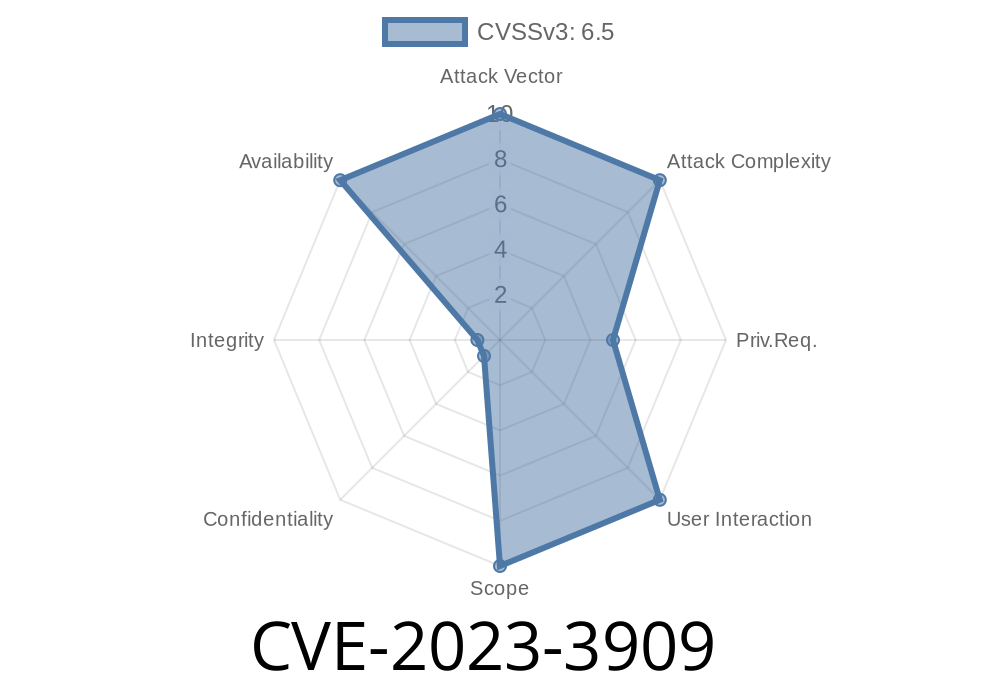
In September 2023, security researchers uncovered a critical vulnerability in GitLab Community Edition (CE) and Enterprise Edition (EE): CVE-2023-3909. This vulnerability—affecting versions from 12.3 up to (but not including) 16.3.6, as well as some 16.4 and 16.5 releases—allowed attackers to orchestrate a Regular Expression Denial of Service (ReDoS) attack by simply adding a massive string in the timeout field of the .gitlab-ci.yml configuration. Such a flaw could halt or slow GitLab services, impacting development teams’ productivity and cloud resources.
What’s the Root Cause?
GitLab supports CI/CD pipelines managed by .gitlab-ci.yml. You can set the timeout for jobs like this:
job1:
script: echo "Hello, world!"
timeout: '10 minutes'
Under the hood, GitLab tries to validate and parse the timeout value—usually using a regular expression (regex). The problem? GitLab’s parser tried to match the timeout string using a regex pattern that was *vulnerable* to catastrophic backtracking, an issue that can freeze the server if someone submits a weirdly long or malformed string.
16.5 ≤ version < 16.5.1
Official advisory:
https://gitlab.com/gitlab-org/cves/-/blob/master/2023/CVE-2023-3909.json
GitLab release notes:
https://about.gitlab.com/releases/2023/10/05/security-release-gitlab-16-5-1-released/
How the Exploit Works
If you maintain a GitLab instance (or have rights to edit pipeline configs in a project), the attack is simple:
Edit .gitlab-ci.yml.
2. In a job’s timeout, supply an *enormous* and *malicious* string that triggers worst-case regex matching.
Here’s a sample payload
exploit-job:
script:
- echo "Attempting ReDoS"
timeout: >
1h1m1saaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaa
The real attack works best by crafting the input so the regex engine spends time trying to match many possibilities. Attackers often use nested, repeating patterns that regex engines struggle with—supplying *many thousands or millions of ‘a’* or creating more complex, evil patterns.
When GitLab processes this, the backend validation step evaluating the timeout hits a regex loop and stalls, eating CPU and memory.
GitLab’s code (in older versions) included code segments like
# In Ruby, as used in GitLab
# Validate the timeout value from .gitlab-ci.yml (simplified example)
def valid_timeout?(timeout_str)
# Example regex pattern (simplified for clarity)
!!timeout_str.match(/^(\d+h)?(\d+m)?(\d+s)?$/)
end
While this regex works fine for normal inputs, with sufficiently large malformed strings, the regex matcher can end up spending *minutes or hours* just checking if the input fits, tying up application resources.
echo "Testing ReDoS vulnerability"
timeout: "1s"aaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaa
Remote Exploitation
- No need for direct server access—Anyone with permission to submit a merge request, push branches, or create CI/CD pipelines can trigger this.
- If your instance is on a public server, attackers could lock up your CI/CD pipeline processing, affecting all users.
Impact
- Denial of Service (DoS): A locked pipeline job can cause system slowdowns, high CPU/memory load, and prevent new jobs from running.
Resource Drain: Servers may need to be restarted or containers rebuilt, disrupting service.
- Potential Chaining: Combined with other flaws, might enable deeper or broader attacks (not yet observed).
Fixes & Workarounds
Upgrading is critical!
Monitor server resource usage for unexplained spikes.
Official patch (for self-hosters):
https://about.gitlab.com/releases/2023/10/05/security-release-gitlab-16-5-1-released/
Conclusion
CVE-2023-3909 demonstrates how a simple bad regex can topple even sophisticated systems. Regular expression denial of service is a real threat—especially when user-supplied input is unchecked. Anyone running a GitLab server must patch to a secure version and audit their instance for any suspicious pipeline timeouts.
References
- Official CVE entry
- GitLab Security Release - 16.5.1
- OWASP: Regular Expression Denial of Service (ReDoS)
Stay safe, keep your dependencies up-to-date, and never underestimate the power of regexes in the wrong place!
Timeline
Published on: 11/06/2023 13:15:09 UTC
Last modified on: 11/14/2023 18:01:26 UTC