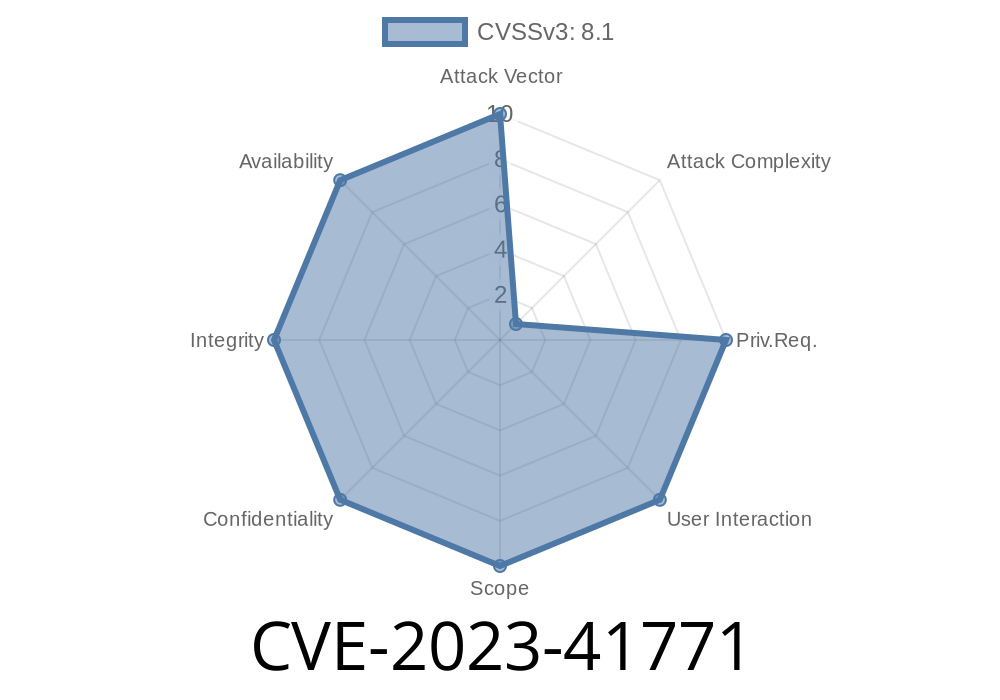
In late 2023, the cybersecurity community was rocked by CVE-2023-41771, a critical remote code execution (RCE) vulnerability in the Layer 2 Tunneling Protocol (L2TP) found in several Windows systems. Let’s break down how this bug works, why it matters, and what you can do to protect yourself.
What Is L2TP, and Why Should You Care?
Layer 2 Tunneling Protocol (L2TP) is a networking protocol used to support VPNs (Virtual Private Networks). Windows systems use L2TP to help users create secure, private connections over the internet. Lots of businesses rely on L2TP for remote work access.
But, just like any software, if there’s a bug in how L2TP handles incoming connections, attackers might exploit it.
What Is CVE-2023-41771?
CVE-2023-41771 is a remote code execution vulnerability. Specifically, a remote, unauthenticated attacker can send specially crafted L2TP packets to a vulnerable Windows server, possibly letting the attacker run code with system privileges. That means, if exploited, a hacker could potentially take over the affected device.
This bug was fixed in the November 2023 Patch Tuesday update. Without the patch, your system could still be at risk.
Technical Details
Microsoft’s advisory (MSRC CVE-2023-41771) explains that the vulnerability is due to improper input validation in the Windows L2TP service. Crafted packets can cause buffer overflows, allowing an attacker to place malicious code in memory that gets executed by the system.
Proof-of-Concept Code (Simplified Example)
This is theoretical and does not contain any live exploits, but it shows how an attacker might send a raw L2TP packet.
import socket
# L2TP usually runs over UDP port 1701
target = "victim.server.ip"
port = 1701
# This is a bogus/crafted L2TP packet (not a real exploit)
malicious_packet = b'\x00\x00\x00\x00' + b'\x90' * 100 # Example: Overflow with x90 NOPs
s = socket.socket(socket.AF_INET, socket.SOCK_DGRAM)
s.sendto(malicious_packet, (target, port))
print("Malicious L2TP packet sent!")
s.close()
*Note: Sending random packets will NOT exploit the bug—it takes deep protocol knowledge and specific byte values based on the vulnerability details.*
Real-World Impact
Because this attack is unauthenticated and remotely exploitable, it’s especially dangerous. You don’t need a valid login or user account. If your server exposes L2TP on the open internet and is unpatched, you’re at risk.
Security researchers started seeing mass Internet scans for open L2TP ports soon after the bug was announced.
How To Protect Yourself
1. Patch Now: Update all Windows devices—especially servers running VPN services—using Windows Update or download the patch from Microsoft.
Restrict Access: Block UDP port 1701 at your firewall unless absolutely needed.
3. Monitor: Look for strange traffic on port 1701. Unexpected connections could mean someone is poking at your VPN for weaknesses.
Official References
- Microsoft CVE-2023-41771 Advisory
- National Vulnerability Database (NVD) Entry
- SecurityWeek coverage
- Rapid7 Analysis
Final Thoughts
CVE-2023-41771 is a big deal, especially if you run VPN services with L2TP. An attacker anywhere in the world could compromise your server just by sending the right packet. Patch your systems now and double-check your firewall rules to keep yourself and your business safe.
If you want more technical detail or need help, check out Microsoft’s resources or consult your IT security team.
Timeline
Published on: 10/10/2023 18:15:18 UTC
Last modified on: 10/12/2023 22:17:19 UTC