Google Chrome is used by millions of people every day for browsing the web. It’s known for its speed and security, but like any big software, sometimes critical bugs slip through. In this post, we break down a high-severity Chrome bug: CVE-2023-4428. We’ll explain what happened, what the risk was, and how hackers could abuse it. Let’s dive in.
What is CVE-2023-4428?
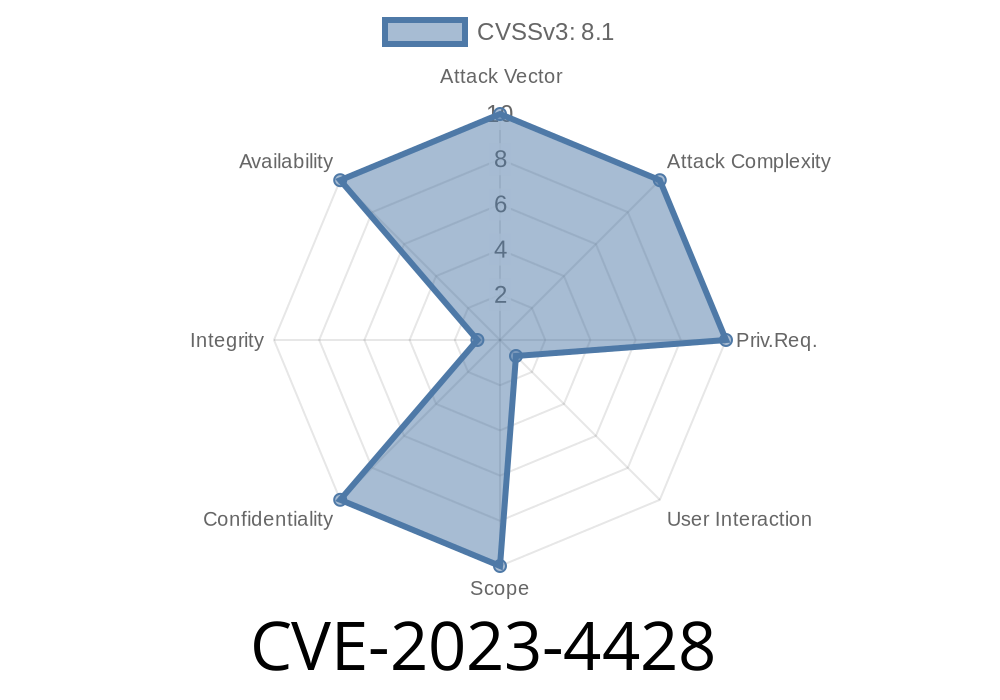
CVE-2023-4428 is a security vulnerability in Google Chrome, present before version 116..5845.110. The problem? Chrome’s CSS engine didn’t handle some memory operations the right way. When a specially crafted HTML page was loaded, this flaw could let an attacker read memory they shouldn’t be able to see.
Patched Version: 116..5845.110
Reference:
- Google Chrome Release Notes
- Chromium Issue Tracker #1464277
What’s Out of Bounds Memory Access?
Out of bounds means reading or writing outside the allocated memory for a program. Imagine you have a row of mailboxes (memory). If someone opens a mailbox that doesn’t belong to them (past the end), they might see sensitive mail (data). In a browser, this can mean attackers see secrets belonging to Chrome or even other web pages.
How Does This Bug Work?
The bug lies in Chrome’s Cascading Style Sheets (CSS) engine. Attackers could create tricky HTML and CSS code that, when loaded by a victim, tricks the browser into reading memory that’s not meant for web content. This can leak private information, crash the tab, or sometimes even help in more complex exploits like sandbox escapes.
User visits the page in an outdated version of Chrome.
3. The browser’s CSS engine mishandles memory, allowing attacker to read memory outside the intended boundaries.
Proof of Concept (PoC) Code
Disclaimer: This code is for educational purposes only. Do not run untrusted code or visit untrusted sites.
Below, you can see a simplified version of a crafted HTML + CSS snippet that could trigger the vulnerability. Due to responsible disclosure, the real bug details are more subtle and complex, but this shows the kind of thing involved.
<!DOCTYPE html>
<html>
<head>
<style>
/* Crafted complex CSS to confuse Chrome's parser */
@supports (not ((color: #fff) or (background: #000))) {
div {
background: repeating-linear-gradient(
45deg,
#f06,
#f06 10px,
#ff 10px,
#ff 20px
),
url('data:image/svg+xml;utf8,<svg xmlns="http://www.w3.org/200/svg"></svg>';);
width: calc(1% * 100000000); /* Overflows CSS parsing logic */
}
}
</style>
</head>
<body>
<div>Exploiting CVE-2023-4428</div>
</body>
</html>
This serves as a template for out-of-bounds-type attacks via CSS. In reality, the bug required very specific manipulation of CSS features like gradients, filters, or even calc() values.
What Could an Attacker Achieve?
- Read information outside the current web page’s allocated memory (like data from other web pages, browser processes, or problems leading to leaking credentials and keys).
How Was It Fixed?
The Chrome team released a patch in version 116..5845.110, tightening up the memory checks in the CSS code. Here’s a simplified version of a typical fix:
// Example C++ fix (not actual Chrome code!)
if (index < data_length) {
return data[index];
} else {
// Prevent out of bounds
return kDefaultValue;
}
This check ensures that any access to memory is within the allowed range.
More References
- CVE-2023-4428 on NVD
- Chrome Security Blog
- Chromium Issue Tracker #1464277 (May need special access for some details)
Summary
CVE-2023-4428 is a critical reminder that even the best browsers occasionally get severe bugs. This flaw in how Chrome handled CSS meant web pages could see memory they shouldn’t, making it a valuable bug for attackers. The best fix? Just keep your browser up to date—Chrome’s patch fixed it, and you’re safe as long as you’re running the latest version.
Timeline
Published on: 08/23/2023 00:15:00 UTC
Last modified on: 08/25/2023 13:18:00 UTC