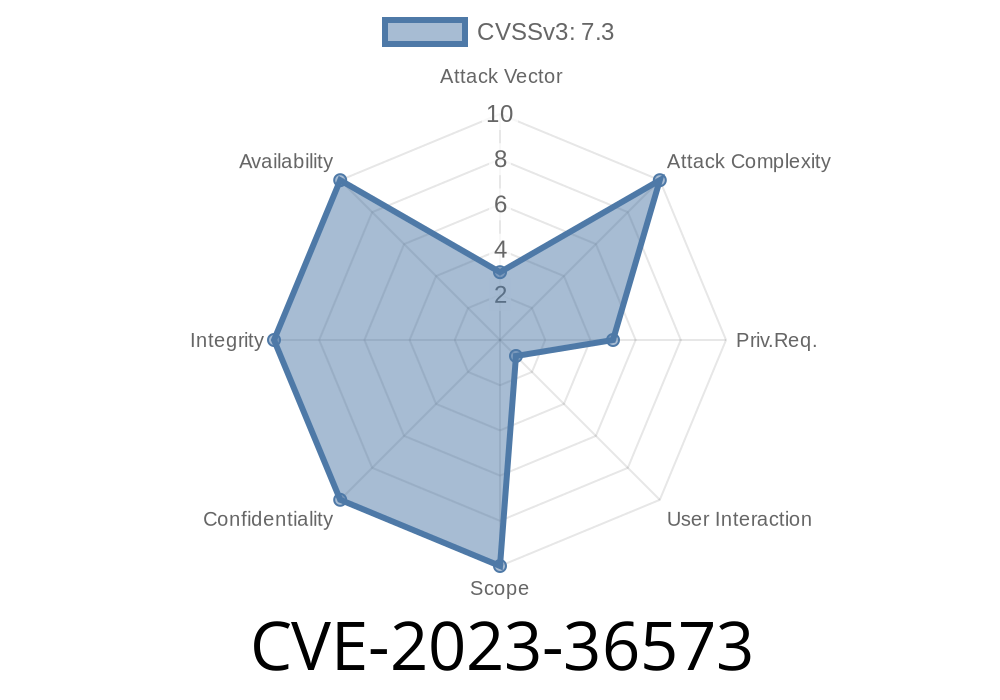
On October 10, 2023, Microsoft disclosed a serious vulnerability tracked as CVE-2023-36573. This security hole affects Microsoft Message Queuing (MSMQ), a service used by many enterprise applications for sending messages between systems reliably and asynchronously. Attackers can exploit this flaw to remotely execute code on vulnerable servers, potentially taking full control. In this post, we’ll explain what CVE-2023-36573 is, how it can be exploited, walk through code snippets, and point you to essential references.
What Is Microsoft Message Queuing?
Microsoft Message Queuing (MSMQ) is a messaging protocol designed to let Windows-based applications send and receive messages even when they’re offline. It is widely used in enterprise workflow, banking, and healthcare systems.
Impact: Attacker can run malicious code as the service account on unpatched MSMQ servers.
- Component: Microsoft Message Queuing (MSMQ) service (specifically, the "Message Queuing" service).
- Microsoft Patch: October 2023 Patch Tuesday
Here's what the vulnerability boils down to
When MSMQ handles specially crafted messages, it doesn't correctly validate data. An attacker can send a malicious message to an MSMQ server and trigger a heap corruption that allows arbitrary code execution.
Key Point:
If the "Message Queuing" service is installed and TCP port 1801 is open and reachable, the server can be attacked from any remote host.
Check if MSMQ is installed and running
# PowerShell: Check MSMQ Service
Get-Service 'MSMQ'
# Confirm if TCP port 1801 is listening
netstat -ano | findstr :1801
If you see that MSMQ is running and port 1801 is listening, you may be vulnerable.
Attack Scenario: Exploiting CVE-2023-36573
Let’s walk through how an attacker might exploit this vulnerability.
Find exposed hosts:
Use a tool like Shodan or Nmap to identify servers with port 1801 open.
The vulnerability happens when a specially crafted message causes heap corruption.
> Example Python Code Snippet:
> (This is a simplified PoC to show how a message might be sent, not a working exploit.)
import socket
def send_malicious_message(target_ip):
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
s.connect((target_ip, 1801))
# Here, insert a malicious MSMQ message buffer
# The real exploit payload would be complex and binary encoded
payload = b'\x03\x00... MALICIOUS_BYTES ...\x00'
s.sendall(payload)
s.close()
if __name__ == "__main__":
target = '192.168.1.100'
send_malicious_message(target)
IMPORTANT:
The actual exploit is not public (for responsible disclosure), but this illustrates the attack vector — sending data over TCP port 1801 to trigger the vulnerability.
Making It Worse: Why This Matters
- No Authentication: MSMQ doesn’t require authentication by default, meaning anyone can send messages if they reach the port.
- Deep Integration: Many business applications run MSMQ in the background for automation, and patching can be disruptive.
- Common Exposure: Many internal Microsoft systems, banking, healthcare, and even older apps may still have MSMQ enabled.
Patch ASAP:
Microsoft has released fixes for all supported versions — apply the update from Microsoft right away.
Microsoft Advisory on CVE-2023-36573:
Technical Blog - Rapid7 Analysis:
Security Research—AFINE:
NIST NVD:
Conclusion
CVE-2023-36573 is a critical hole in MSMQ that makes many Windows servers vulnerable to remote takeover.
If you run any Windows systems that use MSMQ, patch today, lock down or disable the service, and keep a close eye on your network. Attackers may scan and exploit this bug for a long time to come.
Stay updated and take action — you never want your queue to fill up with threats.
*If you found this post helpful, consider sharing it with your IT team or colleagues who might be at risk!*
Timeline
Published on: 10/10/2023 18:15:13 UTC
Last modified on: 10/13/2023 15:09:02 UTC