or images).
The Vulnerability: Command Injection via Malicious Filenames
The function org-babel-execute:latex makes use of user-supplied file and directory names to build shell commands for running latex, dvipng, or other tools. If the filename or directory name included shell metacharacters (like ;, &, |, $(), etc.), those would be passed *directly to the shell*.
Here’s the problematic code snippet from ob-latex.el (simplified for clarity)
(let ((cmd (format "latex %s.tex" basename)))
(shell-command cmd))
If basename is controlled by an attacker and contains dangerous shell characters, the shell will treat them as commands, not filenames.
Example exploit
Suppose an attacker can create a file or directory with the name
$(touch /tmp/hacked)
When you run Babel execute, it constructs a command like
latex $(touch /tmp/hacked).tex
Result: the shell runs touch /tmp/hacked *before* trying to run LaTeX. This means any shell command could be run just by naming a file or directory cleverly.
`sh
mkdir '$(touch /tmp/pwned)'
cd '$(touch /tmp/pwned)'
What happens:
The org-babel-execute:latex function builds and executes the latex command using the directory name. The shell expands $(touch /tmp/pwned), so now you have proof of execution:
`sh
ls /tmp/pwned
What can happen:
If you run Org files (yours or from someone else) in directories with weird names, or process files given to you by an attacker, they can execute *any* command on your computer.
Why it’s dangerous:
Sometimes Org files are shared for documentation, academic work, or online projects. If you work in a shared directory (like on a file server or git repository), attackers could slip in a malicious folder or filename.
Official References
- CVE Record: CVE-2023-28617
- Org Mode Commit Fix
- Emacs Org Babel Latex Security Discussion
Example (safe) replacement
(call-process "latex" nil nil nil (expand-file-name (concat basename ".tex")))
Now, shell metacharacters in the filename aren’t interpreted; they're passed as literals.
Upgrade Org Mode to version 9.6.2 or later.
- Be wary of Org files and directories with strange names, especially if shared or downloaded from untrusted sources.
- If you must use an older Org version for some reason, always manually check the filename/directory path before running code blocks.
Conclusion
CVE-2023-28617 is a classic example of command injection in shell calls—made worse by the powerful automation features beloved by Org Mode users. Always double-check how your software handles user input, especially when constructing shell commands!
If you use Org Mode for LaTeX, update immediately. For hackers and security enthusiasts, this is a textbook case of why escaping—or better, *not* using the shell at all—is critical for code safety.
Timeline
Published on: 03/19/2023 03:15:00 UTC
Last modified on: 05/10/2023 01:15:00 UTC