---
Introduction
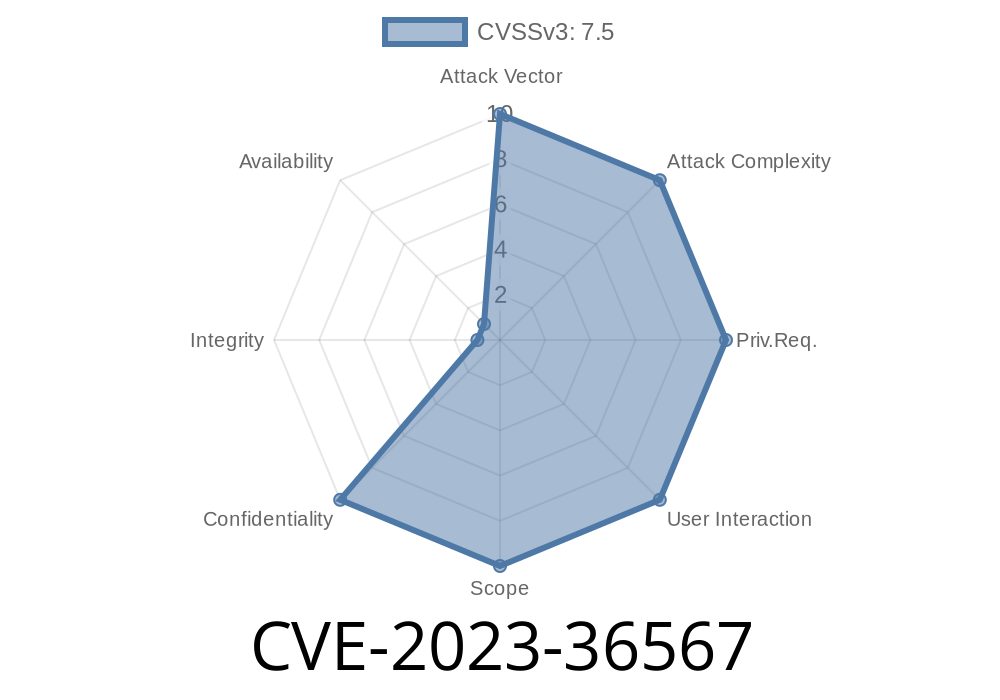
In November 2023, Microsoft patched a vulnerability in Windows Deployment Services (WDS) tracked as CVE-2023-36567. This flaw put sensitive deployment secrets at risk, exposing system credentials and configuration information. If you’re using WDS for imaging or mass deployments, this is something you really need to know about!
This post breaks down how the vulnerability works, what the risks are, and how attackers might exploit it—with simple code snippets and original references.
What is Windows Deployment Services (WDS)?
WDS is a Microsoft server role that lets you deploy Windows images to computers over the network. This is common in enterprise environments for quick provisioning. WDS helps deploy new systems efficiently—but if not secured, it can be a backdoor into your infrastructure.
What is CVE-2023-36567?
CVE-2023-36567 is an Information Disclosure Vulnerability in WDS. An unauthenticated attacker on the same network could exploit it to read potentially sensitive data that wasn’t meant to be public.
Why is this dangerous?
Information disclosure can give attackers the clues they need to carry out bigger and badder attacks—think privileged account credentials, network layout details, or even domain secrets.
Severity: According to Microsoft, this is rated as Important.
How Does the Exploit Work?
When a client connects to WDS to get a boot image (PXE process), certain request parameters are not properly validated. This means an attacker can “trick” the service into serving up files or details outside of what’s safe.
Exploit Mechanism
1. Network Access: You need to be on the same network as the WDS server. Often this is possible in corporate environments, guest Wi-Fi, or during a penetration test.
2. Send Malicious Request: Using a modified network request or tool, the attacker asks the WDS server for a resource it shouldn’t serve.
3. Server Responds: Due to insufficient checks, WDS sends back data like configuration files (unattend.xml, credentials, deployment keys, etc.).
4. Harvest Sensitive Data: If secrets are baked into the deployment setup, the attacker gains them with ease.
Sample Python Snippet (Requesting a File from WDS)
Attackers can use basic scripts or tools like tftp or even custom Python code. Here’s a sample snippet using Python’s socket library that requests a file via TFTP (based on the deployment setup):
import socket
SERVER_IP = '192.168.1.10' # Change to the WDS IP on your network
PORT = 69 # Default TFTP port
FILENAME = 'unattend.xml'
sock = socket.socket(socket.AF_INET, socket.SOCK_DGRAM)
tftp_request = b'\x00\x01' + FILENAME.encode() + b'\x00octet\x00'
sock.sendto(tftp_request, (SERVER_IP, PORT))
while True:
data, addr = sock.recvfrom(4096)
if not data:
break
print(data.decode(errors='ignore')) # Show the data
sock.close()
This script is overly simple, but illustrates how easy it is to probe for files.
Scripts for post-deployment
If an attacker gets this, next steps could be lateral movement, privilege escalation, or launching more targeted attacks.
Microsoft Security Advisory:
CVE-2023-36567 - Microsoft Security Update Guide
Patch Details:
November 2023 Security Updates
Background Reading:
Penetration Testing WDS - harmjy.net
Apply the latest Windows updates that patch this CVE.
- Audit and clean up unattend.xml and other deployment configuration files—avoid leaving passwords or secrets in plain text!
Closing Thoughts
CVE-2023-36567 is a classic example of how deploying systems for ease-of-use can sometimes backfire if you don’t lock down the defaults. If you run WDS, take action today! Patch, review, and monitor.
Remember: in a networked world, the wrong disclosure is all it takes to turn a trickle into a flood.
Timeline
Published on: 10/10/2023 18:15:13 UTC
Last modified on: 10/13/2023 15:15:32 UTC