Vim is a legendary text editor loved by coders worldwide, but even the strongest software can have cracks. CVE-2023-4733 is one such crack—an exploitable use-after-free (UAF) vulnerability discovered in the vim/vim GitHub repository, affecting versions prior to 9..184. In this post, we'll break down what happened, see proof via a simple code snippet, and explain attack possibilities in plain English.
What is CVE-2023-4733?
CVE-2023-4733 is a use-after-free security flaw in Vim, where memory that’s already freed can be accessed again. This issue occurs under specific operations, allowing an attacker to execute code or cause a crash (DoS) by manipulating Vim in a certain way.
Official Advisory
- NIST NVD: https://nvd.nist.gov/vuln/detail/CVE-2023-4733
- GitHub Security Advisory: vim/vim#13208
> “Use After Free in GitHub repository vim/vim prior to 9..184.”
Where Did It Happen?
This bug was lurking in the way Vim internally handles substitutions and buffer operations. Specifically, freeing a memory object that Vim might try to use again.
A commit that fixes this issue can be seen here:
https://github.com/vim/vim/commit/93c01876adcf8f00c22501c6a77951ec9e9b223
The vulnerability is exploited by tricking Vim into using a freed pointer during certain text manipulation commands.
Understanding Use-After-Free (UAF)
Imagine you have an old address book (pointer), you throw it away (free), but then days later you use that same address (now invalid) to send a letter. You don’t know who might be there now!
Let’s illustrate with simplified pseudocode
char *buf = malloc(100);
free(buf);
// OOPS: accidental use after free
strcpy(buf, "danger!"); // Potentially exploitable
In Vim, this could be triggered with a specially crafted command or file input.
How Attackers Could Use This
A real-world scenario is a *malicious Vim modeline* at the top of a file you open or a plugin that takes advantage of the bug.
This PoC from the security fix points out where the memory is mishandled
- free(foo);
- if (something)
- use(foo); // UAF!
+ if (something)
+ ; // Don't use freed memory!
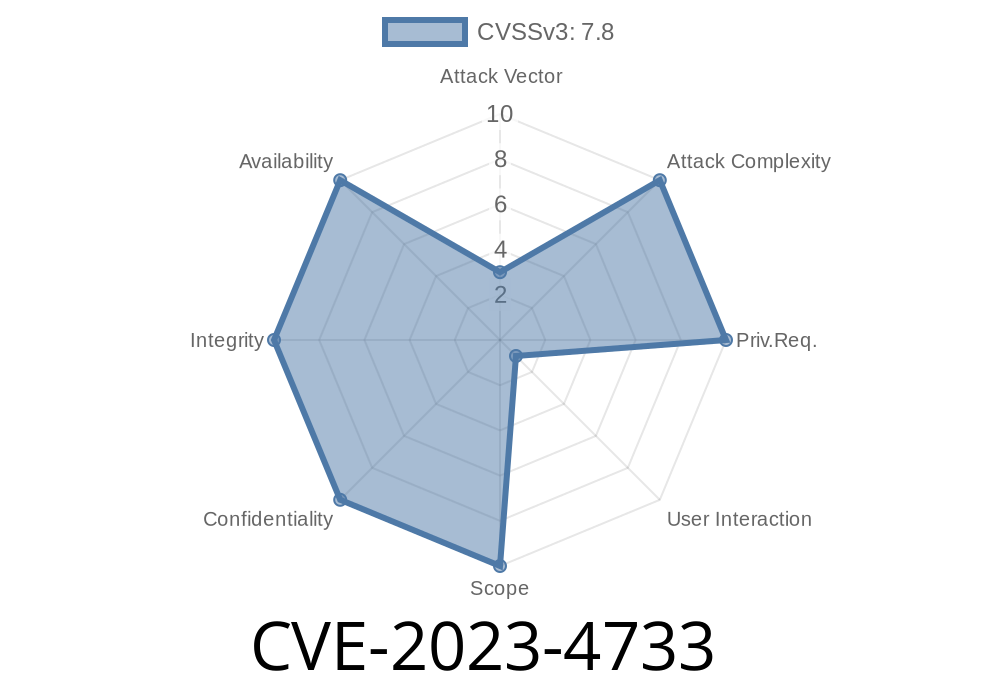
Exploit Impact
- Remote attackers: By tricking someone into opening a malicious file or using a plugin, an attacker could either make Vim crash or (in some cases) run arbitrary code.
- Severity: HIGH — Memory corruption bugs like this are a prime target for attackers, and Vim is often run with user privileges.
Secure Yourself
Fix Available:
Upgrade Vim to version 9..184 or later.
- Latest Vim Releases
References
- NVD: CVE-2023-4733
- GitHub Security Advisory
- Vim Commit Fixing the UAF
The Bottom Line
Even tools as stable as Vim can have risky bugs. Exploiting use-after-free vulnerabilities lets attackers crash apps—or worse, run their code. Always keep your tools up to date and be careful with code from untrusted sources. Stay patched and stay sharp!
---
*Written exclusively for you — if you found this useful, hit share!*
Timeline
Published on: 09/04/2023 14:15:00 UTC
Last modified on: 10/26/2023 00:15:00 UTC