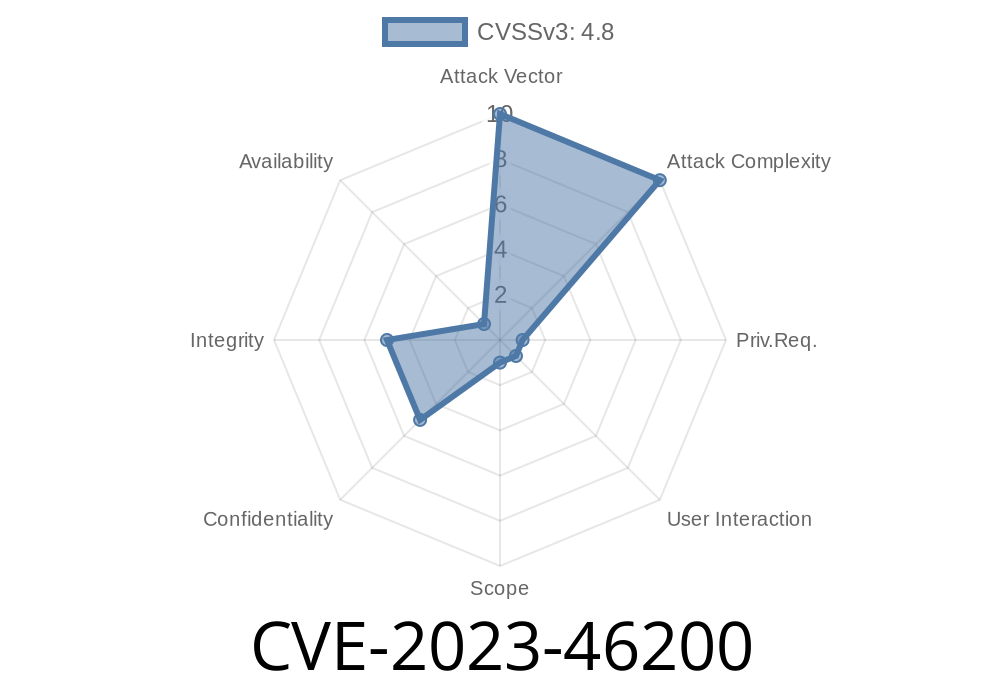
CVE-2023-46200 refers to a serious vulnerability in the WordPress plugin Smart App Banner developed by Stephen Darlington, Wandle Software Limited. The flaw is a Stored Cross-Site Scripting (XSS) vulnerability, found in all plugin versions up to and including 1.1.3. The vulnerability can be exploited by logged-in users with administrative (or higher) privileges.
Let’s break down what this means and why it matters, with easy-to-understand details, code snippets, and direct links to official sources.
What’s Special About Stored XSS?
Stored XSS is serious because the attacker’s malicious code is _saved in the database_ and then shown to any user visiting the affected page or section. Unlike reflected XSS, which requires a user to click a malicious link, stored XSS can affect anyone who loads the poisoned page. In this case, the Smart App Banner plugin is vulnerable to code injection by an authenticated admin+ user.
Because the attack requires admin access, this is not as critical as a bug that can be exploited by anyone — but it can be dangerous in multi-admin environments, or if an account is compromised.
How Does CVE-2023-46200 Work?
The plugin lets admins customize Smart App Banner settings via the WordPress dashboard. However, it fails to properly sanitize or escape certain settings fields before saving them. This oversight allows an attacker to inject malicious JavaScript code into these fields.
Which Plugin Setting Is Vulnerable?
The vulnerable parameter is the ‘App ID’ input field on the plugin’s settings page.
The malicious code is saved in the WordPress database.
3. When any user loads a site page, the plugin’s JavaScript executes the attack code in their browser.
Sample Exploit Code
Suppose you’re an admin (or have hijacked an admin account) and you want to exploit this bug. In the Smart App Banner settings:
- Inject the following payload
"><script>alert('XSS by CVE-2023-46200')</script>
A real attacker wouldn’t just trigger an alert — they might steal cookies, hijack sessions, or perform more damaging actions.
How does it look in the database?
The malicious payload is stored as an option value in the WordPress wp_options table, something like:
INSERT INTO wp_options (option_name, option_value)
VALUES ('smartappbanner_app_id', '"><script>alert(document.cookie)</script>');
Every time a page loads with the plugin’s banner, this code runs.
Upgrade Solution
The vulnerability is patched in version 1.1.4. If you are using version 1.1.3 or below, *update the plugin immediately*.
- Smart App Banner on WordPress.org
- Plugin Changelog
Official References
- CVE Details at National Vulnerability Database
- WPScan Advisory
- Plugin Homepage
Conclusion
CVE-2023-46200 might require admin+ access to exploit, but it’s still a major security concern for websites with multiple trusted administrators, or where attacker privilege escalation is possible. Don’t underestimate XSS bugs just because they require authentication — especially if those accounts are reused or stored weakly.
Patch your plugins. Understand your exposure. And let’s keep the web safer together.
*If you found this useful, consider sharing it with other site admins or plugin developers who need to stay up-to-date on emerging security issues!*
Timeline
Published on: 10/27/2023 21:15:09 UTC
Last modified on: 10/31/2023 15:23:38 UTC