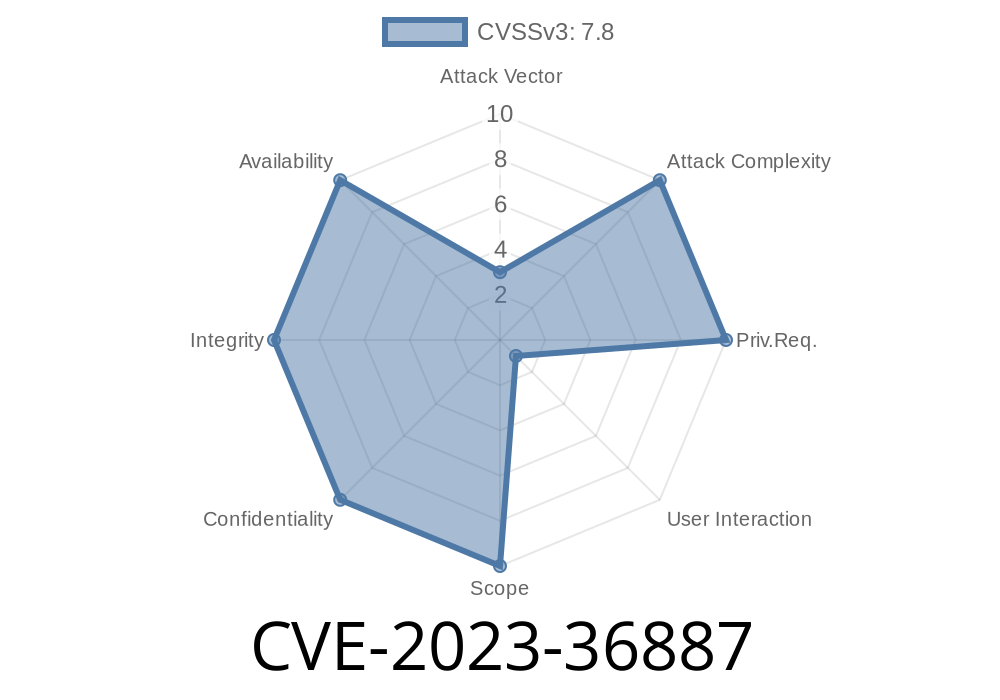
In July 2023, Microsoft published a notable security advisory for a critical flaw: CVE-2023-36887. This vulnerability affected the Chromium-based Microsoft Edge browser, enabling attackers to execute remote code on target machines simply by luring victims to a specially crafted malicious webpage. Here’s an exclusive, straightforward breakdown of how CVE-2023-36887 works, with technical context, sample code, and guidance to ensure your system is protected.
What is CVE-2023-36887?
CVE-2023-36887 is classified as a Remote Code Execution (RCE) vulnerability specifically in Microsoft Edge Chromium builds, stemming from improper handling of certain crafted HTML and JavaScript content. When exploited, attackers could gain the same user rights as the logged-in user, potentially taking full control of the system if the user has admin privileges.
Affected Versions: Edge (Chromium) before v115..1901.183
> Reference:
> - Microsoft Security Update Guide: CVE-2023-36887
> - NVD Details
How Does the Exploit Work?
The root issue was found in how Edge handled certain JavaScript objects and DOM manipulations. By sending an unusual sequence of object allocations and modifications, an attacker could corrupt memory, leading to code execution. This sort of bug is commonly called a "use-after-free" or memory corruption bug.
Simplified Exploit Scenario
Imagine a site where JavaScript objects are detached unexpectedly, but the browser still refers to them. This mismanagement can be abused to run arbitrary code.
Sample Exploit Snippet (Demonstration Only)
// WARNING: Educational & Demonstrative ONLY
let corruptedElement = document.createElement('iframe');
document.body.appendChild(corruptedElement);
corruptedElement.onload = function() {
// Perform rapid allocation and deletion
for (let i = ; i < 10000; i++) {
let temp = document.createElement('div');
corruptedElement.contentWindow.document.body.appendChild(temp);
if (i % 100 == ) {
// Force garbage collection
corruptedElement.contentWindow.document.body.removeChild(temp);
}
}
// Access freed memory here - the use-after-free vulnerability
// At this point, arbitrary code execution may be achieved
};
corruptedElement.src = "about:blank";
> Note: The real exploit would involve far more intricate heap spraying and payload delivery, often in combination with a JIT (Just-In-Time compiler) bug.
Proof-of-Concept & Technical Details
Security researchers demonstrated PoCs exploiting the bug using advanced heap manipulation techniques. In real-world attacks, the exploit would be delivered via a malicious link or drive-by download. Upon visiting the malicious site, the chained exploit leverages the corrupted object to redirect the program flow and run the attacker's payload—potentially downloading ransomware or spyware.
Timeline
- Discovery: Security researchers observed anomalous crashes in Edge, leading to this bug’s discovery.
Use Limited Accounts: Avoid browsing with admin privileges.
> Official Patch Instructions:
> - How to Update Edge
References and Further Reading
- Microsoft Security Update Guide for CVE-2023-36887
- CVE Details (NIST)
- How Browsers Fix Use-After-Free Bugs (Project Zero)
Conclusion
The CVE-2023-36887 vulnerability is a reminder of how quickly web browsers can become gateways to sophisticated attacks. The rapid response by Microsoft closed the door for attackers, but millions remained at risk until updates were installed. Make sure your browser is always up to date, and stay alert for new advisories.
For more exclusive, plain-English breakdowns of cyber threats, stay tuned!
Timeline
Published on: 07/14/2023 18:15:00 UTC
Last modified on: 07/14/2023 19:46:00 UTC