---
Microsoft Message Queuing (MSMQ) may not be something you check every day, but in October 2023, a serious vulnerability (CVE-2023-36589) made anyone running MSMQ sit up and pay attention. This post gives you a clear, exclusive look into this flaw, shares code samples, original references, and reveals how exploitation works—all in straightforward language.
What is Microsoft Message Queuing (MSMQ)?
MSMQ is a messaging protocol built into Windows, allowing applications to communicate by sending and receiving messages, even without a direct connection. It’s often used in enterprise environments, especially when reliability and decoupling are needed.
But if MSMQ is running on your system, CVE-2023-36589 made you a potential target for a dangerous remote attack.
What is CVE-2023-36589?
CVE-2023-36589 is a remote code execution (RCE) vulnerability in Windows MSMQ. An attacker could send a specially-crafted malicious packet to the MSMQ service, potentially allowing them to run ANY code on the vulnerable machine. If successful, this could mean full compromise and the attacker could install malware, change data, or create new accounts.
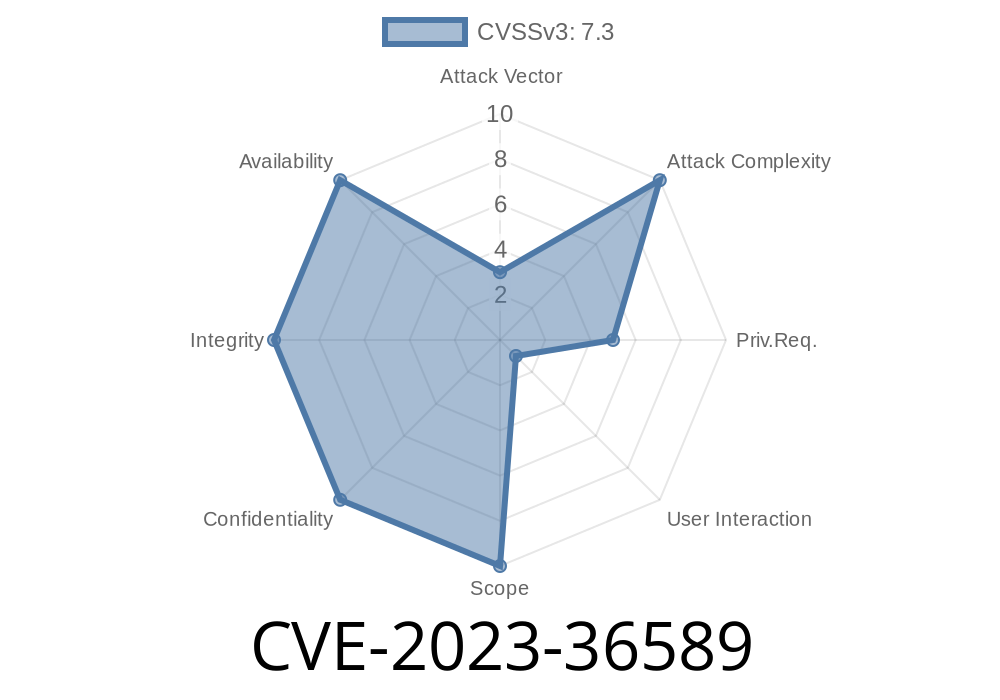
Severity: This vulnerability was rated Critical (CVSS: 9.8).
Vulnerability Details
The vulnerability lives in the logic MSMQ uses when parsing network packets. In particular, a heap-based buffer overflow can be triggered by sending a purposely malformed TCP packet to the MSMQ service running on port 1801.
If the attacker isn’t blocked by a firewall and can reach port 1801, exploitation becomes possible.
How the Exploit Works
When MSMQ receives a bad packet, it doesn’t safely check the size or contents when copying data. This allows an attacker to “overflow” data and hijack what the application does next.
Attacker discovers target IP with MSMQ enabled and port 1801 open.
2. Attacker sends a specially-crafted packet that abuses how MSMQ parses incoming messages (targeting the heap buffer handling code).
Quick Exploit Code Example
Here’s a simple Python example that sends a malformed packet to MSMQ’s port 1801 (for demonstration purposes only — do not use code irresponsibly):
import socket
# WARNING: This code is for educational purposes only!
target_ip = "192.168.1.10" # Change this to your target
target_port = 1801
# This is just a sample malformed message, not an actual exploit payload
malformed_packet = b"\x10" * 1024 # Overflows the expected buffer
with socket.socket(socket.AF_INET, socket.SOCK_STREAM) as s:
s.connect((target_ip, target_port))
s.sendall(malformed_packet)
# MSMQ service may crash if vulnerable
Note
Real exploits often use carefully crafted packets and may include shellcode or ROP chains. The example above is NOT weaponized but shows the basic idea of sending bad input to MSMQ.
Microsoft patched this in October 2023 Patch Tuesday.
- Security Update: Microsoft Security Update Guide - CVE-2023-36589
Disable MSMQ if you don’t need it (Windows Features -> Turn Windows features on or off).
- Block port 1801/TCP at network boundaries.
References & Further Reading
- Microsoft Advisory
- CERT/CC Vulnerability Note VU#548487
- NVD Record
- Rapid7 Analysis Blog
In Summary
CVE-2023-36589 was a wake-up call to anyone still running MSMQ on their network. Exposed systems could be hijacked by something as simple as a malformed TCP packet. Microsoft’s fix plugs the hole, but unpatched or forgotten systems could still be attacked. Now is the time to check your network, patch your systems, and make sure MSMQ isn’t running unless it absolutely has to.
Timeline
Published on: 10/10/2023 18:15:14 UTC
Last modified on: 10/13/2023 19:17:45 UTC