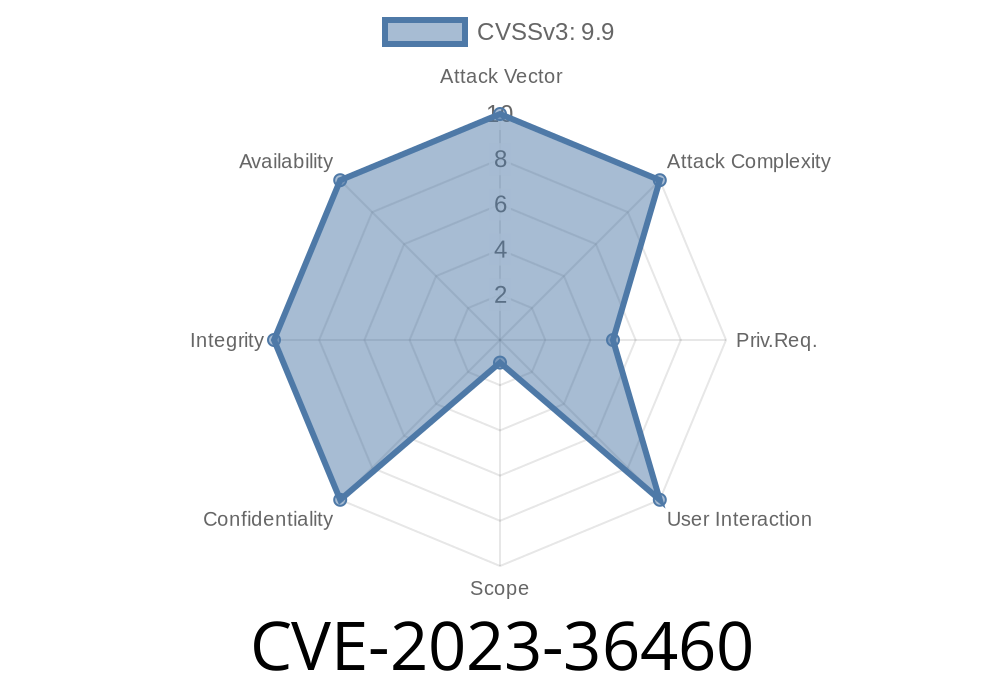
CVE-2023-36460 is a critical security flaw that affected Mastodon, one of the most popular free and open-source social network platforms, from version 3.5. up to but not including patched versions 3.5.9, 4..5, and 4.1.3. This long-form post explains what this vulnerability is, why it’s dangerous, how attackers could exploit it, and what you can do to make sure your Mastodon instance is safe.
What is Mastodon?
Mastodon is a decentralized social network platform—often described as an alternative to Twitter. Mastodon servers (called “instances”) are self-hosted and talk to each other using a modern protocol called ActivityPub. Mastodon is built to help anyone run their own social network, but just like any web application, it must be constantly patched to fix security issues.
What is CVE-2023-36460?
In simple terms: attackers could use special media files to make Mastodon’s backend write or overwrite any file it had access to. This includes configuration files, scripts, or other sensitive data on the server.
Execute arbitrary code remotely (Remote Code Execution, or RCE)
Let’s break down how it happened and what it looks like in code.
The Problem
Mastodon, like most social networks, lets users upload images, video, and audio files. After uploading, Mastodon processes these files: resizing images, generating previews, or transcoding video.
However, starting with version 3.5., Mastodon’s backend didn’t properly sanitize the paths given to these media files. An attacker could craft a media file that, when processed, would cause Mastodon to write new files to arbitrary locations on the server’s filesystem.
Example Exploit
Imagine an attacker uploads a special image file named ../../../../tmp/malicious.rb. If Mastodon didn’t check the filename, it could end up writing or overwriting the file /tmp/malicious.rb on the server.
Example Exploit Scenario
1. Attacker uploads a malicious image – the file is renamed or crafted to have a path like ../../../../var/www/mastodon/live/public/uploads/backdoor.php.
Mastodon processes the image – due to missing checks, Mastodon writes to this path.
3. Attacker accesses or executes the file – if Mastodon serves static files, or if the file is a script that gets executed as part of Mastodon, the attacker gains access, disrupts service, or runs malicious code.
Here’s a dramatically simplified Ruby code snippet to show what went wrong
# Pseudocode to illustrate the vulnerability
user_supplied_filename = params[:file].original_filename # e.g., "../../../../etc/passwd"
save_path = File.join("/var/www/mastodon/public/uploads", user_supplied_filename)
File.open(save_path, 'wb') do |f|
f.write(params[:file].read)
end
If original_filename is not sanitized, a file could be written *anywhere*.
Actual Patch
The Mastodon team patched the vulnerability by making sure that filenames can’t be used to “escape” the intended uploads directory. Meaning: if the upload filename tries to go outside /public/uploads, it gets rejected.
Relevant patch code:
# Now the code resolves the path and checks for escapes
require 'pathname'
uploads_dir = Pathname.new("/var/www/mastodon/public/uploads")
final_path = uploads_dir.join(Pathname.new(user_supplied_filename)).realpath
if !final_path.to_s.start_with?(uploads_dir.to_s)
raise "Attempted directory escape!"
end
Why Is This Dangerous?
- Any File – Logging, scripts, configuration, even system files (if running as root, which is unsafe).
- RCE Possibility – If you overwrite a script or drop a web shell (backdoor.php), and the server executes it, you own the server.
Who Was Affected?
- All Mastodon instances running 3.5. up to 3.5.9 (if not patched), 4.. up to 4..5, and 4.1. up to 4.1.3.
If you run a Mastodon server
1. Upgrade immediately to 3.5.9, 4..5, or 4.1.3 or newer. (Upgrade guide)
2. Consider manually checking for suspicious or unexpected files in your uploads and public directories.
Technical References & Further Reading
- Mastodon Advisory for CVE-2023-36460 on GitHub
- Mastodon Release notes
- CVE-2023-36460 at NIST
- Understanding Path Traversal
Conclusion
CVE-2023-36460 shows how a small oversight in file handling can have a huge impact. Mastodon is a great project, but this bug gave attackers the keys to the kingdom. If you run a Mastodon instance, update now. If you want to know more about open-source security, keep watching for advisories like these—patching just might save your server.
Timeline
Published on: 07/06/2023 19:15:00 UTC
Last modified on: 07/14/2023 19:31:00 UTC