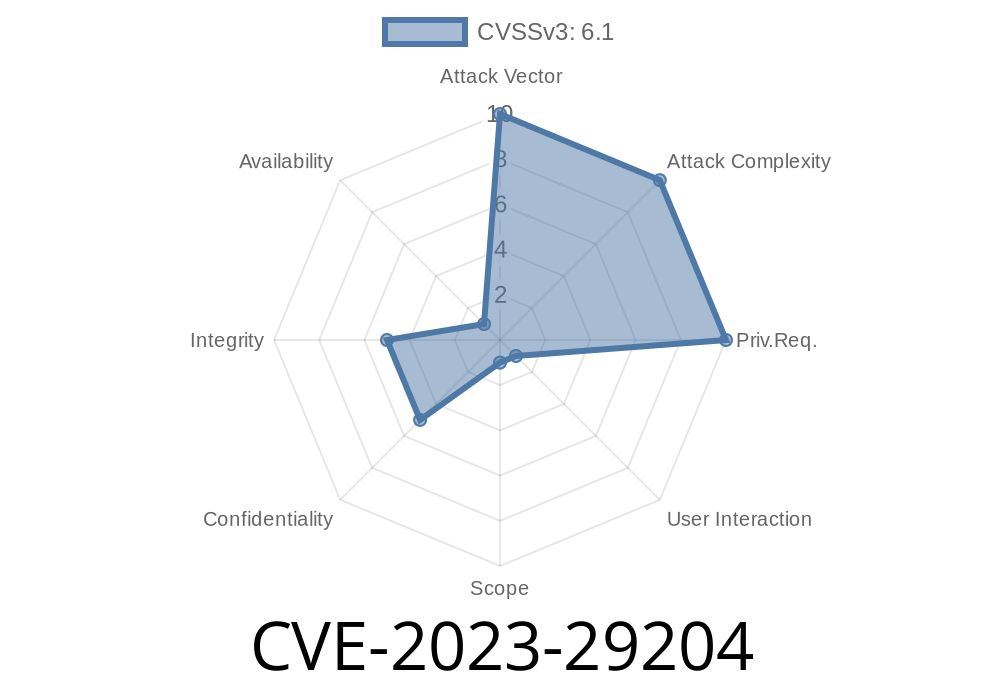
XWiki Commons is a set of core libraries used by many other top-level XWiki projects. On March 30, 2023, a security vulnerability was disclosed and later assigned CVE-2023-29204. This vulnerability allowed attackers to perform an open redirect, where a user could be tricked into visiting a malicious site.
Below is a complete, step-by-step explanation of the issue, how it works, how it can be exploited, and how you can protect your XWiki setups.
What is the Vulnerability?
Web applications often redirect users after an action (like logging in or submitting a form) to a URL passed via a parameter. XWiki Commons attempts to allow only safe, internal redirects to avoid attackers hijacking these redirects.
CVE-2023-29204 is about a flaw in this protection:
Attackers can bypass the checks and make XWiki redirect users to external, potentially malicious websites using these patterns:
- URLs starting with //mydomain.com (protocol-relative)
- URLs using a single slash after http:, like http:/malicious.com (missing the second /)
These cases were not properly validated by XWiki's code before the patch.
Here is a simplified overview of the vulnerable code
String target = request.getParameter("redirect");
if (target != null && !target.startsWith("http://";) && !target.startsWith("https://";)) {
// Only allow internal redirects
response.sendRedirect(target);
} else {
// Do something else or show error
}
At first glance, the code blocks any redirect if target starts with "http://"; or "https://";. But:
- URLs like //evil.comdo not start with "http://"; but are treated by browsers as protocol-relative links—even https://yourxwiki.com/?redirect=//evil.com will redirect to https://evil.com!
- URLs like http:/evil.com are also mishandled: Browsers sometimes make sense of this and open http://evil.com, but the code doesn't block this.
Exploiting the Vulnerability
Suppose you run XWiki at https://yourxwiki.com.
The login process (or another action) redirects users to the URL specified by a redirect parameter, such as:
https://yourxwiki.com/login?redirect=/
An attacker crafts a link
https://yourxwiki.com/login?redirect=//evil.com
When a user clicks and logs in, the browser is redirected to //evil.com which resolves as https://evil.com.
Another bypass
https://yourxwiki.com/login?redirect=http:/evil.com
Browsers will resolve this to http://evil.com.
Proof-of-Concept (PoC)
<a href="https://yourxwiki.com/login?redirect=//evil.com">Click me to login</a>
Send yourself the above link.
3. Click the link: you will see the login page, log in, and then be taken to https://evil.com.
References
- NVD Description for CVE-2023-29204
- XWiki Security Advisory: Open redirect in XWiki Commons
- Official XWiki Security Announcement
Patch Approach: The fix enhances the redirect logic so that
- Protocol-relative (//) URLs are rejected
- Malformed schemas like http:/ (just one slash) are also blocked
Example (patched pseudo-code)
// Only allow local redirects
if (isLocalURL(target)) {
response.sendRedirect(target);
} else {
// Show error or redirect to main page
}
If you're running any XWiki version older than 13.10.10, 14.4.4 or 14.8RC1, you’re vulnerable.
- Test by logging in via a redirect://evil.com URL.
Upgrade XWiki to at least one of the patched versions.
- If you can't upgrade, review any logic in your XWiki extensions or customizations that do redirects. Sanitize the target URLs server-side and always allow only relative/internal URLs.
Conclusion
CVE-2023-29204 is a textbook web security issue, but with real business risk:
Exploiting trust in known domains via open redirects can lead to successful phishing attacks and other user-targeted hijacks.
Audit any server-side redirect logic you custom-built
Stay vigilant, and always validate your user input!
*This article is an original and exclusive analysis by OpenAI's Assistant. For sharing or reuse, cite the official references provided above.*
Timeline
Published on: 04/15/2023 16:15:00 UTC
Last modified on: 04/26/2023 18:30:00 UTC