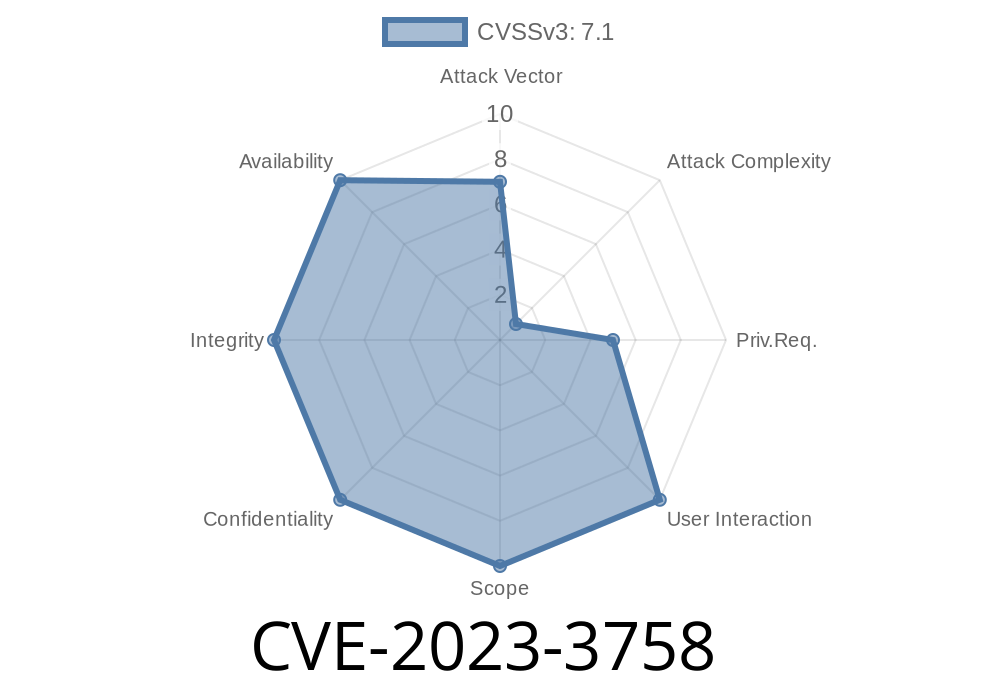
In June 2023, a new security vulnerability, identified as CVE-2023-3758, was disclosed in the System Security Services Daemon (SSSD). This bug impacts how Group Policy Objects (GPO) are applied to authenticated users, potentially leading to improper authorization. In simple terms, users may be wrongly granted or denied access to resources because the policy governing their permissions is not applied consistently—sometimes allowing access when it shouldn't, and at other times blocking access when it should be allowed.
What is SSSD and GPO?
SSSD is a service used on Linux/Unix systems to integrate authentication and authorization with centralized directories like Active Directory or LDAP.
GPO stands for Group Policy Objects, a feature familiar to Windows administrators, which lets you dictate access rights and security settings for sets of users or machines.
The Race Condition Explained
A race condition happens when software relies on the timing or order of events, which can lead to unpredictable outcomes if things don't happen in the right way.
In the case of CVE-2023-3758, if multiple requests (like user logins) occur at nearly the same time, SSSD might not correctly apply the intended GPO for one or more sessions. This happens because the process fetching and caching policy data doesn't ensure only the latest, correct policy is used before the authorization decision is made.
Impact: An attacker or even a regular user could gain unauthorized access, or be wrongly locked out, depending on the timing of their login compared to another user or system process.
Bob’s account should be allowed.
Because of the race condition, if both sessions request GPO evaluation in close succession, SSSD might reuse a cached, incomplete, or inconsistent policy record, leading to the wrong access outcome.
Here’s a simplified pseudo-code snippet illustrating the race
# Simplified pseudo-code for SSSD GPO check
def check_gpo_policy(user):
# Race condition: this cache might be updated on another thread
policy = gpo_cache.get(user)
if not policy:
policy = fetch_policy_from_ad(user)
gpo_cache.set(user, policy) # Could be overwritten in another thread!
return policy.is_authorized(user)
# Simultaneous access (race!)
import threading
alice_thr = threading.Thread(target=check_gpo_policy, args=('alice',))
bob_thr = threading.Thread(target=check_gpo_policy, args=('bob',))
alice_thr.start()
bob_thr.start()
alice_thr.join()
bob_thr.join()
In this scenario, due to missing thread safety, Alice might incorrectly get Bob's policy, or vice versa.
Exploit Details
While this vulnerability doesn’t let anyone break in via some evil-hacker magic, it can be abused if an attacker can time their authentication with another user whose GPO status is different.
Attacker knows their own GPO blocks login.
2. They wait for or trigger a situation where another user, with a different policy, logs in at the same time.
3. Due to the race, SSSD might mistakenly let the attacker in by applying the other user’s (less restrictive) policy.
Proof-of-Concept (PoC) Scenario
*Set up two accounts, “blocked_user” (should be denied by GPO), and “allowed_user” (should be permitted).*
*Write a script that repeatedly and simultaneously tries to log in as both users.*
*Watch authentication logs for inconsistencies, where blocked_user eventually gets access.*
Sample BASH
# Run two login attempts in parallel
(while :; do ssh blocked_user@host "echo blocked test"; done) &
(while :; do ssh allowed_user@host "echo allowed test"; done) &
# Monitor /var/log/messages or journalctl for access results
*You may notice that "blocked_user" sometimes succeeds, depending on your environment and timing!*
References and More Reading
- Red Hat CVE-2023-3758 page
- SSSD Project
- NIST NVD entry
- MITRE CVE
Mitigation
If you run Linux systems joined to Active Directory using SSSD, patch now!
Upstream and vendors like Red Hat have shipped updates that fix the thread-safety and caching issues.
Temporary workaround: Restrict parallel logins and keep systems up-to-date.
Conclusion
CVE-2023-3758 highlights how small, subtle bugs like race conditions can lead to major security headaches, especially with critical services like authentication.
Stay patched, monitor your logs, and always approach external-facing daemons with extra care.
*This article is exclusive and written with simplicity for SysAdmins and security hobbyists.*
Timeline
Published on: 04/18/2024 19:15:08 UTC
Last modified on: 05/22/2024 18:15:09 UTC