---
If you’re running a WordPress site with WooCommerce, chances are you use plugins to smooth out your customer’s shopping experience. One popular plugin is QuadLayers WooCommerce Checkout Manager, which lets you customize WooCommerce checkout fields. But back in 2023, a major security issue was found in this plugin, tracked as CVE-2023-47681 — and it’s more dangerous than you might think.
Let’s break down what happened, how someone could use this bug to attack, and what you need to do if your site is still at risk.
What is CVE-2023-47681?
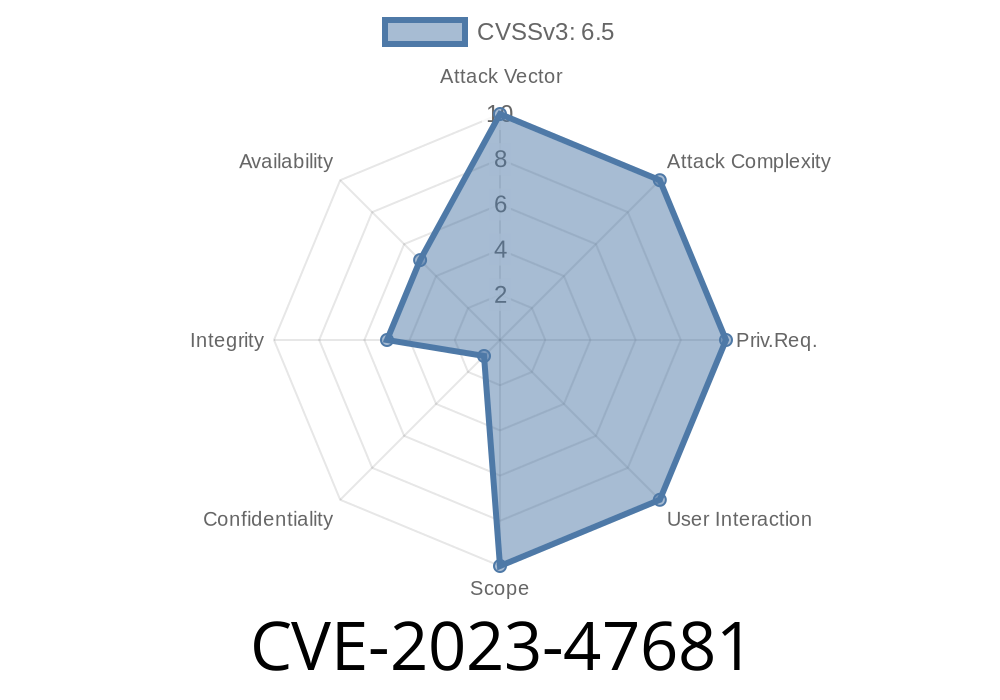
CVE-2023-47681 describes a missing authorization check in QuadLayers WooCommerce Checkout Manager, affecting all versions up to and including 7.3.. This means that some plugin actions didn’t properly verify if a user had the right permissions before letting them run sensitive functions.
In other words, a regular visitor (even someone not logged in) could call plugin functionality that should be reserved for store admins—opening the door for all sorts of attacks.
Reference
- Plugin Vulnerabilities report
- WPScan entry
Technical Details: Missing Authorization
Most WordPress plugins use AJAX requests to let people interact with the site without reloading pages. These requests *should* check if the current user is allowed to perform an action. In WooCommerce Checkout Manager, certain AJAX actions didn’t include proper permission checks.
Here’s a simplified version of what the vulnerable code looked like
add_action('wp_ajax_save_checkout_field', 'save_checkout_field');
add_action('wp_ajax_nopriv_save_checkout_field', 'save_checkout_field'); // <- dangerous!
function save_checkout_field() {
// No permission check!
$field_data = $_POST['field_data'];
// Save custom fields directly
update_option('checkout_fields', $field_data);
echo 'Field saved';
wp_die();
}
There’s no check if the person calling this function is an admin, shop manager, or even logged in! Anyone can POST data to the site’s admin-ajax.php?action=save_checkout_field endpoint and mess with the site's checkout settings.
With the right field data, an attacker could change checkout fields, potentially causing big problems, disabling checkout, injecting malicious code into forms, or extracting sensitive info.
Let’s see what a real attack might look like using a simple script
Attack Step 1: Find a target site using WooCommerce Checkout Manager (<=7.3.).
Attack Step 2: Compose a request to alter checkout fields.
curl -X POST https://victimsite.com/wp-admin/admin-ajax.php \
-d "action=save_checkout_field" \
-d "field_data={\"billing_phone\":{\"label\":\"Phoneploit\",\"type\":\"text\"}}"
What happens?
The victim site’s checkout page will instantly reflect the attacker’s changes—no login or tricks required.
Now imagine using this to
- Add fields asking for sensitive info (scam/phishing)
Fix: What Should You Do?
The fix is straightforward: Update QuadLayers WooCommerce Checkout Manager to the latest secure version. If you can’t update, disable the plugin until you can.
Specifically, the plugin authors fixed this with a permission check
function save_checkout_field() {
if (!current_user_can('manage_woocommerce')) {
wp_die('Not allowed');
}
// continue with saving...
}
If you rely on WooCommerce Checkout Manager, don’t delay—older versions are *exposed*.
To update, go to Plugins > Installed Plugins, find the plugin, and click “Update now.”
Check your site for unknown checkout fields if you ever used the plugin.
- Use a security plugin like Wordfence to scan for vulnerabilities.
References
- Official plugin changelog
- Exploit details on WPVulnDB
- CVE Record
Conclusion
CVE-2023-47681 is a classic example of why plugins must check user permissions for all actions, especially when those actions change how customers interact with your store. If you use QuadLayers WooCommerce Checkout Manager, make updating a top priority to keep your store (and your customers) safe.
*Stay secure, and always keep your plugins up to date!*
Timeline
Published on: 06/19/2024 12:15:11 UTC
Last modified on: 07/02/2024 17:05:07 UTC