FFmpeg is one of the most widely-used open source multimedia frameworks in the world. It powers media processing in countless applications. But in November 2023, a security bug was reported that could put users at risk: CVE-2023-46407. In this post, we’ll break down the vulnerability, show the original code, walk through a simplified exploit, and offer advice on staying safe.
What Is CVE-2023-46407?
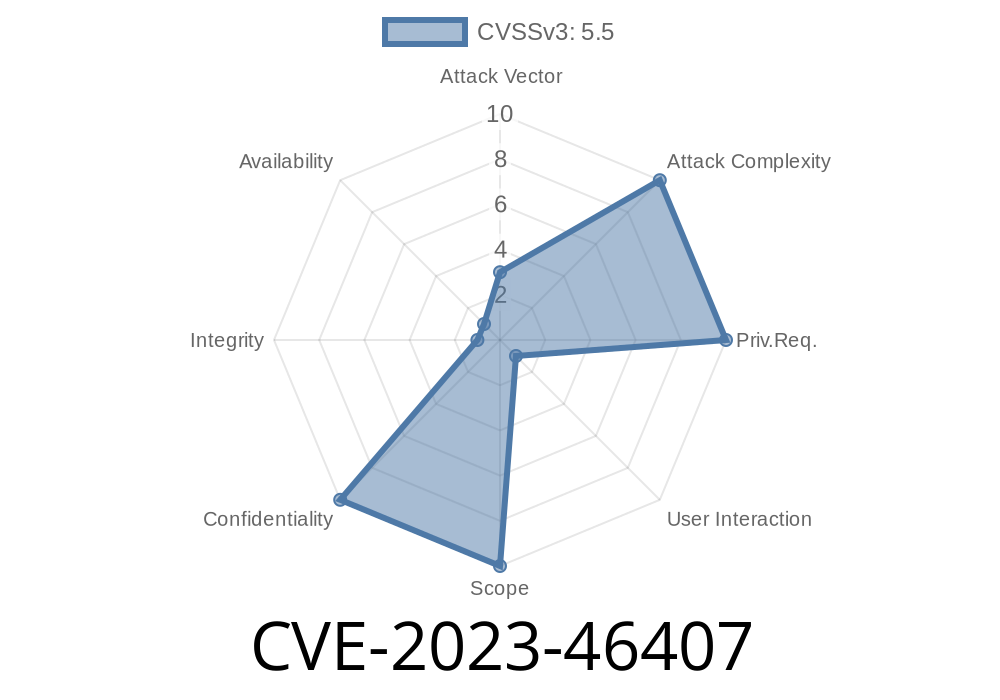
CVE-2023-46407 is an out-of-bounds read in FFmpeg, found before commit bf814, specifically inside the read_vlc_prefix() function. The issue is triggered by the dist->alphabet_size variable, which can be manipulated to make the function read memory it shouldn’t—possibly leaking information or crashing the application.
Discovered? By security researchers on the FFmpeg project, affecting many users before the patch landed.
Where’s the Bug?
You can see the fix in the official FFmpeg Git repository:
FFmpeg Commit bf814 Details
The root problem is here: dist->alphabet_size is used without enough validation. If it’s too large, you get a buffer/read overflow.
Relevant Original Code (before fix)
int read_vlc_prefix(GetBitContext *gb, VLC *vlc, int index) {
int code;
// This should validate dist->alphabet_size, but doesn’t!
if (index < dist->alphabet_size)
code = vlc->table[index];
else
code = -1; // May access memory out of bounds if index is too high!
return code;
}
The Problem:
The alphabet_size is supposed to limit valid indexes, but if it’s wrong (or the input stream lies) it can reference memory outside the intended table, causing an out-of-bounds read.
How Can It Be Exploited?
If an attacker crafts a malicious encoded video or audio file with a *fake* large alphabet_size or corrupts the input so that read_vlc_prefix() receives a big index, FFmpeg could:
Here’s a simplified C snippet demonstrating the risk
#include <stdio.h>
#include <stdlib.h>
#define TABLE_SIZE 4
int read_vlc_prefix(int* table, int index, int alphabet_size) {
// Broken validation: attacker controls alphabet_size and index!
if (index < alphabet_size)
return table[index]; // may read past array!
return -1;
}
int main() {
int table[TABLE_SIZE] = {10, 20, 30, 40};
int mal_index = 10; // way past valid size!
int mal_alphabet_size = 20; // attacker-supplied, highly invalid
// Dangerous out-of-bounds read
printf("Value: %d\n", read_vlc_prefix(table, mal_index, mal_alphabet_size));
return ;
}
Run this program, and it will try to read memory that doesn’t belong to table. A real attack would use a fuzzed audio/video file.
Information leaks (the process may print, log, or otherwise reveal sensitive data from memory!)
For multimedia libraries, where files are regularly decoded from the public internet, this is a serious vector for attacks.
How Is It Fixed?
The official patch validates the index before accessing the table, making sure it never goes outside the allocated memories.
Patch Example
- if (index < dist->alphabet_size)
- code = vlc->table[index];
- else
- code = -1;
+ if (index < dist->alphabet_size && index < VLC_TABLE_SIZE)
+ code = vlc->table[index];
+ else
+ code = -1;
*Now, there’s a proper comparison to the max allowed size!*
Am I Affected? (How to Check)
- If you have FFmpeg built or installed from before commit bf814 (November 2023), you may be vulnerable.
Run ffmpeg -version to see your build date.
Reproducible Test: Try decoding a suspicious, malformed video file. If your FFmpeg instance segfaults, you’re likely vulnerable.
Update FFmpeg!
Get the latest from FFmpeg.org or your package manager.
2. Don’t open suspicious audio/video files with vulnerable versions.
References
- CVE-2023-46407 at NIST
- FFmpeg Commit bf814 Patch
- FFmpeg Security Advisories
Bottom Line
CVE-2023-46407 shows that even “simple” validation mistakes can lead to dangerous software bugs. If you use FFmpeg or ship products based on it, update right away and follow safe coding practices. Even the world’s best open source media tools can have security holes—let’s patch them fast.
Timeline
Published on: 10/27/2023 20:15:09 UTC
Last modified on: 11/07/2023 19:51:29 UTC