XWiki is a powerful open-source wiki platform used by a broad range of organizations. In April 2023, a serious security issue was discovered: CVE-2023-29508. This vulnerability allowed users without script rights to trigger a stored cross-site scripting (XSS) attack, thanks to a logic flaw in the Live Data macro within XWiki Commons. Below, we’ll break down exactly what went wrong, show how the exploit worked, and highlight how to secure your wiki.
What Is CVE-2023-29508?
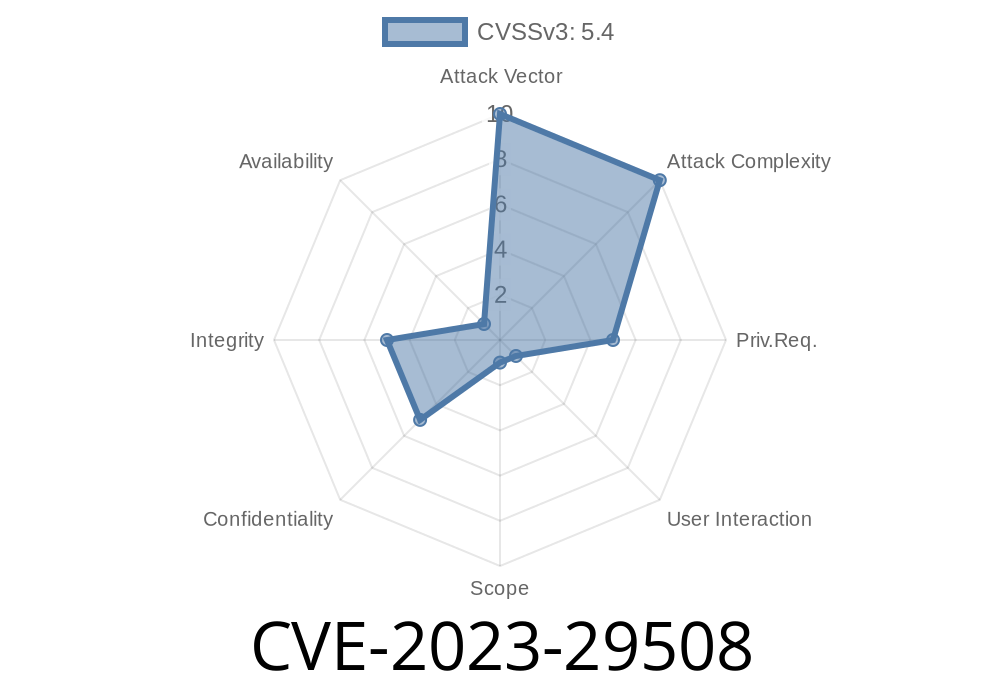
CVE-2023-29508 is a privilege escalation and stored XSS bug in XWiki - official advisory. The issue affects the "Live Data" macro found in the XWiki Commons library, which many XWiki projects rely on.
In simple terms:
Even if you deny users the 'script' permission, they might still inject dangerous JavaScript that gets stored and executed, *if* the last person to edit the page did have script rights.
User with Script Rights edits a page and saves it.
2. User without Script Rights edits the same page and injects Live Data macro content that contains malicious JavaScript (using the macro’s configuration).
3. When anyone views the page, the injected script executes, since the rendering engine trusts the previous "last author"’s script right and doesn't properly check the current content author.
Key flaw:
Security checks depended on the last author’s rights, *not* on the actual editor who injected the dangerous code.
How an Exploit Might Look
Suppose a user, Alice (without script rights), edits a page authored last by Bob (who *does* have script rights). Alice adds the following in WYSIWYG editor:
{{liveData dataSource="url" columns="name,description"}}
{{/liveData}}
But she tweaks the columns parameter like this
{{liveData dataSource="url" columns="name,"><img src=x onerror=alert('XSS')>"}}
{{/liveData}}
Or in more raw form (inside the macro’s configuration)
<macro class="LiveDataMacro">
<parameter name="columns" value="name,description,<img src=x onerror='alert(Hacked!)'>" />
</macro>
When the macro renders, the <img> tag runs its injected JavaScript.
XWiki 13.10.11
The patch fixes security context checks in the Live Data macro to ensure only users with 'script' rights can inject code that will be interpreted as executable scripts.
Patch references
- XWiki Jira Issue XWIKI-20661
- GitHub Commit
References
- Official Jira Advisory - XWIKI-20661
- GitHub Patch Commit
- XWiki Release Notes 14.10
- National Vulnerability Database Entry
Upgrade now and review user privileges to keep your wiki safe.
If you use or administer XWiki, now’s the time to patch — don’t get caught out by this simple, dangerous, yet easily preventable bug.
*This post is crafted exclusively for readers seeking clear, direct security guidance on XWiki CVE-2023-29508. For detailed developer notes, consult the official issue tracker and patch commits. Stay safe!*
Timeline
Published on: 04/16/2023 08:15:00 UTC
Last modified on: 04/26/2023 13:12:00 UTC