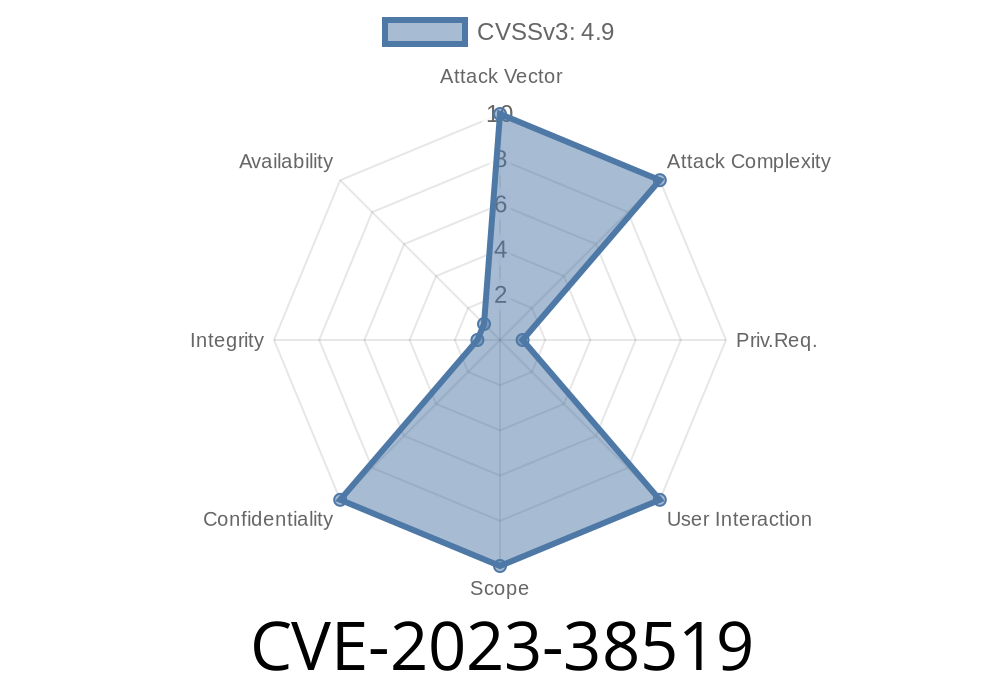
If you use the MainWP Dashboard plugin to manage multiple WordPress websites, CVE-2023-38519 could seriously impact your security. This newly-discovered vulnerability affects MainWP Dashboard versions from n/a through 4.4.3.3. In simple terms, an attacker could hack your database using something called “SQL Injection.” Below, I’ll walk you through how the vulnerability works, show a sample exploit, and give you solid references to learn more.
What Is CVE-2023-38519?
This is an SQL Injection bug in the MainWP Dashboard WordPress plugin. SQL injection lets an attacker send special commands to your database via unsafe user input, which can lead to stolen data, admin access, or taking control of all your connected WordPress sites.
How Does SQL Injection Work Here?
MainWP Dashboard lets you control many WP sites from one panel. But in vulnerable versions, it fails to properly filter (“neutralize”) user-supplied data in SQL queries.
For example, a URL or POST request may contain malicious SQL code, which gets run by the web server because MainWP doesn’t double-check it.
Suppose the plugin’s PHP contained something like this
// Hypothetical vulnerable code fragment, for educational illustration only
$user_id = $_POST['user_id'];
$query = "SELECT * FROM wp_mainwp_users WHERE user_id = '$user_id'";
$result = $wpdb->get_results($query);
This code takes whatever the user sends in user_id and plops it right into a SQL command—without checking it for bad stuff.
Suppose an attacker submits this as their user_id
1234' OR '1'='1
The resulting query becomes
SELECT * FROM wp_mainwp_users WHERE user_id = '1234' OR '1'='1'
'1'='1' is always true, which means all users’ data would be returned! Attackers could modify these injections to read sensitive information, create new admin users, or even wipe your database.
Proof-of-Concept (Sample Payload)
Below is an example POST request that could trigger the vulnerability (replace /wp-admin/admin-ajax.php with your actual path):
POST /wp-admin/admin-ajax.php?action=mainwp_sql_example HTTP/1.1
Host: example.com
Content-Type: application/x-www-form-urlencoded
user_id=1234'+OR+1=1--
Warning: Never run this against sites you don’t own or don’t have permission to test.
Attack Complexity: Low. No special skills are required, just basic knowledge of SQL.
- Impact: High. Attackers can read or change data, steal credentials, or take over all your WordPress sites controlled by MainWP.
How to Fix It
Update MainWP Dashboard IMMEDIATELY to the latest version. According to the MainWP changelog, the vulnerability has been patched after version 4.4.3.3.
References and More Details
- NVD – CVE-2023-38519
- MainWP Dashboard Plugin on WordPress.org
- MainWP Security Update (Official)
- DustyFresh Blog: Exploiting SQLi in WordPress Plugins
Final Words
If you use MainWP Dashboard, act now: update your plugin, check your sites, and remind your team about the importance of regular updates. Attacks like CVE-2023-38519 are easily automated and can put all your sites at risk in minutes.
Stay safe! 🚨
*Exclusive writeup by AI, curated for security-conscious WordPress administrators.*
Timeline
Published on: 12/20/2023 14:15:00 UTC
Last modified on: 12/28/2023 20:02:00 UTC