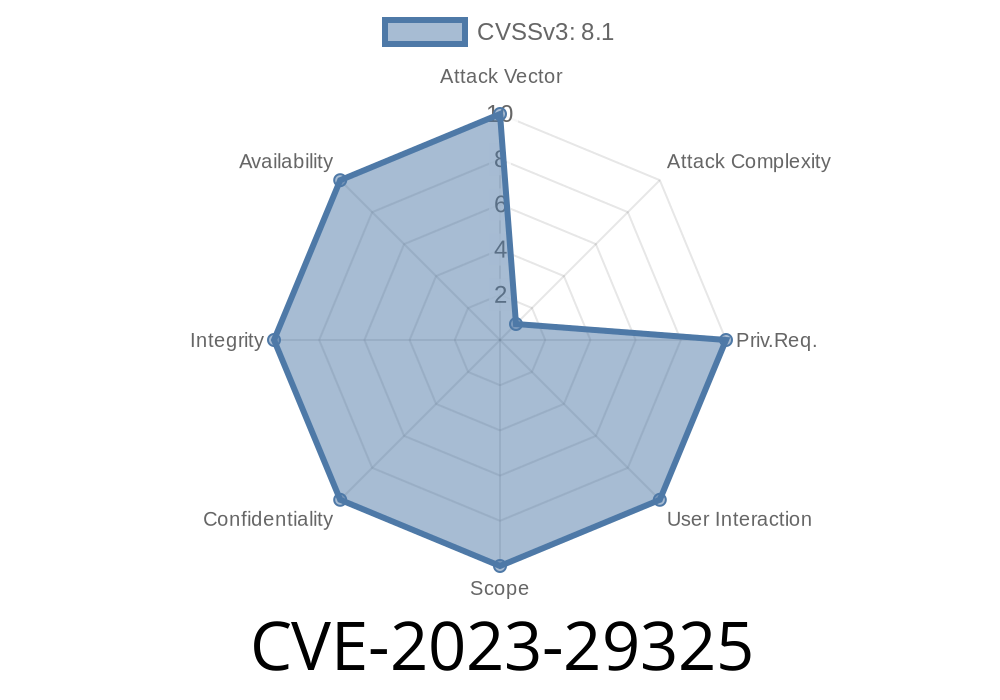
In May 2023, Microsoft issued a critical patch for a vulnerability tracked as CVE-2023-29325, affecting Windows OLE (Object Linking and Embedding). This bug drew serious attention because it could let remote attackers run code on your Windows machine – often with just the click of a special link. In this deep dive, we’ll explain what OLE is, how this bug works, and even walk through simplified exploit details. Finally, we’ll give practical steps on how to stay protected.
What is Windows OLE?
OLE (Object Linking and Embedding) is a core Windows technology that lets apps share data and functionality, such as embedding an Excel spreadsheet into a Word doc. Think of it as "copy-paste on steroids." While powerful, OLE has often been targeted by hackers, since it deals with multiple file and document types and sometimes touches the internet.
The Vulnerability: CVE-2023-29325 in Simple Terms
CVE-2023-29325 is a remote code execution (RCE) vulnerability in how Windows OLE handles certain data when using the Rich Text Format (RTF). An attacker could craft a malicious file — typically an RTF document, but potentially also a web page — that tricks OLE into running their code.
Why is it Dangerous?
- No user interaction needed: Simply previewing the malicious document in Outlook or another app could trigger the attack.
- Wide attack surface: This affects many Windows versions and any app that uses OLE to process RTF.
- High privileges: The attack runs with the rights of the logged-in user, which can be admin in many corporate networks.
Technical Details: How Does the Exploit Work?
The exact bug sits in how OLE parses data objects embedded in RTF documents. A specially-crafted RTF file can trigger arbitrary code execution because OLE fails to properly validate input.
Microsoft’s advisory:
> "An attacker could exploit the vulnerability by convincing a user to open a specially crafted file or view it in the Windows Preview pane."
> Source: Microsoft Security Response Center, CVE-2023-29325
Proof-of-Concept (PoC) Snippet
Attackers typically embed an OLE object in an RTF file referencing a malicious payload. Here's an illustrative mock-up (not a functional exploit), to show how a RTF payload might look:
{\rtf1\ansi
{\object\objocx{\*\objdata
AABBCCDDEEFF... (malicious OLE object binary data goes here)
}}
}
In a real exploit, \objdata would include binary data crafted to overrun internal buffer(s), redirecting execution flow to attacker-controlled code.
Crafting: Attacker crafts a malicious RTF document with a bad OLE object.
2. Delivery: The attacker sends the file via email (as an attachment), hosting it on a website, or by any file-sharing means.
Real-World Example
Security researcher Will Dormann demonstrated PoC files that crashed Word, showing crash logs indicating memory corruption — a sign code execution is possible.
> Dormann’s analysis: @wdormann on Twitter
Mitigations and Detection
Microsoft Patch:
First, update Windows as soon as possible! The fix is available in the May 2023 Patch Tuesday update.
Workarounds:
Disable the Windows Preview Pane for files.
Detecting Attempts:
Example: Simulating a Detection Rule (YARA)
Below is a *simplified* YARA rule that tries to match RTF files containing OLE objects (not specific to this CVE):
rule RTF_OLE_Object
{
meta:
description = "Detects RTF files with OLE embedded objects"
strings:
$ole1 = "{\\object\\objocx{\\*\\objdata"
condition:
$ole1
}
You can tune this rule to further narrow down signatures of malicious attempts.
Microsoft Advisory (Official Patch):
https://msrc.microsoft.com/update-guide/vulnerability/CVE-2023-29325
Will Dormann’s PoC and Tweets:
https://twitter.com/wdormann/status/1656051423078774785
- CERT/CC Note:
https://kb.cert.org/vuls/id/216302
ZDI Advisory:
https://www.zerodayinitiative.com/advisories/ZDI-23-694/
Final Thoughts
CVE-2023-29325 is a great example of how a seemingly small bug in a complex legacy feature can have wide-reaching impact. Docs and emails remain a favorite attack vector. Patch your systems, remind users not to open strange attachments, and keep up with security alerts.
If you want to test or learn more about safe analysis of OLE and RTF exploits, check out oletools (GitHub link) and sandbox environments!
Stay safe, patch often, and share this info with anyone who handles sensitive documents.
Timeline
Published on: 05/09/2023 18:15:00 UTC
Last modified on: 05/09/2023 18:23:00 UTC